Why Security Awareness Training Is Effective in Reducing Cybersecurity Risk
KnowBe4
DECEMBER 14, 2023
Security awareness training (SAT) works! A well-designed security awareness training campaign will significantly reduce cybersecurity risk.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
KnowBe4
DECEMBER 14, 2023
Security awareness training (SAT) works! A well-designed security awareness training campaign will significantly reduce cybersecurity risk.

IBM Big Data Hub
APRIL 15, 2024
Organizations have spent millions developing and implementing cutting-edge technologies to bolster their defenses against such threats, and many already have security awareness campaigns, so why are we failing to stop these attacks? People also have a slow, deliberate and analytical thought process, called System 2.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
JULY 7, 2022
Adam Wedgbury of Airbus on Effective Ways Humans Can Boost Cybersecurity Posture Raising user awareness is too often incorrectly considered to be a panacea for faulty information security programs. "It

The Last Watchdog
JANUARY 2, 2024
In today’s digital landscape, organizations face numerous challenges when it comes to mitigating cyber risks. Here are some of the key challenges that organizations encounter in their efforts to mitigate cyber risks in the current environment. Lack of security awareness and education.
Thales Cloud Protection & Licensing
OCTOBER 17, 2023
Cyber Security Awareness Month – Answering Google’s Most Commonly Asked Questions madhav Wed, 10/18/2023 - 05:25 This month is Cyber Security Awareness Month , highlighting how far security education needs to go in order to enable a secure interconnected world. Data Sovereignty What is data sovereignty?

KnowBe4
SEPTEMBER 15, 2023
A report from cybersecurity consultancy Savanti reveals that board members are facing challenges in understanding cyber risks , and this has important implications for businesses.

The Last Watchdog
AUGUST 31, 2023
31, 2023 – Hornetsecurity has recently launched The Security Swarm podcast series to shed light on the latest cybersecurity issues. This podcast is one of many new approaches we have introduced to support and educate cybersecurity decision-makers across the world.” Hannover, Germany, Aug.

The Last Watchdog
OCTOBER 24, 2022
Employee security awareness is the most important defense against data breaches. Related: Leveraging security standards to protect your company. Create security awareness for employees. One of the most important ways to protect against data breaches is to increase employee security awareness.
KnowBe4
MARCH 21, 2024
In an age when 70% - 90% of successful data breaches involve social engineering (which gets past all other defenses), sufficient training is needed to best reduce human-side cybersecurity risk. Everyone should be trained in how to recognize social engineering attempts, how to mitigate (i.e., delete, ignore, etc.)

KnowBe4
SEPTEMBER 20, 2023
You would think that in the cybersecurity industry, people would be all about safety and security, right? The latest data from IBM shows that the average cost of a data breach has gone up by 2% to a whopping $4.45 I mean, it's literally in the name.

OpenText Information Management
NOVEMBER 15, 2023
And while the use of large language models and generative AI in cybersecurity are still in the early stages, they open the door for attackers with lower skillsets to achieve new capabilities through the generation of malicious code, as … The post OpenText Cybersecurity 2023 Global Ransomware Survey: The risk perception gap appeared first on OpenText (..)

eSecurity Planet
DECEMBER 7, 2022
Despite all this, there is one tech category that has held up fairly well: Cybersecurity. Just look at a report from M&A advisory firm Houlihan Lokey , which found that private cybersecurity company funding grew by 9.4% There have been a number of impressive funding rounds this year for cybersecurity startups.

KnowBe4
MARCH 29, 2024
New data shows organizations are well aware that their users are one of their greatest cybersecurity risks today, and yet aren’t taking the right steps to remediate the risk.

Thales Cloud Protection & Licensing
OCTOBER 24, 2022
Cyber Security Awareness Month: Time to Act and Protect Trust. We’re approaching the end of Cyber Security Awareness Month , an annual event dedicated to increasing awareness of cybersecurity topics globally. Tue, 10/25/2022 - 06:51.

The Last Watchdog
MAY 24, 2023
As a general rule, all organizations should have a secure operation center as well as a security incident management tool that’s either run internally 24 hours a day, seven days a week, or outsourced to a partner who provides managed-security services.

KnowBe4
APRIL 1, 2024
The UK government's third phase of research shows how well UK organizations have been improving their cybersecurity efforts but indicates that the risk from certain attacks have only been reduced marginally.

