IAPP Launches new AI Governance Professional Certification
IG Guru
MARCH 8, 2024
Check out the article here. The post IAPP Launches new AI Governance Professional Certification first appeared on IG GURU.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IG Guru
MARCH 8, 2024
Check out the article here. The post IAPP Launches new AI Governance Professional Certification first appeared on IG GURU.

Data Matters
OCTOBER 21, 2021
On 22 September 2021, the UK Government (the “ Government ”) published its Artificial Intelligence (“ AI ”) strategy. The paper outlines the Government’s plan to make Britain a “global superpower” in the AI arena, and sets out an agenda to build the most “pro-innovation regulatory environment in the world”.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Protection Report
FEBRUARY 27, 2024
On 1 and 2 February 2024, at the fourth 4 th ASEAN Digital Ministers Meeting ( ADGMIN ) in Singapore, ASEAN [1] unveiled: the updated Joint Guide to ASEAN Model Contractual Clauses and EU Standard Contractual Clauses ( Joint MCC – SCC Guide ); and the ASEAN Guide on AI Governance and Ethics ( ASEAN AI Governance Guide ).

IG Guru
NOVEMBER 17, 2020
Check out the article here by Andrew Ysasi at Vital Records Control. The post Introduction to Information Governance (IG) and Certification via Vital Records Control appeared first on IG GURU.

Collibra
NOVEMBER 20, 2020
So your team has identified implementing data governance as a priority for the year. But what happens once you purchase a data governance platform? This article is meant to outline the vital steps for implementing data governance. Why a data governance roadmap is vital. 10 steps to successful data governance.

IG Guru
APRIL 27, 2021
Check out the article here. The post Information Governance: Navigating the Global Digital Economy via Information Management Today appeared first on IG GURU.

The Last Watchdog
FEBRUARY 20, 2023
The Costa Rican government declared a national emergency , after attackers crippled govenrment systems and demanded $20 million to restore them go normal. The Glenn County Office of Education in California suffered an attack limiting access to its own network. Lean toward spending money on cleanup and restoration rather than a payoff.

CILIP
MARCH 4, 2024
This article is featured on the AI hub AI policy is set to become the new GDPR, and the release of the UK government’s AI Regulation White Paper this month is accelerating government action on building a legal framework for AI regulation.

Preservica
JANUARY 22, 2020
In 2002, I accepted the position of Statewide Records and Forms Coordinator for the Wisconsin Department of Electronic Government (DEG). Today, digital information and communications technologies are ubiquitous in the public sector and every agency is engaged in e-government. Playing Catch Up.

IBM Big Data Hub
JUNE 26, 2023
Possibilities are growing that include assisting in writing articles, essays or emails; accessing summarized research; generating and brainstorming ideas; dynamic search with personalized recommendations for retail and travel; and explaining complicated topics for education and training. What is watsonx.governance?
Hunton Privacy
JUNE 16, 2021
In accordance with Article 21 of the DSL, a data protection policy based on the hierarchical classification and categorization of data and an “important data catalogue” (expected to be defined in future implementing rules) must be established at the national level. increasing the punishment dynamics for violations of the law. .

Unwritten Record
MARCH 18, 2024
The clips below show how Boyd shot and constructed the film to serve as an educational introduction to the Arctic environment. These clips, primarily of types of sea ice with an in-focus appearance from Boyd at the end, show how Boyd edited the footage and added intertitles to create an educational film. Local Identifier: 401.83.2)

CILIP
JANUARY 5, 2024
In all her courage and conviction, she was confronting the reality of a brutal Taliban regime that used violence to deny millions of women and girls the basic right to an education. It is not for nothing that CILIP’s own ‘impact statement’ reads: “We change lives by improving education, literacy and prosperity for all.”
Hunton Privacy
JULY 7, 2020
The Draft includes seven sections and 55 articles in total, covering data security and industrial development, the data security regulatory system, data security protection obligations and government data security and access. Government Data Security and Access. establishment of the Open Directory of Government Data.
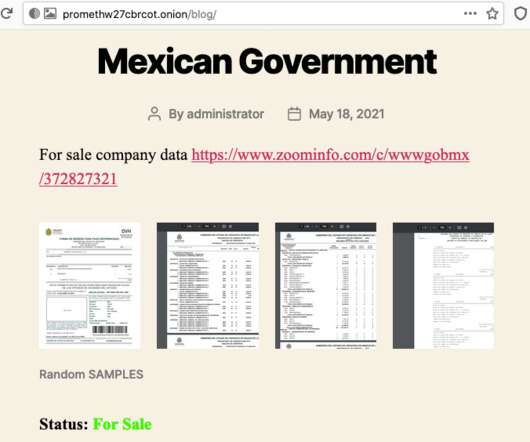
Security Affairs
JUNE 1, 2021
Just recently, the group has published a stolen data allegedly belonging to the Mexican Government which still remains available for sale today, and possibly becoming the first cybercriminal group that has touched a major state in Latin America on such a level. Mexican Government data is published for sale. Pierluigi Paganini.

