Encryption Vital For Right to Privacy, European Court Rules
Data Breach Today
FEBRUARY 14, 2024
The court found that end-to-end encryption is essential to preserving the right to privacy in digital communication systems.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
FEBRUARY 14, 2024
The court found that end-to-end encryption is essential to preserving the right to privacy in digital communication systems.

Schneier on Security
APRIL 24, 2023
The Bill provides no explicit protection for encryption, and if implemented as written, could empower OFCOM to try to force the proactive scanning of private messages on end-to-end encrypted communication services – nullifying the purpose of end-to-end encryption as a result and compromising the privacy of all users.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
JULY 5, 2023
Proposed Online Safety Bill Is 'Doomed to Fail,' Academics Say in an Open Letter Over five dozen British academics joined a widening group of technology firms and privacy groups in criticizing a U.K. government bill aimed at protecting children from online harassments by weakening encryption.

IBM Big Data Hub
APRIL 24, 2024
These are just some examples of how organizations support data privacy , the principle that people should have control of their personal data, including who can see it, who can collect it, and how it can be used. One cannot overstate the importance of data privacy for businesses today. The app heavily encrypts all user financial data.

The Last Watchdog
JANUARY 28, 2024
Related: The role of ‘attribute based encryption’ There’s nothing intrinsically wrong with companies seeking to better understand their customers. Rising data privacy regulations underscores the need for such a capability, Boyle told me. This, in turn, has led to rising data privacy regulations.

The Last Watchdog
AUGUST 3, 2023
3, 2023 — Vaultree, a cybersecurity leader pioneering Fully Functional Data-In-Use Encryption (FFDUE), today announces a strategic integration with Tableau, a renowned platform for data visualization and business intelligence. San Francisco and Cork, Ireland, Aug. Today, we’re making that future a reality.”

The Last Watchdog
JUNE 12, 2023
Information privacy and information security are two different things. Related: Tapping hidden pools of security talent Information privacy is the ability to control who (or what) can view or access information that is collected about you or your customers. still available for you to use. still available for you to use.

eSecurity Planet
AUGUST 4, 2022
It’s been a couple of decades since data tapes delivered by trucks made encryption a standard enterprise cybersecurity practice. Yet even as technology has changed, sending and receiving data remains a major vulnerability, ensuring encryption’s place as a foundational security practice. What is Encryption?

Thales Cloud Protection & Licensing
NOVEMBER 15, 2021
How encryption can help address Cloud misconfiguration. Cloud service providers (CSPs) try to make it simple and easy for their users to comply with data privacy regulations and mandates. Bring your own encryption (BYOE). Tue, 11/16/2021 - 06:15. And, even experts make mistakes.

Dark Reading
JUNE 29, 2023
New online safety bill could force encrypted messaging apps like iMessage and WhatsApp to scan for child abuse material, but platforms warn about privacy implications.

Thales Cloud Protection & Licensing
NOVEMBER 2, 2021
Quantum Resistant Encryption – Are You Ready? When functional quantum computing becomes available it is anticipated to make many current asymmetric encryption ciphers (RSA, Diffie-Hellman, ECC etc.) Learn more about Thales solutions for quantum resistant encryption. Encryption. Tue, 11/02/2021 - 09:10. .

Schneier on Security
AUGUST 5, 2021
The facts aren’t news, but Zoom will pay $85M — to the class-action attorneys, and to users — for lying to users about end-to-end encryption, and for giving user data to Facebook and Google without consent.

Data Breach Today
SEPTEMBER 1, 2023
Bill 'Poses a serious threat' to end-to-end encryption, Apple Says U.S. tech companies are stepping up warnings to British lawmakers over a government proposal they say will fatally weaken security and privacy protections for users.

eSecurity Planet
AUGUST 9, 2022
Regulatory compliance and data privacy issues have long been an IT security nightmare. GDPR, the EU’s flagship data privacy and “right to be forgotten” regulation, has made the stakes of a data breach higher than ever. GDPR-style data privacy laws came to the U.S. with the California Consumer Privacy Act (CCPA) effective Jan.

Data Breach Today
APRIL 3, 2023
A 3-month-old federal law meant to future-proof federal computers from quantum computer decryption will have an effect on healthcare sector entities, too, says Mac McMillan, founder and CEO emeritus of privacy and security consulting firm CynergisTek.

WIRED Threat Level
MARCH 21, 2024
Privacy and security are an Apple selling point. But the DOJ's new antitrust lawsuit argues that Apple selectively embraces privacy and security features in ways that hurt competition—and users.

