Fake Google Update Delivering HavanaCrypt Ransomware
Data Breach Today
JULY 12, 2022
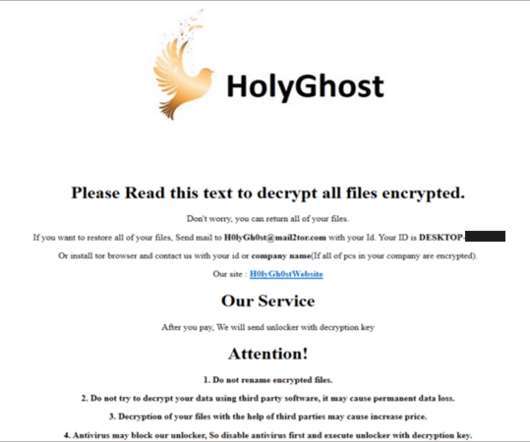
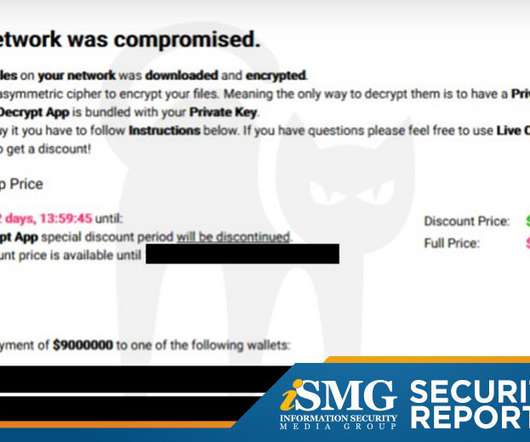
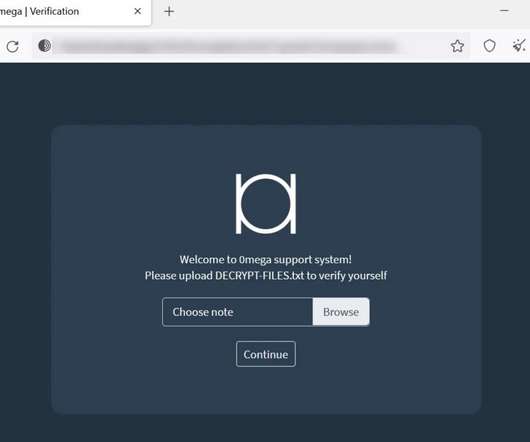
Malware Uses a Variety of Methods to Evade Detection Newly spotted ransomware dubbed HavanaCrypt by TrendMicro masquerades as the Google Software Update. For all its sophistication, it fails to drop a ransom note, leading researchers to speculate that it is still in development. Detect and block it before it causes more damage, the company warns.
































Let's personalize your content