New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. As with the rest of the IoT landscape, there's a lot of scope for improvement here and also just like the other IoT posts, it gets very complex for normal people very quickly.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
DECEMBER 21, 2018
2018 was the year of the Internet of Things (IoT), massive attacks and various botnets hit smart devices, These are 5 IoT Security Predictions for 2019. IoT Attacks in 2018. Do the increased attacks mean the industry is becoming accustomed to IoT cyber attacks? Three IoT Attack Avenues for 2019.

Security Affairs
SEPTEMBER 29, 2018
Avast spotted a new IoT botnet, tracked as Torii, that appears much more sophisticated and stealth of the numerous Mirai variants previously analyzed. Security researchers spotted a new IoT botnet, tracked as Torii, that appears much more sophisticated and stealth of the numerous Mirai variants previously analyzed. Pierluigi Paganini.

Security Affairs
JULY 24, 2018
As an example, a specific Android TV device was also found to ship in this condition.” ” The binary establishes a connection to the C&C server, then scans processes running on the compromised device and attempts to kill any that are running the CoinHive script that could be mining Monero. Pierluigi Paganini.
Security Affairs
SEPTEMBER 1, 2021
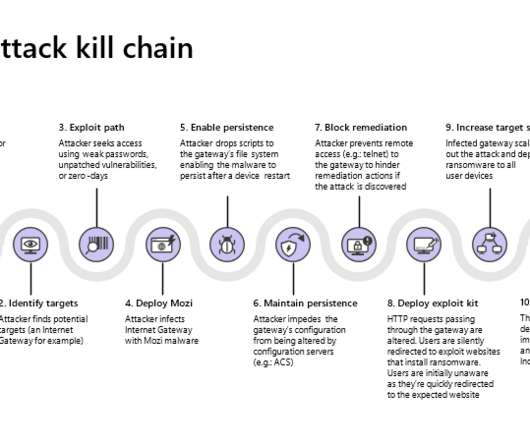
Mozi is an IoT botnet that borrows the code from Mirai variants and the Gafgyt malware , it appeared on the threat landscape in late 2019. Microsoft Security Threat Intelligence Center and Section 52 at Azure Defender for IoT have monitored a new evolution of the threat that extent the list of targets.
Security Affairs
OCTOBER 7, 2020
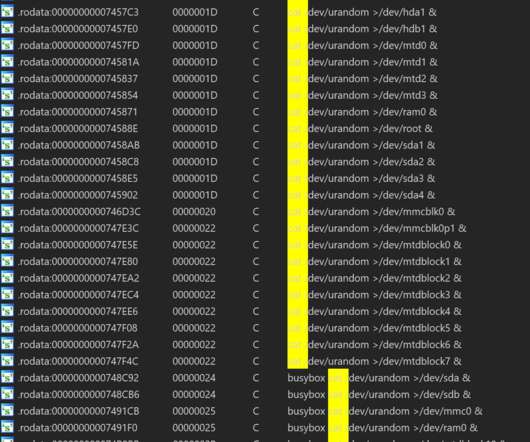
Researchers from from Netlab, the network security division of Chinese tech giant Qihoo 360, have discovered a new botnet, tracked as HEH, that contains the code to wipe all data from infected systems, such as routers, IoT devices, and servers.

Security Affairs
SEPTEMBER 10, 2018
Thousands of unpatched MikroTik Routers are involved in new cryptocurrency mining campaigns. Thousands of unpatched devices are mining for cryptocurrency at the moment. Now the researcher Troy Mursch noticed that the infected MikroTik routers from the latest campaign open a websockets tunnel to a web browser mining script.