WIRED Threat Level
FEBRUARY 21, 2024
But in one of the biggest deployments of post-quantum encryption so far, Apple is bringing the technology to iMessage. Useful quantum computers aren’t a reality—yet.

Schneier on Security
DECEMBER 11, 2023
Details here , and tech details here (for messages in transit) and here (for messages in storage) Rollout to everyone will take months, but it’s a good day for both privacy and security. It’s happened. Slashdot thread.

eSecurity Planet
JULY 26, 2022
Even the most advanced and sophisticated security tools are failing to protect against ransomware and data exfiltration, according to a new report from data encryption vendor Titaniam. Raman says the emerging technology of choice to defend against data exfiltration and extortion attacks is encryption-in-use.

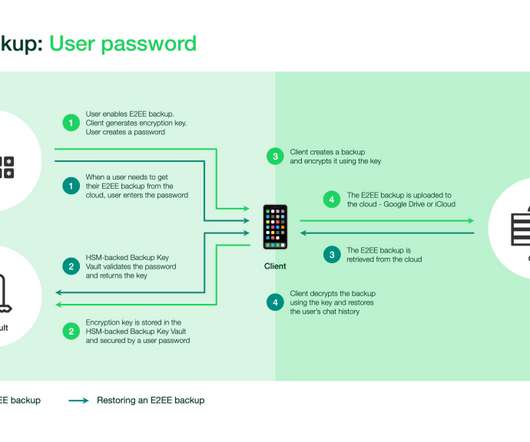
The Guardian Data Protection
OCTOBER 15, 2021
Users can set encryption key for chats on Google Drive or iCloud to prevent authorities demanding access from provider WhatsApp is allowing users to encrypt their backed-up chats, making them unreadable without access to a password or 64-digit encryption key.

Dark Reading
DECEMBER 28, 2020
The ability to perform complex calculations on encrypted data promises a new level of privacy and data security for companies in the public and private sectors. So when can they get started?

The Last Watchdog
JUNE 2, 2021
A new form of agile cryptography must get established in order to robustly preserve privacy and security as all this raw data gets put to commercial use. PKI is the authentication and encryption framework on which the Internet is built. And this is where attribute-based encryption – ABE — enters the picture.
Security Affairs
SEPTEMBER 13, 2021
Facebook announced it will allow WhatsApp users to encrypt their message history backups in the cloud. Facebook will continue to work to protect the privacy of WhatsApp users and announced that it will allow users to encrypt their message history backups in the cloud. ” reads the announcement published by WhatsApp.

eSecurity Planet
JUNE 24, 2021
The increasing mobility of data, as it ping-pongs between clouds, data centers and the edge, has made it an easier target of cybercrime groups, which has put a premium on the encryption of that data in recent years. Since then, interest in fully homomorphic encryption (FHE) has increased, largely paralleling the rise of cloud computing.

Data Breach Today
NOVEMBER 10, 2020
Investigators Find Encryption, Monitoring, Logging and Whitelisting Failures Inadequate database and privileged account monitoring, incomplete multi-factor authentication and insufficient use of encryption: Britain's privacy regulator has cited a raft of failures that contributed to the four-year breach of the Starwood guest reservation system discovered (..)

Thales Cloud Protection & Licensing
FEBRUARY 7, 2022
You can now implement and maintain encryption with minimal impact. However, their integration raises challenges around security, privacy, and the reliability of the underlying infrastructure. Encryption is best practice to ensure cybercriminals do not gain access to your business’s sensitive data. Initial encryption.

The Guardian Data Protection
JUNE 13, 2021
Will Cathcart likens governments’ stance to insisting a 1984 telescreen be installed in every living room Government attacks on WhatsApp’s end-to-end encryption are akin to demands that an Orwellian telescreen be installed in every living room, the app’s head has said as it launches a major advertising campaign in defence of privacy.

Security Affairs
FEBRUARY 1, 2021
Google discovered a flaw in GNU Privacy Guard (GnuPG)’s Libgcrypt encryption library that could be exploited to get remote code execution. The post Google discloses a severe flaw in widely used Libgcrypt encryption library appeared first on Security Affairs. Pierluigi Paganini. SecurityAffairs – hacking, Libgcrypt).
WIRED Threat Level
DECEMBER 7, 2023
Mark Zuckerberg personally promised that the privacy feature would launch by default on Messenger and Instagram chat. WIRED goes behind the scenes of the company’s colossal effort to get it right.