IT Governance
OCTOBER 27, 2022
This includes existing information currently found in textbooks, academic research articles, technical reports, white papers and standards. How do you start your cyber security education? The post How CyBOK Can Help You Develop Your Cyber Security Career appeared first on IT Governance UK Blog.

IT Governance
FEBRUARY 7, 2023
This month, we look at a UK government warning about a resurgence in Russian cyber attacks and concerns that the much-discussed AI programme ChatGPT could be used for fraud. UK government warns of Russian-sponsored phishing campaign The UK government has issued a warning amid an increase in phishing attacks stemming from Russia and Iran.

ARMA International
SEPTEMBER 13, 2021
In the context of DT, this article defines content as information or data that has context and is consumable by humans and automated systems that allow them to make decisions, support operations, take actions, and monetize value by delivering products and services. Glossary of Records Management and Information Governance Terms, 5th ed.,
Data Protection Report
NOVEMBER 28, 2023
For cybersecurity risk prevention, the panel discussed the importance of board members being sufficiently educated to make informed decisions on any associated risk. In general, to effectively mitigate cyber risks, boards should make sure they are prepared, educated on potential and actual risks, and communicate clearly.

Krebs on Security
JANUARY 17, 2023
The government seized four-dozen booter domains, and criminally charged Dobbs and five other U.S. But the government’s core claim — that operating a booter site is a violation of U.S. man charged in the government’s first 2018 mass booter bust-up. men for allegedly operating stresser services. Charles, Ill.

Archives Blogs
NOVEMBER 30, 2017
When budget cuts forced her to curtail the traditional publications used for publicity and outreach, Rankin took the pioneering step of employing radio to communicate with prospective customers in the local government and their constituents. You can afford to give the government machinery more attention and study.’ ’ [1].

Thales Cloud Protection & Licensing
SEPTEMBER 25, 2023
Compliance officers understand and ensure adherence to local, national, and sometimes international laws that govern business practices. Training and Education: Providing training sessions and educational materials to employees to raise awareness of compliance issues and ensure they understand the rules and regulations they must follow.

The Last Watchdog
NOVEMBER 7, 2022
Governments expect ransomware attacks to cost more than $265 billion by 2031 , meaning every dollar invested now to prepare will not be wasted paying ransoms. Analysts must take the time to educate themselves about new and upcoming risks. Follow him on Twitter or LinkedIn for more articles on emerging cybersecurity trends.

ARMA International
OCTOBER 31, 2019
ARMA International and the ARMA International Educational Foundation (AIEF) are pleased to announce their collaboration on Information Management Magazine, ARMA-AIEF Special Edition , scheduled for publication mid-November. “Documentation Theory for Information Governance,” Marc Kosciejew. View the PDF version of this article.

eDiscovery Daily
MARCH 26, 2020
Nonetheless, sometime in May of 2018, the government started to try to crack the defendant’s iPhone’s passcode, using a device called “GrayKey”, which uses “brute force” to try and access the iPhone, a process by which a computer program enters potential passcodes seriatim until the correct passcode is revealed. So, what do you think?

IT Governance
APRIL 12, 2022
In this article, you’ll find an overview of the cyber security landscape from the past three months, including the latest statistics and our observations. IT Governance discovered 266 security incidents between January and March 2022, which accounted for 75,099,482 breached records. Which sectors are most vulnerable?

Preservica
FEBRUARY 22, 2022
If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! We have compiled a series of videos, from users in City and County Government to share how they quickly and easily perform common electronic records preservation and access tasks with Preservica’ s solutions.

