Cloud Security Threats for 2021
Dark Reading
DECEMBER 3, 2020
Most of these issues can be remediated, but many users and administrators don't find out about them until it's too late.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cloud-security cloud-security-threats-for-2021
cloud-security cloud-security-threats-for-2021 
Dark Reading
DECEMBER 3, 2020
Most of these issues can be remediated, but many users and administrators don't find out about them until it's too late.

eSecurity Planet
JANUARY 18, 2024
Cloud storage is a cloud computing model that allows data storage on remote servers operated by a service provider, accessible via internet connections. It excels in remote access, scalability, and security, with distributed storage options and privacy adherence capabilities.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
AUGUST 13, 2023
The popular service, ChatGPT , is based on OpenAI ’s LLM, which taps into everything available across the Internet through 2021, plus anything a user cares to feed into it. Island supplies an advanced web browser security solution. Threat intelligence vendor Cybersixgill for instance launched Cybersixgill IQ at Black Hat.
Thales Cloud Protection & Licensing
NOVEMBER 13, 2023
Defending Financial Services Against Fraud in a Shifting Cyber Landscape sparsh Tue, 11/14/2023 - 05:05 As we approach International Fraud Awareness Week during 12-18 November 2023, taking stock of the evolving threat landscape and the vulnerabilities that financial services organizations face is crucial. billion annually.
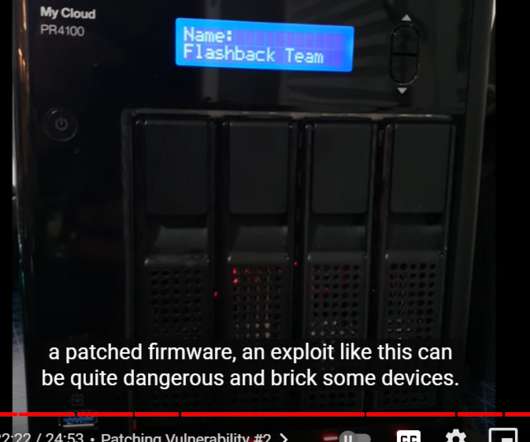
Krebs on Security
JULY 2, 2021
Nevertheless, in February 2021, the duo published this detailed YouTube video from February , which documents how they discovered a chain of weaknesses that allows an attacker to remotely update a vulnerable device’s firmware with a malicious backdoor — using a low-privileged user account that has a blank password.

eSecurity Planet
SEPTEMBER 10, 2021
From the very beginning of the cloud computing era, security has been the biggest concern among enterprises considering the public cloud. In addition, 95 percent of survey respondents confirmed that they are extremely to moderately concerned about public cloud security. What is cloud security?

The Last Watchdog
DECEMBER 21, 2021
Cloud hosted email services have come into wide use as the go-to communication and collaboration work tools for businesses far and wide. Related: Weaponized email endures as top threat. From a security standpoint, this translates into a massive exposure to cyber attacks, leaving many doors open to malware – especially weaponized email.

Security Affairs
SEPTEMBER 12, 2022
Google completed the acquisition of the threat intelligence firm Mandiant, the IT giant will pay $5.4 billion acquisition of threat intelligence firm Mandiant. Mandiant is considered a leading cyber security firm, in 2013 FireEye acquired it, but FireEye separated Mandiant Solutions in 2021 as part of a $1.2

