US Government And Allies Disrupt Massive Russian Botnet
Data Breach Today
JUNE 18, 2022
Botnet Targets IoT And Android Devices; Industrial Control Systems And Computers The U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
JUNE 18, 2022
Botnet Targets IoT And Android Devices; Industrial Control Systems And Computers The U.S.

Krebs on Security
APRIL 26, 2019
A peer-to-peer (P2P) communications technology built into millions of security cameras and other consumer electronics includes several critical security flaws that expose the devices to eavesdropping, credential theft and remote compromise, new research has found. These prefixes identify different product lines and vendors that use iLnkP2P.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
MAY 31, 2021
Use cases of secure IoT deployment. In our previous blog post , we discussed the challenges for securing IoT deployments, and how businesses and consumers benefit from authenticating and validating IoT software and firmware updates. Tue, 06/01/2021 - 06:55. Use case 1: Fortune 500 Healthcare Company.

Thales Cloud Protection & Licensing
MAY 4, 2021
CryptoAgility to take advantage of Quantum Computing. The same goes with the advent of Quantum Computing , which is supposed to bring exponential computing power that shall not only bring endless benefits but also raises question marks on the current state of cryptography that is the bedrock of all information security as we know today.
eSecurity Planet
NOVEMBER 1, 2021
The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices. has made some strides on IoT security at the federal level; it remains to be seen if the EU initiative will spur the U.S. IoT market growth. IoT Security Neglected.

Thales Cloud Protection & Licensing
MARCH 10, 2021
What’s driving the security of IoT? First off, connected vehicles and IoT devices are highly attractive targets to hackers. Unlike servers and devices running in enterprise networks, IoT devices are typically shipped direct to consumers, without any control over the network or environment they run in. Guest Blog: TalkingTrust.

Thales Cloud Protection & Licensing
SEPTEMBER 12, 2018
The Internet of Things (IoT) is rapidly growing and expected to affect all industry verticals as well as our private lives. In this blog, we reached out to our technology partner Nexus to better understand the challenges that the industry faces to ensure safe deployment and management of IoT technologies. Weak authentication.

Security Affairs
JULY 23, 2021
Estonian hacker Pavel Tsurkan has pleaded guilty in a United States court to the counts of computer fraud and of creating and operating a proxy botnet. The Estonian national Pavel Tsurkan has pleaded guilty in a United States court to two counts of computer fraud and abuse. ” reads the press release published by DoJ. . .
Security Affairs
FEBRUARY 2, 2024
Furman for crimes of espionage, computer hacking, contempt of Court, making false statements to the FBI, and child pornography.” The hacking tools developed by the US cyber spies can target mobile devices, desktop computers, and IoT devices such as routers and smart TVs. District Judge Jesse M.

The Security Ledger
NOVEMBER 6, 2018
In this episode of the podcast, #119: Electronic Frontier Foundation General Counsel Kurt Opsahl joins us to talk about the Coders’ Rights Project. Also: we speak with Senthil Ramakrishnan, a lead member of AT&T’s IoT Security group about that company’s plans to work with Ericsson to certify the security of IoT devices.

ARMA International
JUNE 11, 2019
Edge computing is increasingly associated with at least two “trending” terms in the IT and information arenas: Internet of Things (IoT) and artificial intelligence (AI). Broadly speaking, the term refers to computing that’s done at or near the source of the data. back to the enterprise.”.

The Last Watchdog
NOVEMBER 30, 2018
Intelligent computing systems have been insinuating themselves into our homes and public gathering places for a while now. Grimm CEO Brain Demuth told me he hopes the work Grimm has commenced in Sparta will also contribute to generally elevating the security of all types of IoT systems. Get ready for smart ground transportation.

Krebs on Security
OCTOBER 9, 2018
If ever there were a technology giant that deserved to be named and shamed for polluting the Web, it is Xiongmai — a Chinese maker of electronic parts that power a huge percentage of cheap digital video recorders (DVRs) and Internet-connected security cameras. A rendering of Xiongmai’s center in Hangzhou, China. BLANK TO BANK.