Lenny Zeltser
NOVEMBER 3, 2023
After all, people outside the security team are the ones who deliver services, build products, or otherwise engage in business activities that require making security-related decisions. How might we distribute cybersecurity tasks and operationalize the perhaps utopian idea that "security is everyone's responsibility"?

eSecurity Planet
AUGUST 8, 2022
Companies spend a staggering amount of money on cybersecurity products to defend their networks and data from hackers, but a couple of industry pros say that money is wasted if companies don’t change their internal cybersecurity culture. In 2004, the global cybersecurity market was worth just $3.5 trillion by 2025.

Data Matters
MARCH 28, 2022
OCR’s reminders and recommendations for regulated entities include to: assess and reduce risks and vulnerabilities to the availability of ePHI, which is defined as “the property that data or information is accessible and useable upon demand by an authorized person” pursuant to the HIPAA Security Rule. 45 CFR 164.308(a)(5)(i).

IBM Big Data Hub
SEPTEMBER 13, 2023
With cybercriminals evolving the sophistication of their attack tactics, there is an increasing need to speed up detection, response, and neutralization of security breaches. Incorporating an effective attack surface management tool into your security strategy can significantly help you mitigate the risks of data breaches.

KnowBe4
JULY 8, 2019
Developing and maintaining a security-aware culture in an organization has become vital in the defense against modern cyberthreats. Learn how to instill a culture of security through an engaging, meaningful, and even entertaining security awareness program. Tackling security awareness with a team-based mentality.

KnowBe4
JULY 29, 2019
Developing and maintaining a security-aware culture in an organization has become vital in the defense against modern cyberthreats. Our two experts discuss: Addressing cultural challenges to investment in security awareness. Making the case for a behavior-changing awareness initiative. Watch Webinar.

eSecurity Planet
JULY 20, 2023
Kevin Mitnick, who turned legendary hacking exploits and two prison terms into a career as an esteemed cybersecurity leader, died Sunday at age 59 after a 14-month battle with pancreatic cancer, KnowBe4 revealed today. KnowBe4 has been ranked in the top 20 on our list of the top cybersecurity companies for several years.

eSecurity Planet
OCTOBER 17, 2022
According to data from Crunchbase , the total amount of investments in cybersecurity startups came to $2.6 See the Top Cybersecurity Startups. Filling the Cybersecurity Talent Gap. Additionally, the scarcity of talent is still one of the biggest issues in the cybersecurity industry,” said Shilts.

IT Governance
MARCH 29, 2018
Organisations’ second biggest concern is their employees’ lack of security awareness, according to CyberEdge’s 2018 Cyberthreat Defense Report. This is the first time in five years that poor security awareness hasn’t topped the list – with ‘lack of skilled personnel’ nabbing the top spot.

Hunton Privacy
NOVEMBER 23, 2022
On November 9, 2022, the New York Department of Financial Services (NYDFS) released its second, proposed amendments to the Part 500 Cybersecurity Rule. The proposed amendments revise several aspects of the draft Cybersecurity Rule amendments released on July 29, 2022. Penetration Testing, Vulnerability Assessments and Risk Assessments.

KnowBe4
JULY 28, 2023
The SEC (Securities and Exchange Commission) has introduced new rules that require public companies to be more transparent about their cybersecurity risks and any breaches they experience. What happened?

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Global October Cybersecurity Events: Where You Can Find Thales. The summer is now over, and October is a month full of cybersecurity events for Thales around the world. GITEX GLOBAL is the biggest security and technology event and exhibition in the Middle East. Data Security. Thu, 10/06/2022 - 06:55. Safe travels!

Dark Reading
OCTOBER 24, 2022
Best-in-class awareness training comes after a marked increase in cybersecurity risks and attacks in 2022.

Security Affairs
NOVEMBER 29, 2022
In today’s technological world, educating people about cybersecurity awareness is an absolute necessity. These errors are not always entirely preventable, as some level of human error is inevitable, but proper training in cybersecurity awareness can greatly decrease the likelihood of human mistakes leading to data breaches.
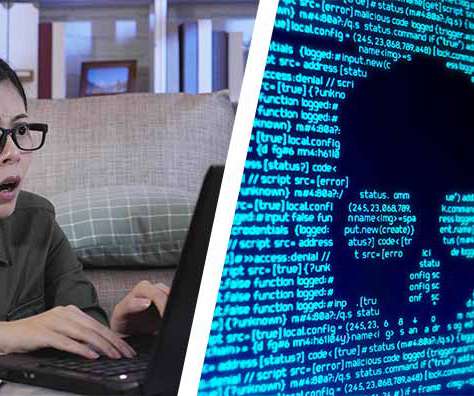
eSecurity Planet
AUGUST 22, 2022
A recent experience highlighted that security awareness training and most alerts to users about unsafe practices may be making the error of being too general. An alert came in one morning about a security alert generated by my device. See the winners of eSecurity Planet’s 2022 Cybersecurity Product Awards. Echoes of Y2K.