Security Affairs
JULY 12, 2022
Researchers investigated cloud-based cryptocurrency mining attacks targeting GitHub Actions and Azure VMs. Researchers from Trend Micro published a report that details cloud-based cryptocurrency mining attacks targeting GitHub Actions and Azure VMs and the threat actors behind them. SecurityAffairs – hacking, cryptocurrency mining).
eSecurity Planet
SEPTEMBER 15, 2022
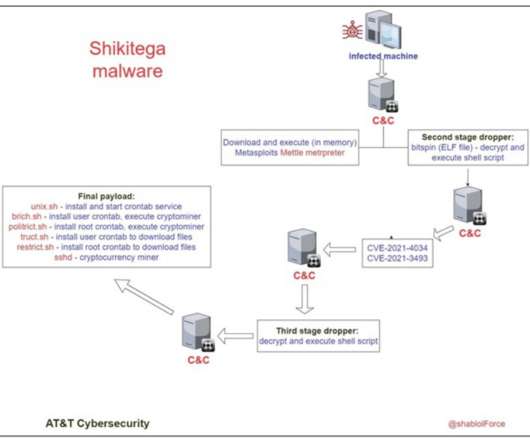
Each module focuses on a unique task, for example, downloading and executing Metasploit meterpreter, escalating privileges on the targeted systems, and maintaining persistence. The infamous XMRig mines Monero cryptocurrency that is known to be anonymity-focused, as it’s particularly hard to trace back.

Security Affairs
SEPTEMBER 20, 2018
Sustes Malware doesn’t infect victims by itself, but it is spread via brute-force activities with special focus on IoT and Linux servers. Sustes Malware doesn’t infect victims by itself (it’s not a worm) but it is spread over the exploitation and brute-force activities with special focus on IoT and Linux servers.

The Security Ledger
DECEMBER 18, 2019
. » Related Stories Episode 170: Cyber Monday is for Hackers Spotlight Podcast: RSA President Rohit Ghai warns Digital Transformation is magnifying Enterprise Risk Spotlight Podcast: Two Decades On, Trusted Computing Group tackles IoT Insecurity. One industry that is unlikely to be phased by the new requirements, however, is healthcare.

The Last Watchdog
SEPTEMBER 11, 2019
Rising implementations of cloud services and IoT systems, not to mention the arrival of 5G, has quickened the pace of software development and multiplied data handling complexities. Stuck in a rut Enter SOAR, which takes well-understood data mining and business intelligence analytics methodologies and applies them to cybersecurity.

ARMA International
SEPTEMBER 13, 2021
Gartner (2021) has two related definitions: Digital Transformation: “can refer to anything from IT modernization (for example, cloud computing), to digital optimization, to the invention of new digital business models.” For example, IBM, Amazon Web Service, Microsoft, and Google offer AIaaS.

Security Affairs
JULY 13, 2019
” Avast researchers also observed crooks using DNS hijacking to deliver crypto mining scripts to users’ browsers. In some cases the router is reconfigured to use rogue DNS servers, which redirect victims to phishing pages that closely look like real online banking sites. Most recently, Netflix became a popular domain for DNS hijackers.”

erwin
JUNE 11, 2020
With tools such as Artificial Intelligence, Machine Learning, and Data Mining, businesses and organizations can collate and analyze large amounts of data reliably and more efficiently. Great examples are BMW Mini , Comfort Keepers, and Teleflora. Transforming Industries with Data Intelligence. Enhance customer experience.

The Last Watchdog
FEBRUARY 6, 2019
It’s now commonplace for high-resolution video cams to feed endless streams of image data into increasingly intelligent data mining software. Other obvious use cases would be to provide real-time authentication to access autonomous vehicles or to control IoT devices in a smart home.

eSecurity Planet
OCTOBER 27, 2021
While many consumer devices today come with standard antivirus software, a growing number of internet-enabled systems, like IoT devices , are being manufactured with light security. Detection Using Machine Learning and Data Mining.
Krebs on Security
FEBRUARY 24, 2020
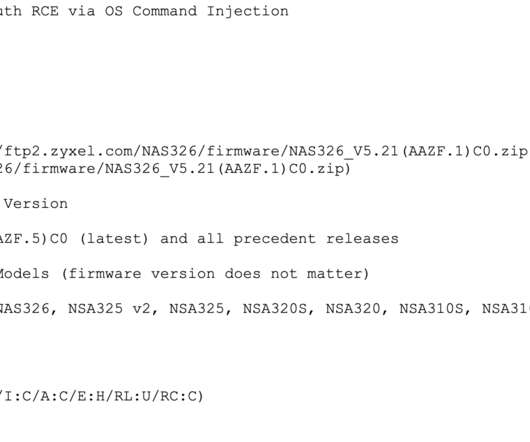
While in many respects the class of vulnerability addressed in this story is depressingly common among Internet of Things (IoT) devices, the flaw is notable because it has attracted the interest of groups specializing in deploying ransomware at scale. EMOTET GOES IOT? KrebsOnSecurity first learned about the flaw on Feb. PARTIAL PATCH.

