How to Handle Retail SaaS Security on Cyber Monday the Hacker News
IG Guru
NOVEMBER 29, 2023
The post How to Handle Retail SaaS Security on Cyber Monday the Hacker News first appeared on IG GURU. Check out the article here.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IG Guru
NOVEMBER 29, 2023
The post How to Handle Retail SaaS Security on Cyber Monday the Hacker News first appeared on IG GURU. Check out the article here.

Security Affairs
APRIL 15, 2023
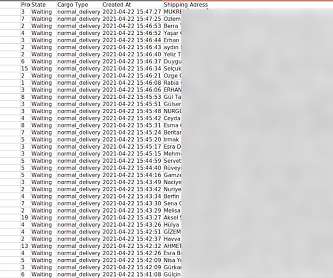
The Brazilian retail arm of car manufacturing giant Volvo leaked sensitive files, putting its clientele in the vast South American country in peril. Volvo’s retailer in Brazil, Dimas Volvo, leaked sensitive files through its website. website, belonging to an independent Volvo retailer in the Santa Catarina region of Brazil.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

AIIM
FEBRUARY 21, 2018
Organizations must focus strategically on how to manage digital content and understand that: 1) end-users are consuming technology differently; 2) consumer devices are being increasingly used as “on-ramps” to digital workflows; and 3) how you secure the scan and capture process becomes increasingly important.

IBM Big Data Hub
FEBRUARY 23, 2024
A data controller is any organization, group, or person that collects personal data and determines how it is used. Think: an online retailer that stores customers’ email addresses to send order updates. Incident response plans should include tools and tactics to recover systems and restore information security.

The Last Watchdog
MAY 3, 2021
Now comes something called attribute-based encryption, or ABE, a new approach to encrypting data that holds the potential to infuse agility into how encryption gets done online. I had the chance to learn more about ABE from Brent Waters, a distinguished scientist in the Cryptography & Information Security (CIS) Lab at NTT Research.
Security Affairs
JUNE 17, 2021
The securWizCase experts found a major breach that affected the popular online retailer Cosmolog Kozmetik. WizCase’s security team, led by Ata Hakç?l, l, has found a major breach in popular online retailer Cosmolog Kozmetik’s database. Hundreds of thousands of users were compromised in the breach. What’s Happening?

IT Governance
JUNE 14, 2018
Little more than three years since its previous security incident, electronics retailer Dixons Carphone has admitted to a data breach compromising 5.9 In a statement released on Wednesday, the retail giant revealed it had identified the colossal breach while it was reviewing its systems and data. million customer cards and 1.2

IT Governance
NOVEMBER 14, 2018
A data processor is the organisation that does the legwork; it processes the information on the controller’s behalf. For example, a marketing executive at a retailer hires a company to conduct a survey on shoppers’ browsing habits. It’s also common for organisations to get their own employees to process information.

Security Affairs
JANUARY 30, 2023
Sports fashion retail JD Sports discloses a data breach that explosed data of about 10M customers who placed orders between 2018 and 2020. We are advising them to be vigilant about potential scam e-mails, calls and texts and providing details on how to report these. Protecting the data of our customers is an absolute priority for JD.”

The Last Watchdog
MARCH 21, 2022
Become familiar with the standards that affect your industry, such as GDPR, CCPA, SOX, HIPAA, the Gramm-Leach-Bliley Act, Payment Card Industry Data Security Standard (PCI-DSS), Federal Information Security Management Act (FISMA) and Children’s Online Privacy Protection Rule (COPPA). Assign roles and responsibilities.
Security Affairs
APRIL 16, 2023
New Android malicious library Goldoson found in 60 apps +100M downloads Siemens Metaverse exposes sensitive corporate data CISA adds bugs in Android and Novi Survey to its Known Exploited Vulnerabilities catalog Volvo retailer leaks sensitive files A cyberattack on the Cornwall Community Hospital in Ontario is causing treatment delays Google fixed (..)

CGI
OCTOBER 24, 2017
How to compete in the cybersecurity talent tug of war. Across business and technology media alike, I’ve seen frequent coverage of the hundreds of thousands of cybersecurity and IT security job openings that are not getting filled. 1 (ISC)² Global Information Security Workforce Study (GISWS). harini.kottees…. million jobs.

IT Governance
AUGUST 19, 2020
In general, data processors will be expected to: Oversee the logistics of data processing; Determine how to store the collected information; Ensure that the information is secure; Determine how to transfer personal data; Ensure that a retention schedule is adhered to; and. That would make you a data controller.

IT Governance
DECEMBER 8, 2017
It will come as no surprise that Christmas is by far the busiest period for online shopping , with online sales accounting for £25 billion during Christmas 2016 (IMRG Capgemini e-Retail Sales Index, January 2017). This must-have guide features simple explanations, examples and advice to help you be security-aware online in the digital age.
Security Affairs
MAY 8, 2022
“The purpose of this publication is to provide guidance to enterprises on how to identify, assess, select, and implement risk management processes and mitigating controls across the enterprise to help manage cybersecurity risks throughout the supply chain.”