The Last Watchdog
NOVEMBER 8, 2021
However, healthcare data ranks at the top of the list for needing improvements in security and privacy protections. However, M&A is a complex undertaking, and integrating and consolidating IT, cybersecurity and data privacy infrastructure only adds to the challenge. Zero trust is an all-inclusive security and privacy architecture.

Threatpost
FEBRUARY 23, 2022
One cryptography expert said that 'serious flaws' in the way Samsung phones encrypt sensitive material, as revealed by academics, are 'embarrassingly bad.'.
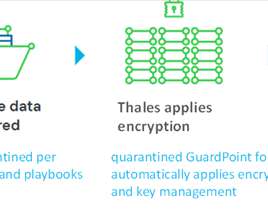
Thales Cloud Protection & Licensing
JUNE 29, 2022
How the new Spirion-Thales partnership enables sensitive-data-centric encryption. Encryption achieves this goal by making the data readable only to those individuals with the proper access levels. It’s a similar overreach to encrypt all the data your company collects, but many organizations are doing just that.

Thales Cloud Protection & Licensing
JANUARY 28, 2020
January 28, 2020 marks the 13th iteration of Data Privacy Day. An extension of the celebration for Data Protection Day in Europe, Data Privacy Day functions as the signature event of the National Cyber Security Centre’s ongoing education and awareness efforts surrounding online privacy. Encryption. Key Management.

Data Breach Today
OCTOBER 29, 2021
After Consulting With VTC Providers, Authorities Recommend End-to-End Encryption Six national data protection and privacy authorities – from Australia, Canada, Gibraltar, Hong Kong SAR, China and Switzerland - have joined with the U.K.

Security Affairs
JUNE 8, 2020
IBM has released open-source toolkits implementing fully homomorphic encryption (FHE) that allow researchers to process data while it’s still encrypted. IBM has released open-source toolkits implementing fully homomorphic encryption (FHE), which allows researchers to process encrypted data without having access to the actual data.

Security Affairs
OCTOBER 15, 2020
The Video conferencing platform Zoom announced the implementation of end-to-end encryption (E2EE) and its availability starting next week. The popular Video conferencing platform Zoom announced the availability of the end-to-end encryption (E2EE) starting next week. ” reads the post published by the company. Pierluigi Paganini.

Thales Cloud Protection & Licensing
JANUARY 24, 2022
Data Privacy and Security: It Takes Two to Tango. The National Cybersecurity Alliance (NCA) announced earlier this year that they have expanded the Data Privacy Day campaign into Data Privacy Week , a full week-long initiative. Data privacy and security: a delicate balance. Here’s where privacy and security must balance.

WIRED Threat Level
NOVEMBER 29, 2020
As the Signal protocol becomes the industry standard, it's worth understanding what sets it apart from other forms of end-to-end encrypted messaging.

Dark Reading
APRIL 30, 2019
New tools, such as Compliance Manager and Advanced Message Encryption, aim to give businesses more options for data privacy.

Schneier on Security
JANUARY 18, 2022
Rolling Stone is reporting that the UK government has hired the M&C Saatchi advertising agency to launch an anti-encryption advertising campaign. Presumably they’ll lean heavily on the “think of the children!” ” rhetoric we’re seeing in this current wave of the crypto wars.

Thales Cloud Protection & Licensing
MARCH 4, 2021
The Cloud Trust Paradox: Keeping Control of Data & Encryption Keys in the Cloud. It is as important as privacy, security and compliance. With customers increasingly being less trusting of how companies store and process their data in the cloud, encrypting this data and controlling the encryption keys is essential for building trust.

The Last Watchdog
SEPTEMBER 30, 2019
Homomorphic encryption has long been something of a Holy Grail in cryptography. Related: Post-quantum cryptography on the horizon For decades, some of our smartest mathematicians and computer scientists have struggled to derive a third way to keep data encrypted — not just the two classical ways, at rest and in transit.

Data Breach Today
JULY 20, 2022
Future quantum computers will decrypt encrypted data, so businesses feel pressure to find quantum-resistant security solutions for data transmission. Wells Fargo Bank's Peter Bordow discusses the state of quantum computing, approaches to quantum security, and privacy-enhancing technologies.

Hunton Privacy
SEPTEMBER 25, 2023
On August 8, 2023, the Massachusetts Gaming Commission approved 205 CMR 257: Sports Wagering Data Privacy , a set of regulations designed to create new rights and obligations with respect to sports betting operators’ use of patrons’ Confidential Information or Personally Identifiable Information.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content