The Last Watchdog
NOVEMBER 16, 2020
Related: How Multi Party Computation is disrupting encrypti on An accomplished violinist, Einstein, no doubt, appreciated the symmetry of his metaphor. And the risk factors will only rise exponentially as reliance on cloud infrastructure and Internet of Things (IoT) systems accelerates. For instance, basic research led by Dr. Robert L.

The Last Watchdog
MAY 23, 2022
Related: Leveraging PKI to advance electronic signatures. It used to be that trusting the connection between a workstation and a mainframe computer was the main concern. Modern digital systems simply could not exist without trusted operations, processes and connections.

The Security Ledger
JANUARY 8, 2019
In this episode of The Security Ledger podcast (#128): you're going to hear a lot from the annual Consumer Electronics Show (CES) out in Las Vegas this week, but are any of the new gadgets being released secure? And do security and privacy have a seat at the table at the world's largest electronics event? Read the whole entry. »

Thales Cloud Protection & Licensing
JULY 20, 2023
3 Ways to Protect Smart Devices from Criminal Exploits madhav Thu, 07/20/2023 - 07:28 When people think of home or business security, they are usually worried about protecting against a physical breaking in via a window or door and a burglar stealing valuables such as jewelry, cash, electronics, and equipment.

eDiscovery Daily
DECEMBER 1, 2021
As a vital part of the Electronic Discovery Reference Model (EDRM) , any data collected is done so with the intent to capture it exactly as intended or as it was actively being used. By 2025, the number of IoT devices deployed globally will surpass 25 billion. . Protecting the Quality of Your eDiscovery Data.

eDiscovery Daily
MARCH 20, 2019
See what I did there? ; o ) While I’m speaking at the University of Florida E-Discovery Conference today, let’s take a look at a couple of articles related to Internet of Things (IoT) devices that you need to know from an eDiscovery standpoint. Further, it addresses topics including data privacy, fog computing, smart cities and more.
ARMA International
FEBRUARY 21, 2020
According to futurist Bernard Marr, [2] “The Internet of Bodies (IoB) is an extension of the IoT (Internet of Things) and basically connects the human body to a network through devices that are ingested, implanted, or connected to the body in some way. Body-external devices (“wearables”). These devices can take many forms.

Krebs on Security
OCTOBER 12, 2018
BK: But certainly there are some areas of computer hardware and network design where you absolutely must have far greater integrity assurance? Once I know I can trace back the construction of a computer board to a certain place, you’ve built a different kind of security challenge for the attacker. Where does accountability come in?

IBM Big Data Hub
MAY 23, 2023
The rise of interconnected technologies like the Internet of Things (IoT), electric vehicles, geolocation and mobile technology have made it possible to orchestrate how people and goods flow from one place to another, especially in densely-packed urban areas. The solution is smart transportation.
eSecurity Planet
NOVEMBER 4, 2021
Hackers can exploit these weaknesses to compromise computer systems, exfiltrate data, and even perform DDoS attacks. It’s called hardware pen-testing , and it usually targets IoT devices such as desktop computers, tablets, smartphones, fax machines, printers, and many other electronics. The full MITRE-CWE list.

Security Affairs
SEPTEMBER 23, 2018
Google Android team found high severity flaw in Honeywell Android-based handheld computers. Evolution of threat landscape for IoT devices – H1 2018. Magecart cybercrime group stole customers credit cards from Newegg electronics retailer. Researcher devised a new CSS & HTML attack that causes iPhone reboot or freezes Macs.

Security Affairs
SEPTEMBER 20, 2018
Sustes Malware doesn’t infect victims by itself, but it is spread via brute-force activities with special focus on IoT and Linux servers. Sustes Malware doesn’t infect victims by itself (it’s not a worm) but it is spread over the exploitation and brute-force activities with special focus on IoT and Linux servers.

Thales Cloud Protection & Licensing
AUGUST 31, 2022
Organizations in the finance sector manage trillions of dollars and maintain very valuable and vital electronic data, including bank account, credit card, and transaction information as well as sensitive data related to estates, wills, titles, and other matters. Thu, 09/01/2022 - 05:15. Data security challenges.