Security Affairs
JANUARY 22, 2023
The Irish DPC fined WhatsApp €5.5M

Security Affairs
JULY 4, 2021
Then overnight we realised it was much bigger and we took the decision not to open most of our stores this morning so that our teams could work out how to fix it.” . “We first noticed problems in a small number of stores on Friday evening around 6:30pm so we closed those stores early. ” reads a statement from Visma.
Security Affairs
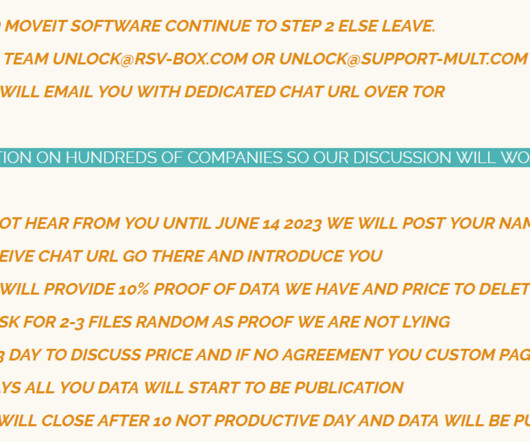
JUNE 9, 2023
Kroll security experts discovered that the Clop ransomware gang was looking for a zero-day exploit in the MOVEit Transfer since 2021. Kroll investigated the exploitation attempts for the MOVEit Transfer vulnerability and discovered that Clop threat actors were likely experimenting with how to exploit this issue as far back as 2021.

IT Governance
DECEMBER 3, 2018
Lush could have avoided this predicament by implementing an ISMS (information security management system) aligned to ISO 27001 , the international standard for information security. For more information, or advice specific to your organisation, email our team. The value of an effective ISMS. Risk assessments.

IT Governance
AUGUST 23, 2018
Here are this week’s stories: High-street retailer, Superdrug, suffered a data breach earlier this week. In an email sent to those affected, Superdrug said: “On the evening of the 20 th of August, we were contacted by hackers who claimed they have obtained a number of our customer’s online shopping information.

IT Governance
MAY 23, 2019
A year ago this week, the GDPR (General Data Protection Regulation) took effect, promising to revolutionise information security. Our experts couldn’t agree on which sector had done the least to meet the GDPR’s requirements, with retail, education and the public sector among those named the worst. Compliance fatigue’.

IT Governance
MARCH 22, 2018
Such machine learning has been adopted in industries such as motoring, healthcare and retail. It will no doubt progress to many more, so what might this mean for cyber security? Ultimately, this would help improve network security defences. We cannot continue to do things in a manual way.”.

eSecurity Planet
JANUARY 28, 2022
Also read: How to Stop DDoS Attacks: 6 Tips for Fighting DDoS Attacks. The gaming industry is most targeted by DDoS attacks, but Microsoft is finding that other industries – including financial institutions, media, internet service providers (ISPs), retailers and supply-chain companies – are seeing an increase in such incidents.

Armstrong Archives
DECEMBER 19, 2023
No matter the size of a business, a well-defined record retention policy serves multiple purposes: ensuring compliance with legal and regulatory requirements, aiding in efficient document management, and securing sensitive information. Also, their policies must be tailored to their specific industry requirements and business size.

Adapture
SEPTEMBER 30, 2020
Marvis is an IT administrator’s best friend , providing prescriptive actions and proactive notifications on how to constantly optimize user experiences. At ADAPTURE, we take pride in decades of experience in the field of information security and IT in general. Benefits of an AI-Driven Network.

IT Governance
JUNE 8, 2023
Cyber criminals are constantly creating new attacks methods to outwit defences, meaning that the only consistent and effective way to thwart an attack is for the individual to understand how phishing works and how to identify the signs before clicking a malicious link. However, staff awareness must be at the centre of your activities.

Hunton Privacy
DECEMBER 5, 2018
The comment period is open until February 11, 2019, and instructions on how to make a submission to the FTC are included in the notice. The Red Flags Rule requires certain financial entities to develop and implement a written identity theft detection program that can identify and respond to the “red flags” that signal identity theft.

CGI
JUNE 15, 2016
This flagship research surveyed 150 C-level and boardroom business leaders from the UK’s largest companies (1,000+ employees) across the commercial sectors of retail, banking, insurance, utilities and telco. Less than half of UK boardrooms are confident in the IT security advice they receive today.

CGI
JUNE 14, 2016
This flagship research surveyed 150 C-level and boardroom business leaders from the UK’s largest companies (1,000+ employees) across the commercial sectors of retail, banking, insurance, utilities and telco. Less than half of UK boardrooms are confident in the IT security advice they receive today.

