Mine, Mine, All Mine
John Battelle's Searchblog
APRIL 19, 2024
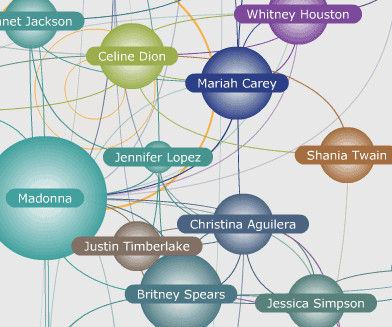
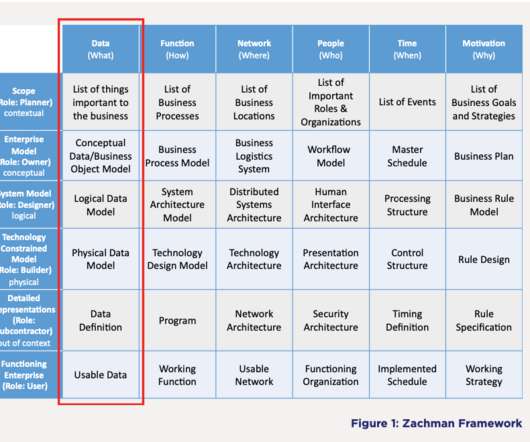
Author’s musical preferences not included… No Longer Mine When I write, I like to listen to music. I Want To Mine This raises much larger issues about how – or whether – we are intelligently architecting the possibilities that define our interaction with knowledge. The original MusicPlasma interface.





























Let's personalize your content