Krebs on Security
JUNE 8, 2021
Microsoft today released another round of security updates for Windows operating systems and supported software, including fixes for six zero-day bugs that malicious hackers already are exploiting in active attacks. June’s Patch Tuesday addresses just 49 security holes — about half the normal number of vulnerabilities lately.
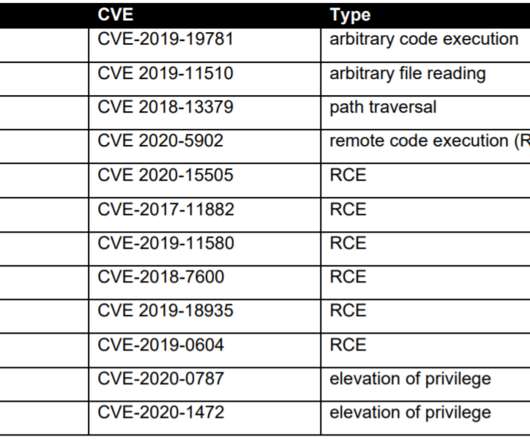
Security Affairs
JULY 28, 2021
A joint report published by US, UK, and Australian cyber security agencies warns of the top routinely exploited vulnerabilities in 2020. Cybersecurity and Infrastructure Security Agency (CISA), the Australian Cyber Security Centre (ACSC), the United Kingdom’s National Cyber Security Centre (NCSC), and the U.S.

Thales Cloud Protection & Licensing
MARCH 23, 2022
Shifting Risk and Business Environment Demand creates a Shift in Security Strategies. The 2022 Thales Data Threat Report, based on data from a survey of almost 2,800 respondents from 17 countries across the globe, illustrates these trends and changes. Malware and accidental human error are the biggest security threats.

Thales Cloud Protection & Licensing
MAY 8, 2023
Thales 2023 Data Threat Report: Sovereignty, Transformation, and Global Challenges madhav Tue, 05/09/2023 - 05:30 Despite the economic and geopolitical instability in 2022, enterprises continued to invest in their operations and digital transformation. However, the reported threat sources have been changing.

eSecurity Planet
JUNE 7, 2023
IT security buyers are consolidating vendors at an overwhelming rate, according to a speaker at this week’s Gartner Security & Risk Management Summit. ” Security Products Merge Into Platforms As part of that trend, security products are consolidating too, MacDonald said.
Thales Cloud Protection & Licensing
SEPTEMBER 11, 2023
Thales 2023 Data Threat Report: The Increased Telco Cybersecurity Challenges in the 5G Era madhav Tue, 09/12/2023 - 05:15 Telecommunications firms have always faced a unique set of security challenges. Infrastructure extends to multiple cloud platforms and applications and the increased volume of connected IoT devices.
Security Affairs
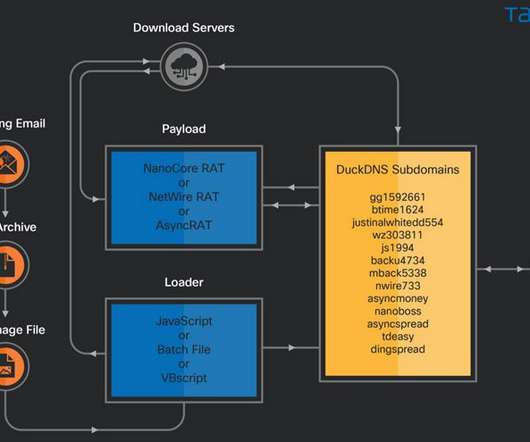
JANUARY 13, 2022
Threat actors are actively abusing cloud services from Amazon and Microsoft to deliver RATs such as Nanocore , Netwire , and AsyncRAT. The malware campaign was spotted by Cisco Talos in October 2021, most of the victims were located in the United States, Italy and Singapore. SecurityAffairs – hacking, cloud services).

