Leaking Military Secrets on Gaming Discussion Boards
Schneier on Security
JUNE 8, 2022
People are leaking classified military information on discussion boards for the video game War Thunder to win arguments — repeatedly.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
JUNE 8, 2022
People are leaking classified military information on discussion boards for the video game War Thunder to win arguments — repeatedly.

The Last Watchdog
OCTOBER 10, 2023
As tragic as it is, we are in a space where video has become a crucial asset in wartime. Related: Apple tool used as warfare weapon Ukraine’s defense against Russian invaders has changed the role of video. Metadata’s role As important as the video content itself is, there is an even more critical element: metadata.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Data Breach Today
JANUARY 9, 2020
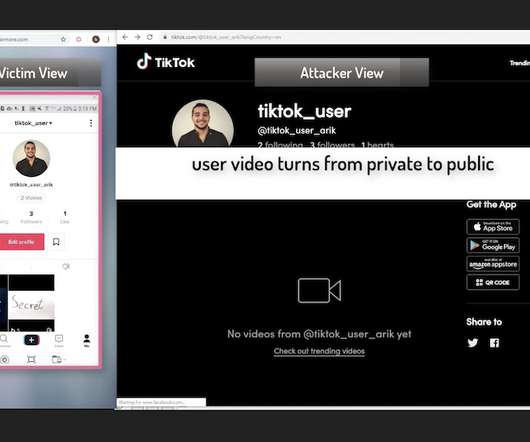
Now Fixed, Check Point Says Flaws Could Have Led to Account Takeover The security company Check Point has revealed several vulnerabilities in TikTok, the popular Chinese video app that has raised concerns lately from the U.S. military and lawmakers.
Security Affairs
MARCH 10, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
Security Affairs
FEBRUARY 28, 2020
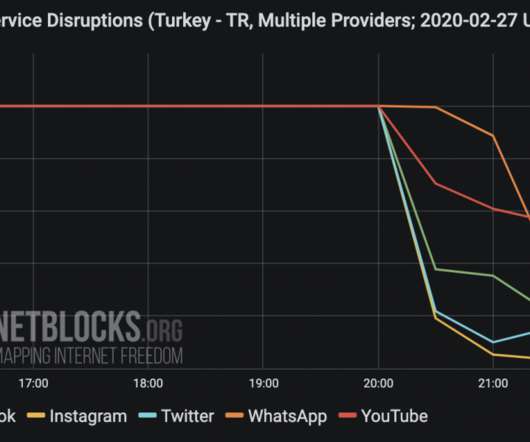
Network data collected by the NetBlocks internet observatory confirm that Turkey has blocked access to social media as Idlib military crisis escalates. In December 2016 , the Turkish blocked social media in the country to prevent the sharing of a video of the executions of Turkish soldiers by the IS group. It's 5:30 a.m.
Krebs on Security
FEBRUARY 28, 2024
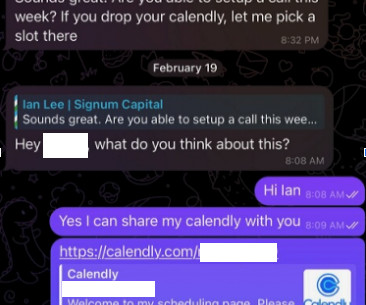
The attackers impersonate established cryptocurrency investors and ask to schedule a video conference call. The investor expressed interest in financially supporting Doug’s startup, and asked if Doug could find time for a video call to discuss investment prospects. “We are actively working on fixing these problems.
Security Affairs
JUNE 18, 2020
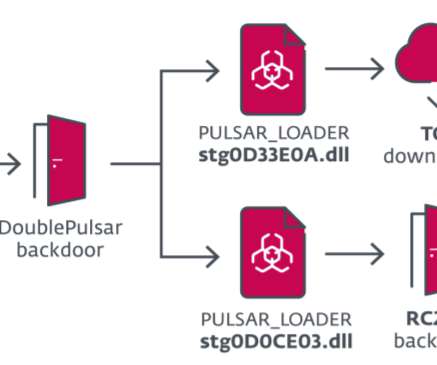
Security researchers at ESET recently uncovered a campaign carried out by the InvisiMole group that has been targeting a small number of high-profile organizations in the military sector and diplomatic missions in Eastern Europe. The SMInit exploit chain exploits a vulnerability in the legitimate Total Video Player software.

