A Call for Change in Physical Security
Dark Reading
NOVEMBER 16, 2020
We're at an inflection point. The threats we face are dynamic, emerging, and global. Are you ready?
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 physical-security a-call-for-change-in-physical-security
physical-security a-call-for-change-in-physical-security 
Dark Reading
NOVEMBER 16, 2020
We're at an inflection point. The threats we face are dynamic, emerging, and global. Are you ready?

The Last Watchdog
APRIL 1, 2024
Related: Data privacy vs data security However, this remains a novel concept at most companies. The report, titled “ Embed Cybersecurity And Privacy Everywhere To Secure Your Brand And Business ,” argues for a paradigm shift. Shey Shey: This is something that calls for a maturity assessment.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Krebs on Security
FEBRUARY 26, 2023
But it’s worth revisiting how this group typically got in to targeted companies: By calling employees and tricking them into navigating to a phishing website. Media coverage understandably focused on GoDaddy’s admission that it suffered three different cyberattacks over as many years at the hands of the same hacking group.

Krebs on Security
MAY 9, 2023
Microsoft today released software updates to fix at least four dozen security holes in its Windows operating systems and other software, including patches for two zero-day vulnerabilities that are already being exploited in active attacks. However, as the SANS Internet Storm Center points out , the attack vector for this bug is local.

The Last Watchdog
JULY 24, 2023
Related: Satya Nadella calls for facial recognition regulations Historically, this relationship has been effective from both the user experience and host perspectives; passwords unlocked a world of possibilities, acted as an effective security measure, and were simple to remember. That all changed rather quickly.
Krebs on Security
APRIL 29, 2022
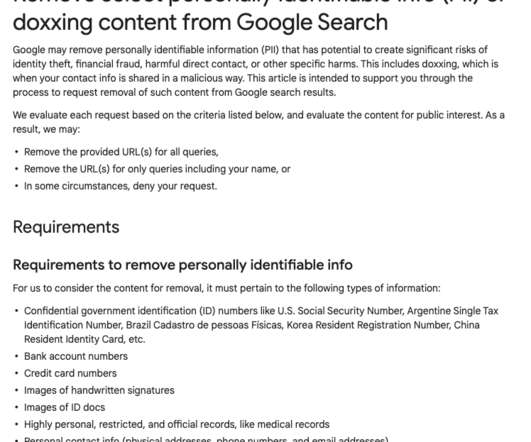
Google said this week it is expanding the types of data people can ask to have removed from search results, to include personal contact information like your phone number, email address or physical address. Google has for years accepted requests to remove certain sensitive data such as bank account or credit card numbers from search results.

The Last Watchdog
AUGUST 8, 2022
Digital twins are a digital representation of reality , either in physical or process form. They might be able to find the most vulnerable spots in the physical structure to stage a terrorist attack. They might be able to find the most vulnerable spots in the physical structure to stage a terrorist attack.

