ZLoader Malware adds Zeus’s anti-analysis feature
Security Affairs
MAY 3, 2024
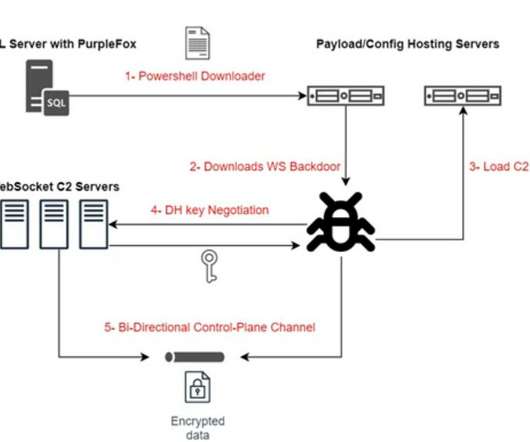
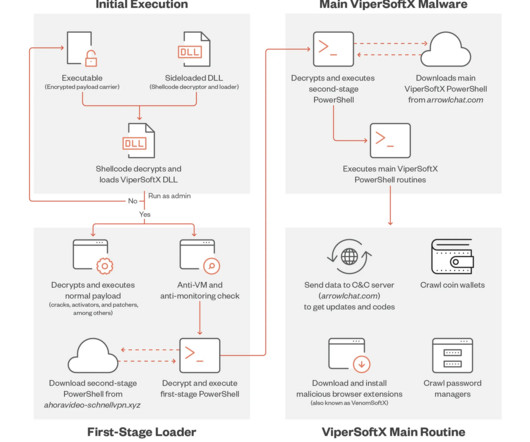
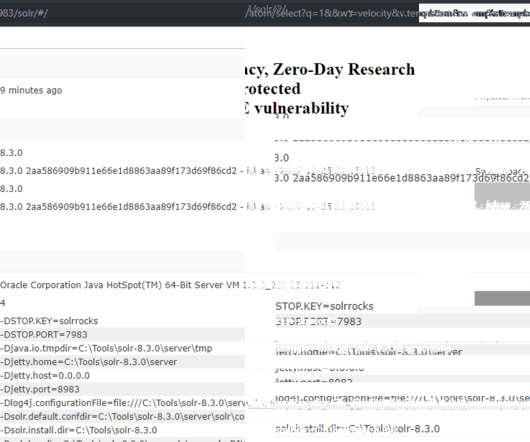
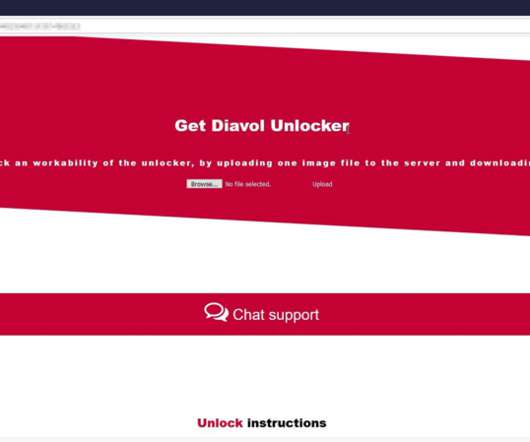
Zloader continues to evolve, its authors added an anti-analysis feature that was originally present in the Zeus banking trojan. After a hiatus of almost two years, Zloader reappeared with new obfuscation techniques, domain generation algorithm (DGA), and network communication. ” reads the analysis published by Zscaler.







































Let's personalize your content