Security Affairs
JANUARY 29, 2023
Every week the best security articles from Security Affairs free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! If you want to also receive for free the newsletter with the international press subscribe here.
Security Affairs
OCTOBER 1, 2023
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

The Last Watchdog
MAY 13, 2020
Chief Information Security Officers were already on the hot seat well before the COVID-19 global pandemic hit, and they are even more so today. They must rally the troops to proactively engage, day-to-day, in the intricate and absolutely vital mission of preserving the security of IT assets, without stifling innovation.

Security Affairs
FEBRUARY 28, 2021
During a video conference of the members of the European Council, EU leaders agreed on a new strategy aimed at boosting defense and security. Participants are committed to providing secure European access to space, cyberspace and the high seas. SecurityAffairs – hacking, security). Pierluigi Paganini.
Security Affairs
APRIL 15, 2024
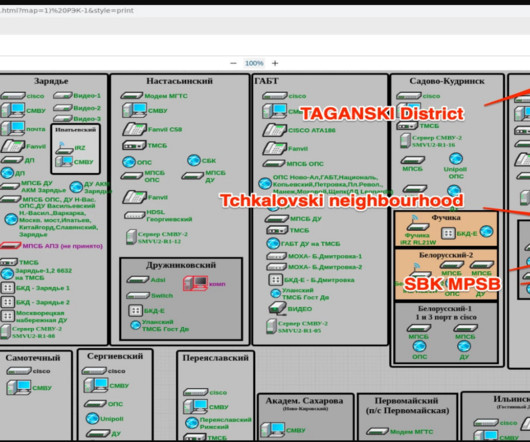
The Blackjack group is believed to be affiliated with Ukrainian intelligence services that carried out other attacks against Russian targets, including an internet provider and a military infrastructure. YouTube Video 1 , YouTube Video 2 ). All servers have been deleted.

Security Affairs
JANUARY 2, 2024
” The Ukraine’s Security Service of Ukraine is implementing countermeasures to prevent future attempts to hack surveillance cameras to conduct reconnaissance. Having penetrated her settings, the special services of the Russian Federation changed the viewing angle and connected her to the YouTube streaming platform.

Schneier on Security
JANUARY 24, 2019
Considering the storage capacity of microSD memory cards, a pigeon's organic characteristics provide front line forces a relatively clandestine mean to transport gigabytes of video, voice, or still imagery and documentation over considerable distance with zero electromagnetic emissions or obvious detectability to radar.
Security Affairs
JULY 31, 2022
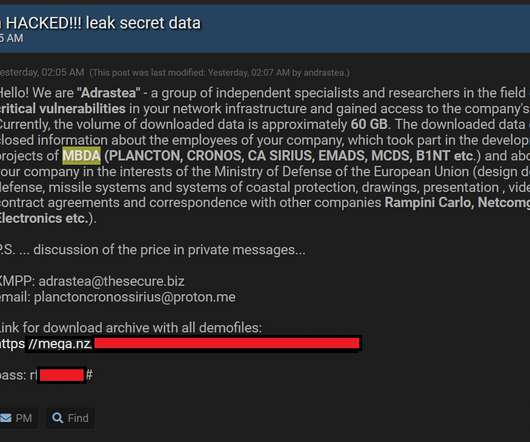
The attackers said that the stolen data includes information about the employees of the company involved in military projects, commercial activities, contract agreements and correspondence with other companies. The post Threat actor claims to have hacked European manufacturer of missiles MBDA appeared first on Security Affairs.
The Security Ledger
FEBRUARY 21, 2024
Related Stories BitCoins To Bombs: North Korea Funds Military With Billions In Stolen Cryptocurrency China Calls Out U.S. Video Podcast ] | [ MP3 ] | [ Transcript ] Four years ago, I sat down with Gary McGraw in the Security Ledger studio to talk about a report released by his new project, The Berryville Institute of Machine learning.

IT Governance
DECEMBER 20, 2022
Although there have still been a few surprises, with the death of Queen Elizabeth II and blazing heatwaves across the UK to name but two, it was a familiar year in the cyber security landscape. Google , Clearview AI , and Meta all receives hefty penalties in 2022, demonstrating the continued important of effective information security.

Security Affairs
JULY 17, 2020
Iran-linked APT35 group accidentally exposed one of its servers, leaving online roughly 40 GB of videos and other files associated with its operations. The experts found several files on the server, roughly five hours of training videos recorded by the APT group. Some of the videos were showing how to exfiltrate data (i.e.