IBM Big Data Hub
FEBRUARY 1, 2024
Cyber workforce shortage There are over four million unfilled cybersecurity jobs in the world today. Filling these vacancies has become a security imperative, and several global compliance mandates have been established to tackle the issue. Crisis simulation After a cybersecurity breach, every second counts.

KnowBe4
MARCH 27, 2023
Younger employees need to be wary of oversharing company information on social media, according to John Karabin, senior director of cybersecurity at NTT Ltd. In an article for SmartCompany, Karabin explained that while younger users are typically more acclimated to new technologies, they may also be more distracted by them.

The Last Watchdog
JANUARY 9, 2023
A Data Privacy Impact Assessment, or DPIA , is a formal assessment of the privacy risks of your data processing activities. The purpose of conducting a DPIA is to identify and assess the potential impact of these risks on individuals’ rights and freedoms from your proposed processing operations. DPIA starting point.

eSecurity Planet
OCTOBER 18, 2022
The vast majority of cybersecurity decision makers – 91 percent, in fact – find it difficult to select security products due to unclear marketing, according to the results of a survey of 800 cybersecurity and IT decision makers released today by email security company Egress. What Should Security Buyers Do?

KnowBe4
OCTOBER 5, 2023
Gartner issued a press release that forecasted global security and risk management end-user spending to reach $188.1 billion, along with worldwide end-user spending on security and risk management projected to be $215 billion in 2024.

KnowBe4
MAY 21, 2019
Here’s another, this one offering four pieces of advice for security awareness training managers based on the findings of the DBIR. This means security awareness managers cannot exempt executives from training. Be prepared to present training that speaks to them in their language: risk. Educate the Execs.

The Last Watchdog
FEBRUARY 15, 2021
Cybersecurity training has steadily gained traction in corporate settings over the past decade, and rightfully so. In response to continuing waves of data breaches and network disruptions, companies have made a concerted effort and poured substantial resources into promoting data security awareness among employees, suppliers and clients.

eSecurity Planet
APRIL 12, 2024
12 Data Loss Prevention Best Practices 3 Real Examples of DLP Best Practices in Action How to Implement a Data Loss Prevention Strategy in 5 Steps Bottom Line: Secure Your Operations with Data Loss Prevention Best Practices When Should You Incorporate a DLP Strategy? Analyze the storage’s security protocols and scalability.
KnowBe4
DECEMBER 29, 2023
Let's explore the top 10 expected AI developments of 2024 and their implications for cybersecurity. Challenges in AI Regulation Governments' attempts to regulate AI to prevent catastrophic risks will be a key area of focus. AI's reasoning abilities are expected to soar, potentially outperforming human intelligence in certain areas.

KnowBe4
SEPTEMBER 9, 2022
New data from PwC provides insight into what aspects of the business are executives focused on, worried about, and seeing as future challenges as they look to manage business risk.

KnowBe4
OCTOBER 7, 2018
million unfilled jobs in cybersecurity. This presents a monumental risk to companies, worldwide, as they look to attract and retain these key professionals who keep their companies and general public safe from cybercriminals. Millions of Rewarding Jobs: Educating for a Career in Cybersecurity. Get your toolkit today!

OpenText Information Management
MAY 1, 2024
If you aren’t familiar with DBIR, provides invaluable insights into the evolving landscape of cybersecurity. The human element: a persistent challenge “[The human element] is present in more than two-thirds of breaches…” – DBIR 2024 Despite advancements in technology, the human element remains a significant factor in cybersecurity breaches.

KnowBe4
OCTOBER 13, 2023
But in general, security awareness training (SAT) programs should strive to win “hearts and minds” and proponents versus opponents. Social engineering and phishing accounts for 50% to 90% of successful cybersecurity exploits (depending on the data you rely on). There are thousands of topics to choose from.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content