The IoT Cybersecurity Act of 2020: Implications for Devices
eSecurity Planet
JANUARY 22, 2021
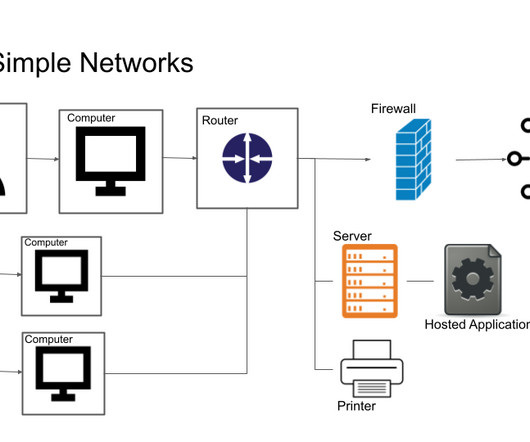
billion Internet of Things (IoT) devices. As more information about IoT device vulnerabilities is published, the pressure on industry and government authorities to enhance security standards might be reaching a tipping point. government, standards will not apply to the IoT market at-large. Implications for IoT devices.















































Let's personalize your content