Krebs on Security
AUGUST 30, 2022
A recent spate of SMS phishing attacks from one cybercriminal group has spawned a flurry of breach disclosures from affected companies, which are all struggling to combat the same lingering security threat: The ability of scammers to interact directly with employees through their mobile devices.
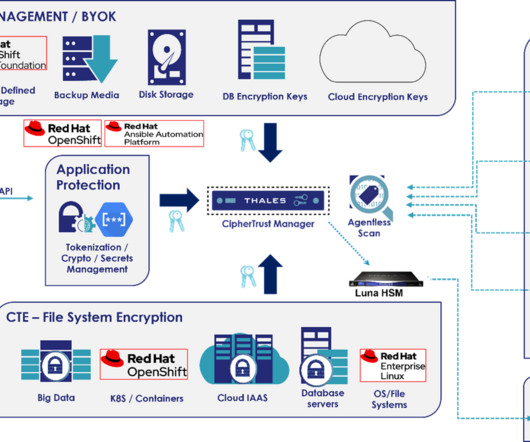
Thales Cloud Protection & Licensing
FEBRUARY 21, 2024
Unfortunately, API attacks are increasing as vectors for security incidents. In this blog, we will explain the unique data security challenges for Telcos and three ways how both Thales and Red Hat can help them protect against future API attacks. In particular, the Telcom industry has fallen victim to several high-profile API attacks.
Krebs on Security
APRIL 6, 2021
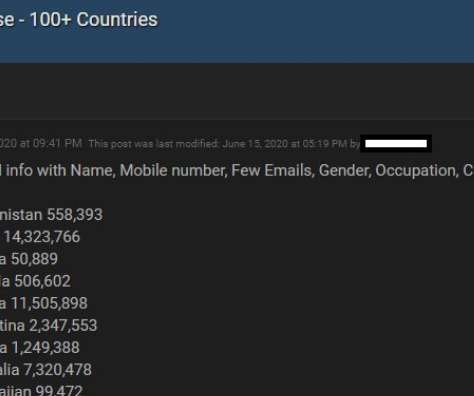
Facebook says the data was collected before 2020 when it changed things to prevent such information from being scraped from profiles. Ne’er-do-wells leaked personal data — including phone numbers — for some 553 million Facebook users this week. billion active monthly users. According to a Jan. According to a Jan.
Krebs on Security
MAY 19, 2021
“On postpaid interfaces, Verizon already has safeguards and T-Mobile does not even support changing numbers online,” the researchers wrote. “On postpaid interfaces, Verizon already has safeguards and T-Mobile does not even support changing numbers online,” the researchers wrote.

Schneier on Security
DECEMBER 15, 2023
In 2016, I wrote about an Internet that affected the world in a direct, physical manner. Arguing with customer service—on chat—for service changes and refunds. But these AIs will interact with the physical world as well, first controlling robots and then having those robots as part of them. This is the easy stuff.

The Last Watchdog
JULY 10, 2023
I had a wide-ranging conversation with NTT Research President & CEO Kazu Gomi about an ambitious initiative called Innovative Optical and Wireless Network ( IOWN ) that aims to develop next-generation networks and computations. In short, the mighty integrated circuit is maxed out. Here are my takeaways.

Krebs on Security
MARCH 16, 2021
SMS text messages were already the weakest link securing just about anything online, mainly because there are tens of thousands of employees at mobile stores who can be tricked or bribed into swapping control over a mobile phone number to someone else. While adding a number, Sakari provides the Letter of Authorization for the user to sign.

eSecurity Planet
APRIL 29, 2024
Meanwhile, a 911 (or 999) call center’s objectives will probably focus on high availability of services and quick response times for callers. The 911 call center would be more concerned about utility disruption (electricity, phone) or a computer system crash that disrupts their ability to dispatch appropriate emergency responses.

Krebs on Security
JANUARY 30, 2024
Multiple trusted sources told KrebsOnSecurity that Sosa/King Bob was a core member of a hacking group behind the 2022 breach at Twilio , a company that provides services for making and receiving text messages and phone calls. Multiple security firms soon assigned the hacking group the nickname “ Scattered Spider.”
IBM Big Data Hub
FEBRUARY 20, 2024
In an era of accelerating climate change , predicting the near-future can yield major benefits. These proactive measures are made possible by evolving technologies designed to help people adapt to the effects of climate change today. But what will the impacts of climate change be in the future?

Security Affairs
FEBRUARY 3, 2020
Cybercriminals are planting so-called “sleepers” in cleaning companies so that they can physically access IT infrastructure and hack them. The alert was launched by a senior p olice officer, cyber criminals are p lanting so-called “sleepers” in cleaning companies so that they can gau physical access IT infrastructure and hack them.

Krebs on Security
SEPTEMBER 28, 2021
When scanned, an AirTag in Lost Mode will present a short message asking the finder to call the owner at at their specified phone number. The vulnerability was discovered and reported to Apple by Bobby Rauch , a security consultant and penetration tester based in Boston. But your average Good Samaritan might not know this.

