New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. As with the rest of the IoT landscape, there's a lot of scope for improvement here and also just like the other IoT posts, it gets very complex for normal people very quickly.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
DECEMBER 21, 2018
2018 was the year of the Internet of Things (IoT), massive attacks and various botnets hit smart devices, These are 5 IoT Security Predictions for 2019. IoT Attacks in 2018. Do the increased attacks mean the industry is becoming accustomed to IoT cyber attacks? Three IoT Attack Avenues for 2019.
Security Affairs
SEPTEMBER 1, 2021
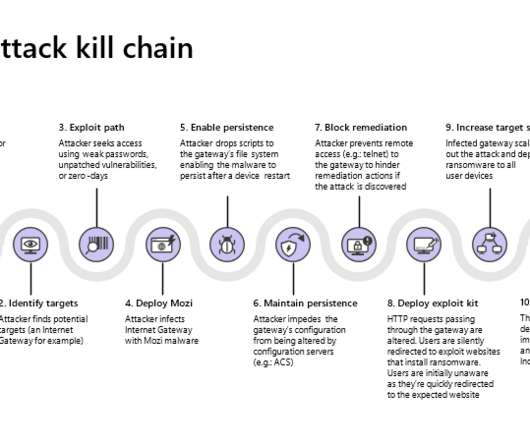
Mozi is an IoT botnet that borrows the code from Mirai variants and the Gafgyt malware , it appeared on the threat landscape in late 2019. Earlier in August, Microsoft researchers reported that the Mozi botnet was improved by implementing news capabilities to target network gateways manufactured by Netgear, Huawei, and ZTE.

eSecurity Planet
OCTOBER 27, 2021
While many consumer devices today come with standard antivirus software, a growing number of internet-enabled systems, like IoT devices , are being manufactured with light security. Detection Using Machine Learning and Data Mining.

ARMA International
SEPTEMBER 13, 2021
Gartner (2021) has two related definitions: Digital Transformation: “can refer to anything from IT modernization (for example, cloud computing), to digital optimization, to the invention of new digital business models.” DRM is used by publishers, manufacturers and IP owners for digital content and device monitoring” (Techopedia 2021).

ForAllSecure
APRIL 30, 2020
He shares a particular example: e-commerce couldn’t have happened without fundamental crypto libraries, such as TLS and SSL. Gary McGraw is a good friend of mine and I've talked to him about software security for almost two decades now. David Brumley: The set of people who haven't actually been that enthusiastic so far is IoT.
Let's personalize your content