The Last Watchdog
SEPTEMBER 6, 2022
Network security has been radically altered, two-plus years into the global pandemic. They must take into account a widely scattered workforce and somehow comprehensively mitigate new and evolving cyber threats. Acohido is dedicated to fostering public awareness about how to make the Internet as private and secure as it ought to be. (LW
eSecurity Planet
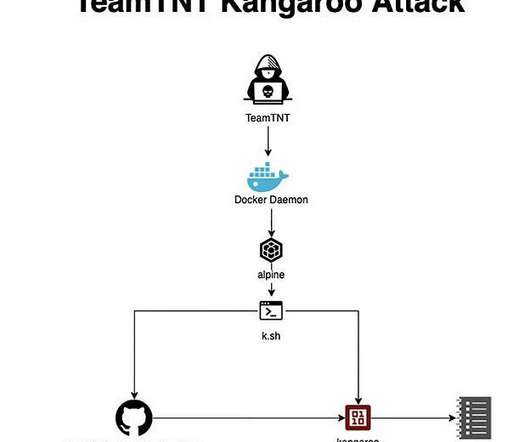
SEPTEMBER 21, 2022
A retired threat actor has returned with new attacks aimed at the cloud, containers – and encryption keys. These cybercriminals are known for their creativity and ability to target cloud environments, as they introduced new techniques in 2020 that hadn’t been seen before. Also read: Top Container Security Solutions.

Security Affairs
OCTOBER 29, 2021
The US NSA and CISA published a security advisory to warn about threat actors compromising 5G networks via cloud infrastructure. The report is part of a four-part series that was built on the ESF Potential Threat Vectors to 5G Infrastructure white paper that was released by the US agencies in May 2021.The

The Last Watchdog
MARCH 31, 2021
The start of 2021 brings forth a cyber security crossroads. From the known compromise vectors to the most recent threats, hackers are constantly on the lookout for new strategies to bypass IT notice, out maneuver defense setups, and take advantage of new weaknesses. Many employees don’t have a wide range of security protections.
eSecurity Planet
NOVEMBER 18, 2021
New cybersecurity buzzwords are always in abundance at the Gartner Security & Risk Management Summit, and the concepts that took center stage this week, like cybersecurity mesh and decentralized identity, seem well suited for new threats that have exploded onto the scene in the last year. A distributed identity fabric.

Thales Cloud Protection & Licensing
JULY 10, 2023
Managing Complexity, Data Control, and Sovereignty in the Cloud madhav Tue, 07/11/2023 - 05:08 55% of Organizations Feel Managing and Securing Cloud Data is Becoming More Complex Cloud computing has played a transformative role in some of the most significant technological advances of the past two years.
Security Affairs
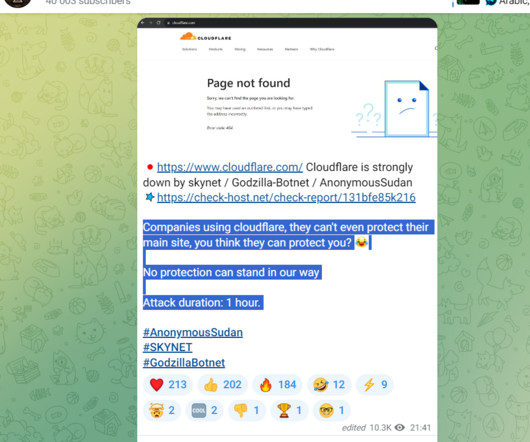
NOVEMBER 10, 2023
However, some security researchers believe that Anonymous Sudan is a sub-group of the pro-Russian threat group Killnet. Threat actors relied on access to multiple virtual private servers (VPS) in conjunction with rented cloud infrastructure, open proxies, and DDoS tools.

eSecurity Planet
OCTOBER 8, 2021
And like other old-guard companies, ESET knows it needs to innovate to stay competitive, which the company has done with its cloud-based endpoint protection platform, ESET PROTECT. Administrators can quickly deploy ESET and configure policies to meet network security objectives through the cloud-based management console.

