Alleged Member of Neo-Nazi Swatting Group Charged
Krebs on Security
JANUARY 10, 2020
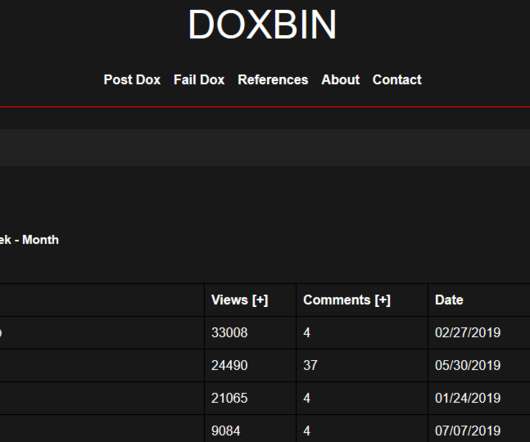
In July 2018, KrebsOnSecurity published the story Neo-Nazi Swatters Target Dozens of Journalists , which detailed the activities of a loose-knit group of individuals who had targeted hundreds of individuals for swatting attacks, including federal judges, corporate executives and almost three-dozen journalists (myself included). since 2017.








































Let's personalize your content