Thales Cloud Protection & Licensing
SEPTEMBER 12, 2019
Just a couple of months after that, World Rugby itself announced that one of its training websites had suffered a security breach that exposed subscribers’ account information. That’s why it announced it would pursue two measures designed to strengthen its national digital security posture ahead of these sporting events.

The Last Watchdog
APRIL 22, 2019
It’s clear that closing the cybersecurity skills gap has to happen in order to make our internet-centric world as private and secure as it ought to be. The Boulder, CO-based company got its start in the mid-1990s as a pioneer of massive multi-player video games. It will be fascinating to see how far this can take us.

The Last Watchdog
JULY 16, 2018
When I first wrote about Cloud Access Security Brokers in 2015, so-called CASBs were attracting venture capital by the truckloads — and winning stunning customer testimonials. CASBs (pronounced caz-bees) originally sought to resolve a fast rising security nightmare: Shadow IT. CASBs new role.

The Security Ledger
JANUARY 23, 2024
In this episode of The Security Ledger Podcast (#255) host Paul Roberts interviews Niels Provos of Lacework about his mission to use EDM to teach people about cybersecurity. The post Episode 255: EDM, Meet CDM – Cyber Dance Music with Niels Provos appeared first on The Security Ledger with Paul F. Click the icon below to listen.

Data Protection Report
AUGUST 20, 2021
In addition, China published the Provisions on the Administration of Security of Automobile Data (For Trial Implementation) ( Automobile Data Regulation ) today, which will take effect on 1 October 2021. This is an implementation regulation issued under the umbrella of China’s new Data Security Law ( DSL ).

Security Affairs
DECEMBER 14, 2023
Federal Bureau of Investigation (FBI), National Security Agency (NSA), Polish Military Counterintelligence Service (SKW), CERT Polska (CERT.PL), and the UK’s National Cyber Security Centre (NCSC) the group is targeting TeamCity servers since September 2023. The issue does not affect TeamCity Cloud.

Schneier on Security
AUGUST 27, 2018
military would be unable to respond effectively for a while. Years of worry about a possible Chinese "Assassin's Mace" -- a silver bullet super-weapon capable of disabling key parts of the American military -- turned out to be focused on the wrong thing. Finally, it had, though the U.S.

ForAllSecure
AUGUST 10, 2021
Secure software creates new possibilities. Rather, the process that surrounds these programmers is what needs to improve, namely the tools and processes that they use in developing secure software. That’s why organizations need to secure their software before adversaries can attack. Watch the full video here.
Security Affairs
AUGUST 23, 2020
The Transparent Tribe cyber-espionage group continues to improve its arsenal while targets Military and Government entities. The Transparent Tribe APT group is carrying out an ongoing cyberespionage campaign aimed at military and diplomatic targets worldwide. Transparent Tribe continues to show high activity against multiple targets.

The Security Ledger
NOVEMBER 21, 2023
In this Spotlight Security Ledger podcast, Chris Petersen, the CEO and founder of RADICL, talks about his company's mission to protect small and midsized businesses serving the defense industrial base, which are increasingly in the cross-hairs of sophisticated, nation-state actors. Read the whole entry. » ” And its a big problem.

Security Affairs
AUGUST 6, 2019
The STRONTIUM APT group (aka APT28 , Fancy Bear , Pawn Storm , Sofacy Group , and Sednit ) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. link] #MSFTatBlackHat — Security Response (@msftsecresponse) August 5, 2019. ” concludes Microsoft.

Security Affairs
AUGUST 23, 2019
The security incident has happened in July at the South Ukraine Nuclear Power Plant at Yuzhnoukrainsk, in the south of the country. The Ukrainian authorities are currently investigating if any attackers may have had access to exposed systems to information that could threaten national security. ” reported ZDnet.

Adam Levin
DECEMBER 18, 2018
The report issued by the Inspector General’s office details several basic lapses in security protocols at five separate locations, including: A lack of multifactor authentication to access BMDS technical information. exposed to greater risks unless actions are taken to improve security and reduce the.