eSecurity Planet
JUNE 14, 2022
Laminar raised $67 million earlier this month, which came after a $37 million round in November 2021. They saw an opportunity in the public cloud data security market. They saw an opportunity in the public cloud data security market. Also read: CNAP Platforms: The Next Evolution of Cloud Security.
Security Affairs
OCTOBER 25, 2021
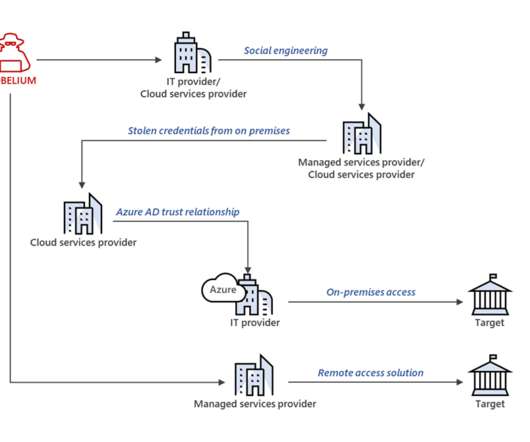
Russia-linked Nobelium APT group has breached at least 14 managed service providers (MSPs) and cloud service providers since May 2021. The campaign confirms that Russia-linked threat actors are trying to gain long-term, systematic access to multiple points in the technology supply chain to carry out cyberespionage activities. .

eSecurity Planet
SEPTEMBER 24, 2021
Rapid7 combines threat intelligence , security research, data collection, and analytics in its comprehensive Insight platform, but how does its detection and response solution – InsightIDR – compare to other cybersecurity solutions? This article looks at the top three benefits of the Rapid7 InisightIDR solution.

Thales Cloud Protection & Licensing
MAY 23, 2022
Access Management is Essential for Strengthening OT Security. These systems are connected to and managed from the cloud to fine-tune performance, provide data analytics, and ensure the integrity of critical infrastructure across all sectors. The threat landscape. Tue, 05/24/2022 - 06:11. Attacks against the food sector.

Thales Cloud Protection & Licensing
JANUARY 24, 2022
Data Privacy and Security: It Takes Two to Tango. The goal of Data Privacy Week, celebrated between January 24 – 28, is to spread awareness about online privacy and educate citizens on how to manage their personal information and keep it secure. However, with technology innovation comes new risks, security challenges and threats.
Security Affairs
APRIL 1, 2024
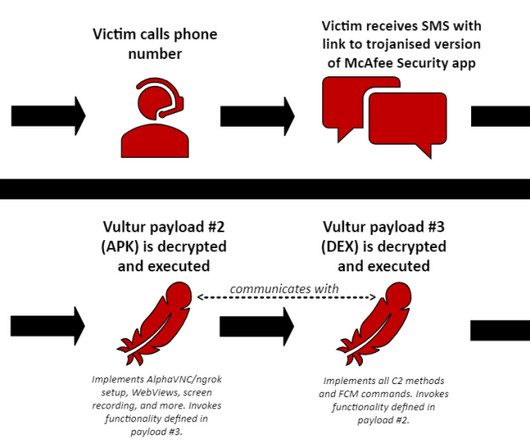
Vultur was first spotted in late March 2021, it gains full visibility on victims’ devices via VNC (Virtual Network Computing) implementation taken from AlphaVNC. In July 2021, ThreatFabric researchers discovered the Android version of Vultur, which uses screen recording and keylogging to capture login credentials.

Thales Cloud Protection & Licensing
JANUARY 17, 2022
It is your data in their cloud, make sure it is secure! For modern organizations, digital transformation is a vital imperative, and cloud services offer a proven path to thrive in the digital economy. It is your data in their cloud after all - and you need to make sure your most valuable assets are secure!