ARMA International
SEPTEMBER 22, 2021
For example, once a health record has met the regulatory requirements, the record can be anonymized and kept for years for such purposes as medical research and predictive analytics. See Table 1 listing some common examples of the “art of the possible. See Table 2 for a few examples. Auto-classification.

ForAllSecure
APRIL 30, 2020
He shares a particular example: e-commerce couldn’t have happened without fundamental crypto libraries, such as TLS and SSL. Gary McGraw is a good friend of mine and I've talked to him about software security for almost two decades now. David Brumley: The set of people who haven't actually been that enthusiastic so far is IoT.

ForAllSecure
APRIL 30, 2020
He shares a particular example: e-commerce couldn’t have happened without fundamental crypto libraries, such as TLS and SSL. Gary McGraw is a good friend of mine and I've talked to him about software security for almost two decades now. David Brumley: The set of people who haven't actually been that enthusiastic so far is IoT.

ForAllSecure
APRIL 30, 2020
He shares a particular example: e-commerce couldn’t have happened without fundamental crypto libraries, such as TLS and SSL. Gary McGraw is a good friend of mine and I've talked to him about software security for almost two decades now. David Brumley: The set of people who haven't actually been that enthusiastic so far is IoT.
Security Affairs
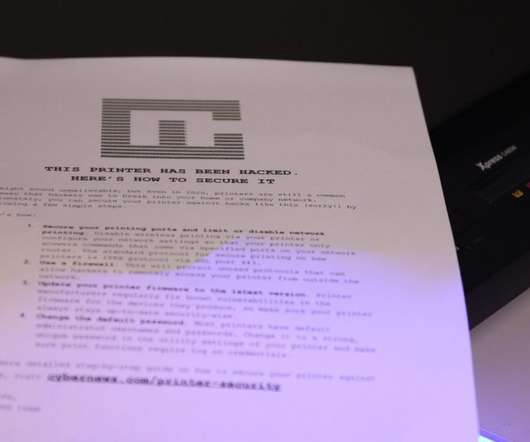
AUGUST 27, 2020
To perform the experiment, we used Internet of Things (IoT) search engines to search for open devices that utilized common printer ports and protocols. To find out how many printers were on the menu for our experiment, we searched for IP addresses with open ports on specialized IoT search engines, such as Shodan and Censys.

ForAllSecure
JUNE 16, 2021
So, for this episode I probably need to set the landscape API as an example of where I think I understand something, but then I come to find out there's a lot more to it. So, maybe a concrete real world example is needed. Kent: I like to use Uber as the example when I talk about this right. There's always a lot more, right.

ForAllSecure
JUNE 16, 2021
So, for this episode I probably need to set the landscape API as an example of where I think I understand something, but then I come to find out there's a lot more to it. So, maybe a concrete real world example is needed. Kent: I like to use Uber as the example when I talk about this right. There's always a lot more, right.

Troy Hunt
DECEMBER 19, 2017
Incidentally, do note the inclusion of things like mobile device ID, IoT data and trade union memberships; many people wouldn't normally think of these as "personal data", but once you consider the potential for abuse, it makes a lot more sense.) Use of Personal Data Should be Transparent and Easy to Understand.

Bill Schmarzo - Dell EMC
FEBRUARY 14, 2018
For example, Amazon is vertically integrating the grocery industry with their recent acquisition of Whole Foods. for examples of how Amazon is leveraging customer insights to vertically integrate the grocery industry. Customer experiences are unsatisfactory. Customer outcomes are questionable, or are downright wrong.

Thales Cloud Protection & Licensing
JUNE 27, 2022
From smart cities and digital IDs to open government and better governance, the Cloud, Big Data, IoT and Artificial Intelligence have enabled a wide range of digital government initiatives. For example, 91% of government agency officials in the United States said they were “ innovating with urgency ” after the pandemic. Government.

CGI
NOVEMBER 9, 2015
IoT – It’s more than just connecting a sensor. There is a growing recognition by business leaders and analysts that there is more to the Internet of Things (IoT) than just connecting a remote device or sensor to an application to monitor a temperature or alarm. p.butler@cgi.com. Mon, 11/09/2015 - 04:30.