Security Affairs
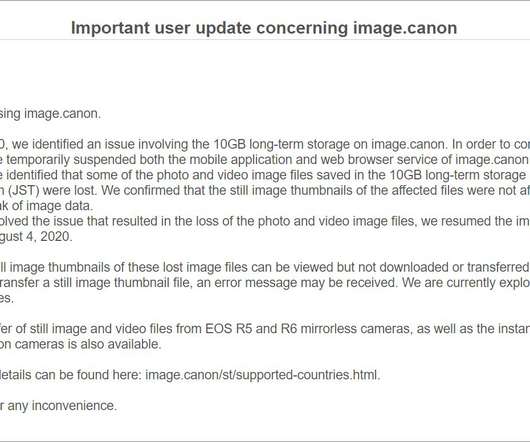
AUGUST 14, 2020
The memo also reveals that the company has hired an external security firm to investigate the incident. The problem was first reported by Bleepingcomputer, which tracked a suspicious outage on Canon’s image.canon cloud photo and video storage service. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.

The Security Ledger
JULY 31, 2018
There is more alarming security news for consumers with smart devices at home: hackers can take remote control of video cameras, thermostats, smart locks or other IoT devices by exploiting vulnerabilities discovered in Samsung’s SmartThings Hub, according to a report by Cisco Systems’ Talos research group.

Security Affairs
APRIL 22, 2021
The popular cryptographer and researcher Moxie claims the list of customers of the company includes authoritarian regimes in Belarus, Russia, Venezuela, and China, death squads in Bangladesh, and military juntas in Myanmar. This is the space in which virtually all security vulnerabilities originate.” ” concludes the expert.

eSecurity Planet
JULY 20, 2023
Mitnick often represented the company at conferences and discussed his experience in KnowBe4 training videos. military systems and launch nuclear missiles through mere whistling. He helped design KnowBe4’s training based on his social engineering tactics, and he became a partial owner of KnowBe4 in November 2011.
Security Affairs
AUGUST 7, 2020
The memo also reveals that the company has hired an external security firm to investigate the incident. The problem was first reported by Bleepingcomputer, which tracked a suspicious outage on Canon’s image.canon cloud photo and video storage service. appeared first on Security Affairs. Pierluigi Paganini.

Security Affairs
JUNE 19, 2019
According to security researchers at Trend Micro, a cyberespionage campaign is targeting Android users in Middle Eastern countries. Security researchers at Trend Micro have spotted a cyberespionage campaign, dubbed ‘Bouncing Golf, that is targeting Android users in Middle Eastern countries. Pierluigi Paganini.

The Last Watchdog
NOVEMBER 9, 2020
IoT devices help remotely control our household appliances, power plants, smart buildings, factories, airports, shipyards, trucks, trains and military. The challenge of the moment is that many companies already have their hands full trying to improve their security posture as they migrate their legacy, on premises, IT systems to the cloud.
IT Governance
NOVEMBER 1, 2022
We identified 102 security incidents throughout the month, which is the second largest figure so far this year – trailing only August (112). Meanwhile, be sure to subscribe to our Weekly Round-up to receive the latest cyber security news and advice delivered straight to your inbox. Cyber attacks.

The Security Ledger
NOVEMBER 11, 2019
In this episode of the podcast (#167): two stories this week - one from Pittsburgh and one from New York - have highlighted anxiety about Chinese made cameras and other security gear deployed in U.S. Independent Security Researchers Feel the Chill Up North Episode 162: Have We missed Electric Grid Cyber Attacks for Years? agencies.

Schneier on Security
NOVEMBER 30, 2017
ZDNet is reporting about another data leak, this one from US Army's Intelligence and Security Command (INSCOM), which is also within to the NSA. Red Disk was envisioned as a highly customizable cloud system that could meet the demands of large, complex military operations. This doesn't feel like a big deal to me. Slashdot thread.

Data Matters
JUNE 16, 2021
semiconductor production, scientific research, development of artificial intelligence, and space exploration in the face of growing economic, technological, and military competition from China. Division D – Homeland Security and Governmental Affairs Committee Provisions. Senate adopted by a 68-32 vote S. Maria Cantwell, D-Wash.,
Security Affairs
DECEMBER 24, 2019
The report said US intelligence officials and a security researcher determined the app was being used by the UAE government for detailed surveillance. It appears to be a copy of a Chinese messaging app offering free video calls, YeeCall, slightly customized for English and Arabic audiences.” appeared first on Security Affairs.

KnowBe4
APRIL 4, 2023
But, according to security researchers at Abnormal Security, cybercriminals are becoming brazen and are taking their shots at very large prizes. According to Abnormal Security, nearly every aspect of the request looked legitimate. Blog post with screenshots and links: [link] A Master Class on IT Security: Roger A.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content