Krebs on Security
NOVEMBER 22, 2021
Image: Abnormal Security. The brazen approach targeting disgruntled employees was first spotted by threat intelligence firm Abnormal Security , which described what happened after they adopted a fake persona and responded to the proposal in the screenshot above. Please don’t harm Sociogram’s reputation,” Medayedupin pleaded. “I
Krebs on Security
APRIL 28, 2020
You may have heard that today’s phone fraudsters like to use use caller ID spoofing services to make their scam calls seem more believable. Last week, KrebsOnSecurity told the harrowing tale of a reader (a security expert, no less) who tried to turn the tables on his telephonic tormentors and failed spectacularly.

Krebs on Security
AUGUST 12, 2020
Postal Service, the credit bureaus or the Social Security Administration, it’s a good idea to do so for several reasons. Adding multi-factor authentication (MFA) at these various providers (where available) and/or establishing a customer-specific personal identification number (PIN) also can help secure online access.

Security Affairs
FEBRUARY 10, 2022
Verify the call by dialing the customer service line of your mobile carrier. Be aware of any changes in SMS-based connectivity. Use strong multi-factor authentication methods such as biometrics, physical security tokens, or standalone authentication applications to access online accounts.

Krebs on Security
MARCH 8, 2022
“The business services we provide are extremely small and very limited as is our physical presence. . “The business services we provide are extremely small and very limited as is our physical presence. Monroe, La. But on Tuesday the company said it could no longer justify that stance. ru) from the Internet.

Krebs on Security
NOVEMBER 21, 2018
Postal Service just fixed a security weakness that allowed anyone who has an account at usps.com to view account details for some 60 million other users, and in some cases to modify account details on their behalf. Image: USPS.com. The researcher said he informed the USPS about his finding more than a year ago yet never received a response.

Krebs on Security
AUGUST 16, 2018
Terpin alleges that on January 7, 2018, someone requested an unauthorized SIM swap on his AT&T account, causing his phone to go dead and sending all incoming texts and phone calls to a device the attackers controlled. He soon learned his AT&T password had been changed remotely after 11 attempts in AT&T stores had failed.

Krebs on Security
JANUARY 10, 2024
A California man who lost $100,000 in a 2021 SIM-swapping attack is suing the unknown holder of a cryptocurrency wallet that harbors his stolen funds. Experts say the development could make it easier for victims of crypto heists to recover stolen funds through the courts without having to wait years for law enforcement to take notice or help.

Security Affairs
SEPTEMBER 7, 2022
In the digital age, authentication is paramount to a strong security strategy. In the digital age, authentication is paramount to a strong security strategy. As cloud adoption grows exponentially, businesses scramble to amend security strategies to keep their data and end users safe. User Authentication.

Security Affairs
AUGUST 22, 2020
The flaws that could have allowed crooks to modify the amount of money they deposited on their card, so-called Deposit forgery, and make fraudulent cash withdrawals abusing of the new account balance. . An attacker with physical access to internal ATM components may be able to exploit this vulnerability to commit deposit forgery.”
Security Affairs
DECEMBER 23, 2020
Israeli cyber security firm Cellebrite claims that it can decrypt messages from the popular Signal’s messaging app. Israeli security firm Cellebrite has claimed that it can decrypt messages from the Signal highly secure messaging app. To do it, we used Signal’s open-source code and looked for any call to the database.”

The Last Watchdog
JULY 21, 2021
Related: Why PKI will endure as the Internet’s secure core. Yet electronic signatures do have their security limitations. It adds trust and security into each signature, with the ability to easily work with third-party signing workflows such as Adobe, DocuSign, or other signing workflow platforms,” he says.

The Last Watchdog
MAY 17, 2021
In pulling off that milestone hack, Paige Thompson took advantage of CapOne’s lack of focus on cloud security as the banking giant rushed headlong into leveraging Amazon Web Services. A slew of new cloud-security frameworks have gained traction since the Capital One hack. Related: How credential stuffing fuels account takeovers.

IBM Big Data Hub
FEBRUARY 5, 2024
For federal and state governments and agencies, identity is the crux of a robust security implementation. Numerous individuals disclose confidential, personal data to commercial and public entities daily, necessitating that government institutions uphold stringent security measures to protect their assets.