Bill Schmarzo - Dell EMC
MARCH 5, 2018
Note: throughout this blog, when I use the term “artificial intelligence,” I mean that to include other advanced analytics such as deep learning, machine learning (supervised, unsupervised, reinforcement), data mining, predictive analytics, and statistics (see Figure 1). Figure 1: The Evolution of AI, ML and DL (Source: Nvidia ).

eSecurity Planet
APRIL 7, 2023
IoT (printers, IP phones, security cameras, etc.) For example, if deploying the eyeSight module, no additional licenses may be required, but dedicated virtual hardware may need to be deployed for the Command Center and Monitoring Sensors. Agents Forescout Platform is an agentless solution.

The Last Watchdog
MARCH 17, 2020
For example, when you click to Amazon.com, two different cryptographic keys are used: a public key and a private key. In fact, there is a potential for advanced encryption systems, in general, to crack open a whole new world of cloud computing and IoT-enabled services. More data is coming as 5G and IoT usage climbs.

IBM Big Data Hub
MAY 17, 2023
Additionally, DaaS has the potential to leverage smart technologies such as IoT, sensors, 5G, edge analytics and machine learning to improve the monitoring and visualization of assets operations. The flexibility of DaaS in offering a multiplicity of data collection services for different industry use cases makes it unique.

ForAllSecure
SEPTEMBER 21, 2021
They discuss how software and IoT companies can avoid becoming the next Black Mirror episode and share resources that can help survivors (and those who want to help them) deal with the technology issues that can be associated with technologically facilitated abuse. There are literally dozens of other examples. What about social media?

Bill Schmarzo - Dell EMC
MARCH 5, 2018
Note: throughout this blog, when I use the term “artificial intelligence,” I mean that to include other advanced analytics such as deep learning, machine learning (supervised, unsupervised, reinforcement), data mining, predictive analytics, and statistics (see Figure 1). Figure 1: The Evolution of AI, ML and DL (Source: Nvidia ).

IBM Big Data Hub
JUNE 30, 2023
Many industries depend on CMMS to improve asset and workflow visibility, streamline operations and maintenance, manage mobile field workforces, and ensure compliance in, for example, auditing and health, safety and environment reporting. What is EAM and what does it do?

eSecurity Planet
JULY 25, 2023
Examples include baiting, pretexting, and impersonation. Cryptojacking : Unauthorized use of a computer’s processing power to mine cryptocurrencies. Social engineering attacks: These involve manipulating individuals to gain unauthorized access to sensitive information or systems.

ForAllSecure
NOVEMBER 2, 2021
Vamosi: The war dialing example at the beginning, hanging up when the other end answers would be more like a Surface Scan or a port scan, where you just check to see if the port is open. For example, for the IAS research I mentioned before scanning port 80 was sufficient because like most IIS servers will listen on port 80.

ForAllSecure
AUGUST 2, 2022
And, there’s thirty more villages including Girls Hack Village, the Voting Machine Hacking village, the IoT Village, and the Bio Hacking village. So in this episode, I'm going to share some of the conversations I've had with leaders of some of those more established villages over the last 50 episodes of the hacker mine.

eDiscovery Daily
MARCH 29, 2018
I think the point though not to lose sight of is that we still have a large task in handling more traditional forms of documents and ESI, and that these may still be the “low hanging fruit” in many, many cases without worrying about exotic forms of IOT that may or may not be relevant. Where are mining operations?

Bill Schmarzo - Dell EMC
JANUARY 29, 2018
As a standard operating practice, football front offices should apply Machine Learning to mine the large body of football game data to identify those “known unknowns” and “unknown unknowns” relationships buried in the data. Trap: Anchoring Basis. Figure 3: Human Design Making. Trap: Framing Effect. yards per completed pass in the first half.

ForAllSecure
MAY 13, 2022
For example, in 2009, the Obama administration provided financial incentives to utilities in the United States. Vamosi: But as someone who wrote a book questioning the security of our mass produced IoT devices, I wonder why no one bothered to test and certify these devices before they were installed? It's mine.

Troy Hunt
APRIL 15, 2019
For example, there was VTech back in 2015 who leaked millions of kids' info after they registered with "smart" tablets. Wearco produces "mining consumables". It's the little things that keep popping up, for example the language and grammar in the aforementioned user manual. And why is the opening sentence of the doc so.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content