GUEST ESSAY: The drivers behind persistent ransomware — and defense tactics to deploy
The Last Watchdog
SEPTEMBER 7, 2022
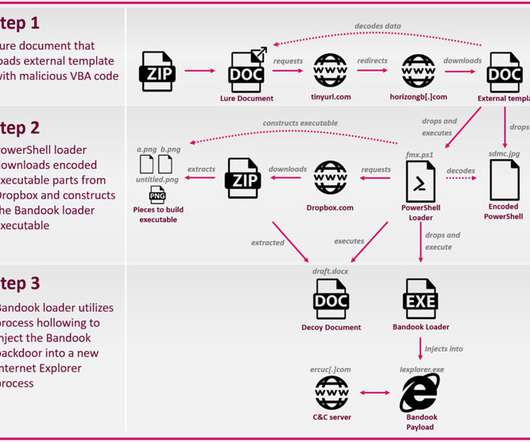
This gives the perpetrator the access needed to launch the ransomware and lock the company out of its own infrastructure or encrypt files until the ransom is paid in cryptocurrency. They’re often state-sponsored entities, foreign governments, or actual businesses. Victims have two equally unattractive choices to resolve the situation.































Let's personalize your content