U.S. Hacks QakBot, Quietly Removes Botnet Infections
Krebs on Security
AUGUST 29, 2023
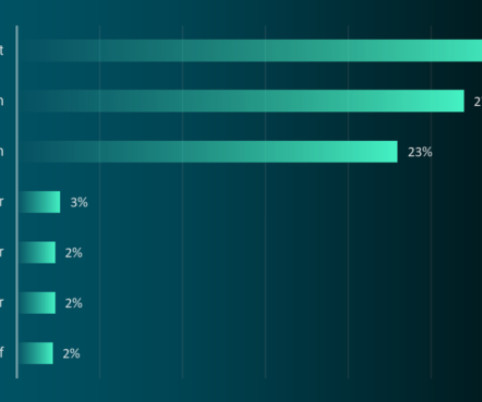
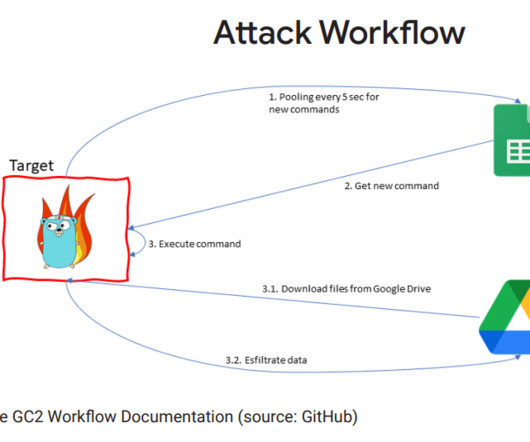
government today announced a coordinated crackdown against QakBot , a complex malware family used by multiple cybercrime groups to lay the groundwork for ransomware infections. Emerging in 2007 as a banking trojan, QakBot (a.k.a. government has used court orders to remotely disinfect systems compromised with malware.


























Let's personalize your content