Morgan Stanley's Hard Drive Destruction Investment Failure
Data Breach Today
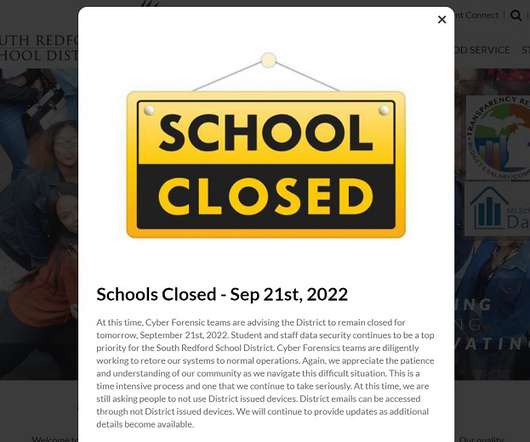
SEPTEMBER 22, 2022
$35 Million Fine From Securities and Exchange Commission Covers 5 Years of Mishaps Financial services giant Morgan Stanley will pay a $35 million fine to settle U.S. Securities and Exchange Commission charges that it failed to comply with rules requiring it to safeguard customer data as well as ensure it is disposed of properly.






































Let's personalize your content