IT Governance
JUNE 21, 2023
Phishing attacks are among the most common forms of cyber crime that organisations face, so it’s crucial that you learn how to prevent scams. Some bogus messages might look like security alerts, for instance, whereas others advertise bargain discounts at an online retailer.

eSecurity Planet
JANUARY 21, 2021
How to choose a GRC platform. LogicManager’s GRC solution has specific use cases across financial services, education, government, healthcare, retail, and technology industries, among others. Recommended: How To Improve Governance, Risk, and Compliance. How to choose a GRC platform. MetricStream. ServiceNow. SaaS-enabled?

IT Governance
APRIL 17, 2019
Security technology is, in most cases, cheaper and simpler to implement than cutting-edge technology. ISO 27001 , the international standard for information security management, and guidance related to the GDPR (General Data Protection Regulation) , give straightforward instructions on how to achieve effective security.

Hunton Privacy
DECEMBER 15, 2017
On December 12, 2017, the Federal Trade Commission hosted a workshop on informational injury in Washington, D.C. Some panelists stated it should occur if the information is sensitive, while others noted over-enforcement can be a deterrent to new technologies. For instance, it can look at social harms in ways that courts cannot.

eSecurity Planet
JANUARY 21, 2021
How to choose a GRC platform. LogicManager’s GRC solution has specific use cases across financial services, education, government, healthcare, retail, and technology industries, among others. Recommended: How To Improve Governance, Risk, and Compliance. How to choose a GRC platform. MetricStream. ServiceNow. SaaS-enabled?

Hunton Privacy
MAY 26, 2010
Congressman Markey had urged the FTC to investigate this issue after a CBS News exposé showed that almost every digital copier produced since 2002 stores on its hard drive images of documents that are “scanned, copied or emailed by the machine” – including documents with sensitive personal information.

IT Governance
DECEMBER 1, 2017
Retailers are the most affected , but lax security over Christmas is a problem for all organisations. We’ve highlighted some of the biggest mistakes organisations make and how to address them. Security in the Digital World is a straightforward guide for the home user, parent, consumer or home office.

IT Governance
JULY 25, 2018
You can meet the GDPR’s requirements for privacy notices via prominently displayed signs that provide brief and comprehensible information explaining that CCTV is being used, and stating who manages the surveillance system and how to contact them, as was acceptable under the DPA 1998. Redact information where necessary.
IT Governance
JUNE 1, 2023
Meanwhile, you can subscribe to our Weekly Round-up to receive the latest cyber security news and advice delivered straight to your inbox. IT Governance is dedicated to helping organisations tackle the threat of cyber crime and other information security weaknesses. With that out of the way, it’s time to move on to May 2023.

Hunton Privacy
FEBRUARY 20, 2009
CVS Pharmacy (“CVS”), reportedly the largest retail pharmacy chain, has agreed to pay the Department of Health and Human Services (“HHS”) $2.25
Security Affairs
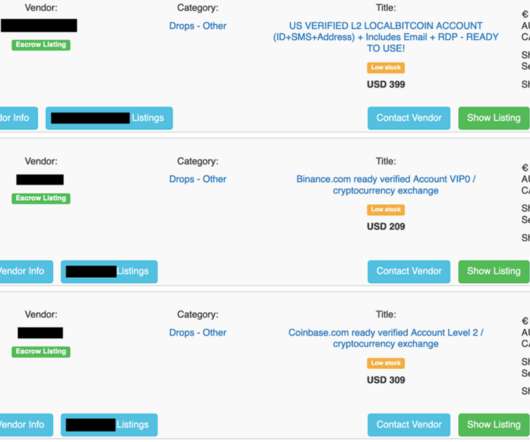
JUNE 4, 2021
More retailers accept several forms of online payments. This standard error saves the hackers a lot of work in figuring out how to gain control over different services and accounts. The guides add a cost of cents to the purchase, and it’s anybody’s guess if they work at all. Cryptocurrency trading accounts.

Hunton Privacy
APRIL 3, 2009
On March 20, 2009, the Federal Trade Commission (“FTC”) published its long-awaited guide to the Red Flags Rule (the “Rule”), entitled “Fighting Fraud with Red Flags Rule: A How-To Guide for Business.” Second, the guide sets out an expansive view of “covered accounts.”

ForAllSecure
JANUARY 15, 2021
And they said that they really had no idea how to deal with and classify, you know, a package with over, 1000 pieces of or 1000 vulnerabilities. I’m Robert Vamosi and this episode about best practices in information security, and how critical life services, in particular, remain at risk today -- in the middle of a global pandemic.

ForAllSecure
JANUARY 15, 2021
And they said that they really had no idea how to deal with and classify, you know, a package with over, 1000 pieces of or 1000 vulnerabilities. I’m Robert Vamosi and this episode about best practices in information security, and how critical life services, in particular, remain at risk today -- in the middle of a global pandemic.

ForAllSecure
OCTOBER 9, 2019
Machine learning algorithms are already being used in transportation to ease road congestion, in healthcare to spot medical errors and improve patient care and in retail to improve the customer shopping experience. But how exactly will artificial intelligence help bridge the information security skills gap?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content