NEW TECH: DigiCert Document Signing Manager leverages PKI to advance electronic signatures
The Last Watchdog
JULY 21, 2021
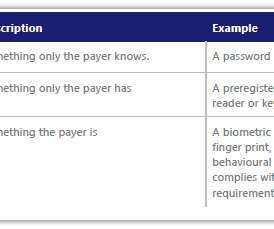
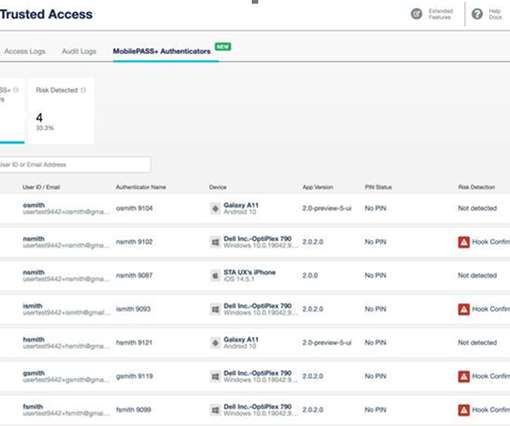
Most of us, by now, take electronic signatures for granted. Yet electronic signatures do have their security limitations. And PKI , of course, is the behind-the-scenes authentication and encryption framework on which the Internet is built. Related: Why PKI will endure as the Internet’s secure core.





































Let's personalize your content