Thales Cloud Protection & Licensing
FEBRUARY 17, 2022
Best Practices for a Modern Cloud Security Architecture. Partnering with Thales, Red Hat takes the latest in open source innovation and crafts that into secure, enterprise-ready solutions. I was invited to the 2021 Thales Cloud Security Summit to discuss modern cloud security architecture with Alex Hanway.
Thales Cloud Protection & Licensing
APRIL 22, 2022
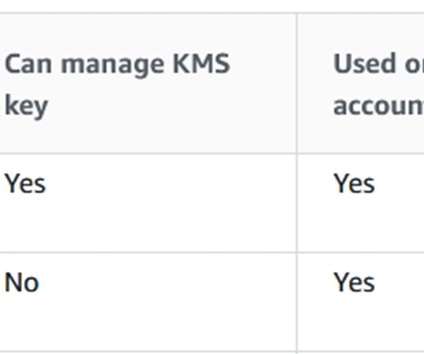
So You Think You Are Protected With Cloud Native Encryption? According to industry surveys, like the IBM 2021 Data Breach Investigations Report, a very high percentage of data breaches occur because attackers are abusing system privileges. Cloud customers are responsible for the security and protection of data stored in the cloud.

Thales Cloud Protection & Licensing
MAY 16, 2022
In a previous blog post, I discussed how The White House Executive Order issued on May 12, 2021 laid out new, rigorous government cyber security standards for federal agencies. Control – Insulate and layer access against digital threats like ransomware attacks. Cloud Security. Cloud Security.

eSecurity Planet
AUGUST 5, 2021
Two of the largest government security agencies are laying out the key cyberthreats to Kubernetes, the popular platform for orchestrating and managing containers, and ways to harden the open-source tool against attacks. ” Further reading: Top Container Security Solutions for 2021. Three Threat Areas.

Security Affairs
NOVEMBER 22, 2023
Cybersecurity and Infrastructure Security Agency (CISA) added Looney Tunables Linux vulnerability to its Known Exploited Vulnerabilities (KEV) catalog. Researchers at Qualys’ Threat Research Unit disclosed the vulnerability, also named Looney Tunables, last week and published a PoC exploit. reads the advisory.

Security Affairs
MARCH 30, 2021
VMware has published security updates to address multiple vulnerabilities in VMware vRealize Operations that could allow threat actors to steal admin credentials from vulnerable installs. The vulnerability was reported to VMware by security researcher Egor Dimitrenko from Positive Technologies. Pierluigi Paganini.

Security Affairs
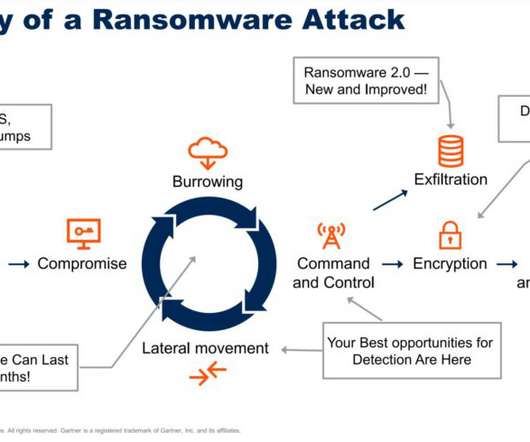
FEBRUARY 12, 2022
and Australia have published a joint advisory warning of an increased globalised threat of ransomware worldwide in 2021. “Ransomware tactics and techniques continued to evolve in 2021, which demonstrates ransomware threat actors’ growing technological sophistication and an increased ransomware threat to organizations globally.”

Security Affairs
SEPTEMBER 9, 2021
Evidence collected by the experts suggests that the campaign began on July 25, 2021, threat actors used a large set of open-source tools in the attacks. Threat actors leverage open-source tools to avoid detection and make hard the attribution of the attacks. ” reads the analysis published by AT&T.