The Last Watchdog
MAY 26, 2021
As a data-driven, security-focused company, we’ve rounded up our top tips inspired by World Password Day to help you improve your password game. But, unfortunately, we live in a world of constant hacking attempts and security breaches. Passwords are now an expected and typical part of our data-driven online lives.

Krebs on Security
JULY 23, 2018
Google has not had any of its 85,000+ employees successfully phished on their work-related accounts since early 2017, when it began requiring all employees to use physical Security Keys in place of passwords and one-time codes, the company told KrebsOnSecurity. A YubiKey Security Key made by Yubico. a mobile device).

Krebs on Security
APRIL 30, 2020
But apparently a number of criminal reshipping services are reporting difficulties due to the increased wait time when calling FedEx or UPS (to divert carded goods that merchants end up shipping to the cardholder’s address instead of to the mule’s). ” Alex Holden , founder and CTO of Hold Security , agreed. .

Armstrong Archives
DECEMBER 18, 2023
This reality has made data security increasingly important, requiring a sea change in the way companies handle their documents. Often, our clients come to us with two concerns: Traditional vs. digital: Even in the digital age, physical documents remain. If your company is among them, you know how frustrating this can be.
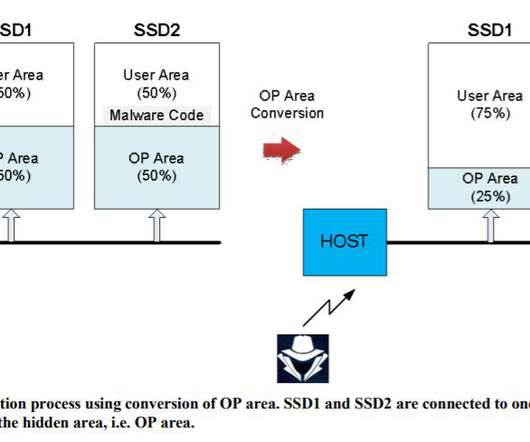
Security Affairs
DECEMBER 31, 2021
Researchers devised a series of attacks against SSDs that could allow to implant malware in a location that is not monitored by security solutions. Korean researchers devised a series of attacks against solid-state drives (SSDs) that could allow to implant malware in specific memory locations bypassing security solutions.

The Last Watchdog
MARCH 17, 2021
Basic research, also called pure research, is aimed at advancing scientific theories unfettered by commercial interests. Ongoing basic research in advanced cryptography concepts is pivotal to putting the brakes on widening cyber risks and ultimately arriving at a level of privacy and security that makes sense.

eSecurity Planet
APRIL 1, 2024
While most issues can be fixed through prompt patching and updating, a few remain unfixed and may require more significant changes to the security stack to block possible attacks. March 22, 2024 Emergency Out-of-Band Windows Server Security Updates Type of vulnerability (or attack): Memory leak. Upgrade versions 7.2.0

Krebs on Security
APRIL 26, 2019
A peer-to-peer (P2P) communications technology built into millions of security cameras and other consumer electronics includes several critical security flaws that expose the devices to eavesdropping, credential theft and remote compromise, new research has found. A Webcam made by HiChip that includes the iLnkP2P software.

The Last Watchdog
FEBRUARY 3, 2020
Department of Homeland Security issued a bulletin calling out Iran’s “robust cyber program,” and cautioning everyone to be prepared for Iran to “conduct operations in the United States.” The drone strike taking out Soleimani itself demonstrated America’s singular ability to potently blend cyber ops with physical firepower.

Security Affairs
FEBRUARY 10, 2022
With this, they deceived the employees of phone stores to obtain duplicate SIM cards and, in this way, have access to the bank’s security confirmation messages. In this way they could operate in online banking and access bank accounts to empty them after receiving security confirmation messages from the banks.”

Security Affairs
MARCH 19, 2022
The alert revealed that in some cases, the AvosLocker ransomware operators targeted victims with phone calls encouraging them to go to the onion site to negotiate and threatens to leak the stolen data online. The advisory was published in coordination with the US Treasury Department and the Financial Crimes Enforcement Network (FinCEN).
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content