IT Governance
OCTOBER 26, 2021
In this article, you’ll find an overview of the cyber security landscape from the past three months, including the latest statistics and our observations. IT Governance discovered 266 security incidents between July and September 2021, which accounted for 185,721,284 breaches records. Which sectors are most vulnerable? Download now.

Preservica
NOVEMBER 29, 2021
If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! We have compiled a series of videos, from users in City and County Government to share how they quickly and easily perform common electronic records preservation and access tasks with Preservica’ s solutions.

Security Affairs
SEPTEMBER 20, 2020
Every week the best security articles from Security Affairs free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.

AIIM
JUNE 4, 2020
If your organization has an internal audit function (many corporations and virtually all government offices do), those policies also act as one of the yardsticks the auditors use to evaluate the effectiveness and compliance of different arms of the business. How Do Policies and Contracts differ? We'll look at that question in Part 3.

The Last Watchdog
SEPTEMBER 21, 2022
For example, government defense contractors must pass the Cybersecurity Maturity Model Certification (CMMC) assessment to conduct business with the Department of Defense (DoD). Businesses must prioritize education for employees so they can act as the company’s first defense. PhaaS is not going anywhere.
IT Governance
OCTOBER 23, 2023
Secure remote working tips and VPN insights from our senior penetration tester Leon Teale is a senior penetration tester at IT Governance. He’s also been featured in various articles relating to cyber security. The post Expert Insight: Leon Teale appeared first on IT Governance UK Blog.

IT Governance
OCTOBER 19, 2022
In this article, you’ll find an overview of the cyber security landscape from the past three months, including the latest statistics and our observations. IT Governance identified 285 publicly disclosed security incidents between July and September 2022, which accounted for 232,266,148 compromised records. Download now.

IT Governance
JANUARY 9, 2024
Source (New) Software Luxembourg Yes 3,600,000 National Automobile Dealers Association Source (New) Retail USA Yes 1,065,000 Consórcio Canopus Source (New) Professional services Brazil Yes 1,400,000 The Teaching Company (Wondrium by The Great Courses) Source (New) Education USA Yes 1.3 TB Gräbener Maschinentechnik GmbH & Co.

Security Affairs
FEBRUARY 13, 2022
Every week the best security articles from Security Affairs free for you in your email box. A new round of the weekly Security Affairs newsletter arrived! If you want to also receive for free the newsletter with the international press subscribe here.
IT Governance
APRIL 5, 2023
IT Governance Podcast 2023-7: Capita, ChatGPT and TikTok (yet again) 5th April 2023 How to Prevent Malware Attacks: 8 Tips for 2023 5th April 2023 List of Data Breaches and Cyber Attacks in March 2023 – 41.9 Million Records Breached 3rd April 2023 GDPR Article 17: What Is the Right to Erasure?

IT Governance
JULY 11, 2022
In this article, you’ll find an overview of the cyber security landscape from the past three months, including the latest statistics and our observations. IT Governance discovered 237 security incidents between April and June 2022, which accounted for 99,019,967 breached records. This represents an 11.5% Download now.

eSecurity Planet
AUGUST 9, 2022
The GDPR provision that may keep IT security teams busiest is Article 32, which requires “a process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures for ensuring the security of the processing” of personal data. See the Top Governance, Risk and Compliance (GRC) Tools.

The Texas Record
SEPTEMBER 30, 2019
However, there are several organizations that do offer such programs for those in records management to undertake to further their education and assert the skills learned in a professionally-recognized way. LGARA Certificate Program. CRA and CRM Certifications. This page lays out what will qualify you to sit for the exam. IGP Certification.

Security Affairs
APRIL 9, 2023
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! billion rubles.

IT Governance
NOVEMBER 9, 2018
Profiling is most often used for marketing purposes, but it is also used in other areas, such as healthcare, financial services and education, where large volumes of data need to be analysed in order to make quicker and more consistent decisions. appeared first on IT Governance Blog. Such decision-making is now restricted.

IT Governance
JULY 10, 2023
In this article, we take a closer look at the information gathered in our monthly list of security breaches , and delve into the infosec landscape over the past three months. Overview IT Governance discovered 297 security incidents between April and June 2023, which accounted for 116,933,247 breached records.

IT Governance
MAY 7, 2019
In Techworld’s recent article summarising some of the most infamous data breaches in the UK, Facebook, Google+ and Reddit are all featured. Staff should be educated about the possible consequences of sharing their activities or location. Teach staff that if something looks too good to be true, it probably is.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content