eSecurity Planet
DECEMBER 28, 2020
The movement to the cloud means access to data anywhere, enhanced data recovery, flexibility for collaboration, and less of a burden on IT staff. But, while cloud providers boast that their storage services — or “buckets” — offer added application security , they have also consistently proven vulnerable.
eSecurity Planet
JANUARY 20, 2022
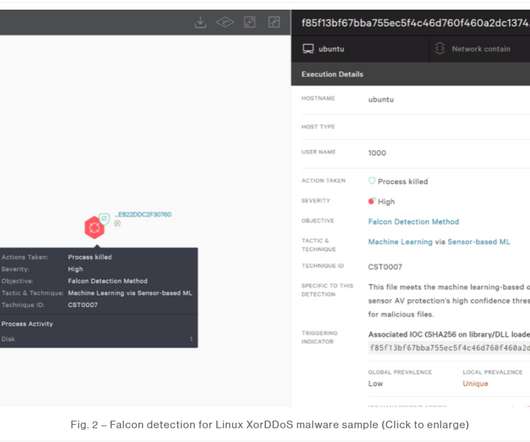
Incidents of malware targeting Linux-based Internet of Things (IoT) devices jumped by more than a third in 2021, with three malware families the primary drivers behind the increase. There was a 10-fold increase in the number of samples of Mozi found in the wild, Mihai Maganu, a threat researcher at CrowdStrike, wrote in a blog post.

Security Affairs
JANUARY 23, 2024
Cybersecurity and Infrastructure Security Agency (CISA) adds VMware vCenter Server Out-of-Bounds Write bug to its Known Exploited Vulnerabilities catalog. vCenter Server is a critical component in VMware virtualization and cloud computing software suite. In October, VMware addressed the flaw CVE-2023-34048 (CVSS score 9.8).

Thales Cloud Protection & Licensing
MARCH 4, 2021
The Cloud Trust Paradox: Keeping Control of Data & Encryption Keys in the Cloud. Thu, 03/04/2021 - 09:38. Trust is a much-debated topic in cloud security. It is as important as privacy, security and compliance. However, there seems to be a cloud trust paradox: to trust more, you will need to trust less.
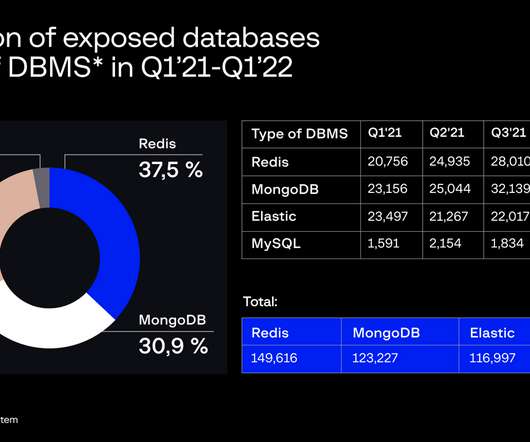
eSecurity Planet
MAY 3, 2022
From Q1 2021 to Q1 2022, the team discovered 399,200 exposed databases due to those efforts. Also read: Database Security: 7 Best Practices & Tips. According to Group-IB, the likelihood of the database systems being used in cybercrime and security breaches is high. Expectations for Security Breaches Run High .
Security Affairs
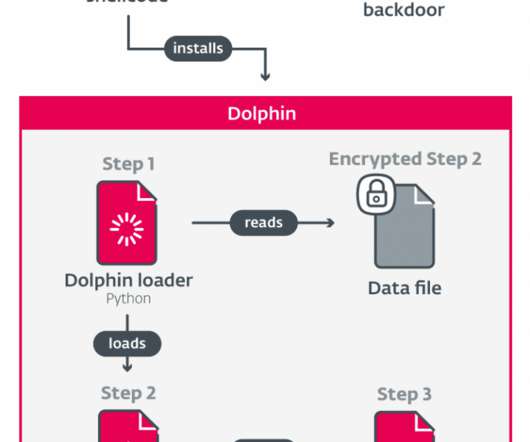
DECEMBER 1, 2022
Dolphin abuses Google Drive cloud storage for Command & Control communication. A notable feature of earlier Dolphin versions we analyzed is the ability to modify the settings of victims’ signed-in Google and Gmail accounts to lower their security, most likely to maintain access to victims’ email inboxes.” Pierluigi Paganini.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content