Humans are Bad at URLs and Fonts Don’t Matter
Troy Hunt
OCTOBER 28, 2020
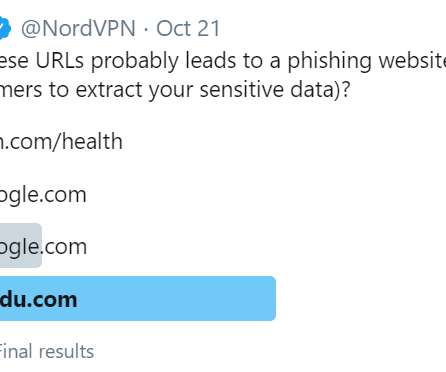
The victim, through no fault of their own, has been the target of numerous angry tweets designed to ridicule their role in internet security and suggest they are incapable of performing their duty. If I'm completely honest, I had no idea what the correct answer would be because frankly, I'm bad at reading URLs.


















Let's personalize your content