Thales Cloud Protection & Licensing
AUGUST 28, 2018
We attended the show with our colleague Paul Cleary and sat in on many talks (and demos) ranging from attacking IoT devices over insecure Bluetooth connections, to exploiting publically available expired certificates. Are You a Good or Bad Hacker? The presenters collected over 300 million public keys from across the internet (X.509,

eSecurity Planet
FEBRUARY 13, 2023
Take advantage of CAPTCHAs (Completely Automated Public Turing tests to tell Computers and Humans Apart) to prevent automated attacks, protect against abuse, improve user experience, ensure authenticity of user-generated data, and ensure that only legitimate user interactions are processed.

eDiscovery Daily
JANUARY 18, 2018
The first, IoT devices, have been much discussed but not yet been a major data factor. On board computer systems in automobiles, Exif data in digital photos, GPS coordinates in Google maps are all examples of this type of data which has been used as evidence for years. The first is forensic images of computers and cell phones.

IBM Big Data Hub
MAY 26, 2023
Cloud computing offers the potential to redefine and personalize customer relationships, transform and optimize operations, improve governance and transparency, and expand business agility and capability. In 2017, 94% of hospitals used electronic clinical data from their EHR.

The Security Ledger
JULY 10, 2018
» Related Stories Episode 100: Estonia’s Former CIO talks about engineering a secure electronic vote Fitness apps: Good for your health, not so much for military security Episode 101: The Dystopian IoT looks a lot like the Printer Ink Aisle and City of Atlanta Employees phished on Rogue Wi-Fi. Read the whole entry. »

ARMA International
SEPTEMBER 13, 2021
This means imaging the “art of the possible” for a new future using a cloud computing model to deliver transformative change. Gartner (2021) has two related definitions: Digital Transformation: “can refer to anything from IT modernization (for example, cloud computing), to digital optimization, to the invention of new digital business models.”

DLA Piper Privacy Matters
OCTOBER 7, 2021
This include that data controllers must not use personal means of communications, including postal and electronic addresses, of the data subject in order to sent promotional or awareness materials without first obtaining the consent of the data subject, and providing the data subject with a mechanism to opt out.

AIIM
SEPTEMBER 12, 2018
The confluence of big data, cloud computing, social media, mobile devices collect and aggregate diverse data sets, which taken together, such as internet search habits and GPS tracking information may expose personally identifiable information. The Changing Nature of Personally Identifiable Information. Data Discovery.

eSecurity Planet
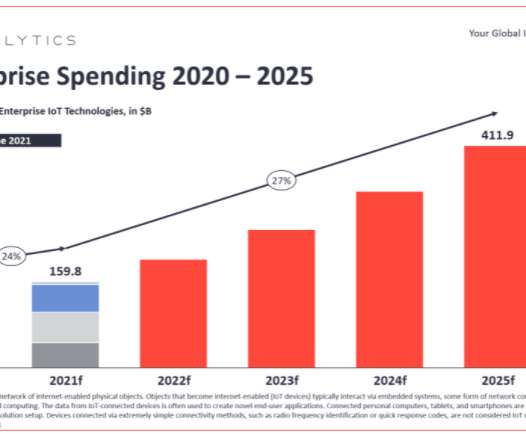
SEPTEMBER 1, 2021
Exposing the Internet of Things (IoT) Universe. Consumer electronics, business, network appliances, and industrial IoT (IIoT) devices are all driving the exponential growth of IoT systems. IoT products are notoriously vulnerable appliances because the build prioritizes ease of use and connectivity. What is 5G?

ARMA International
NOVEMBER 12, 2019
AI refers to computer systems that are able to perform tasks that are considered to require human intelligence – that is, cognitive tasks. six-in-ten Americans (58%) feel that computer programs will always reflect the biases of the people who designed them.” Definitions of AI. A central ethical issue for AI is bias in ML algorithms.

eDiscovery Daily
MARCH 25, 2018
A frequent court appointed special master in electronic evidence, Craig is a prolific contributor to continuing legal and professional education programs throughout the United States, having delivered over 2,000 presentations and papers. I don’t understand why they lump blockchain in with IoT? Today’s thought leader is Craig Ball.

Bill Schmarzo - Dell EMC
JANUARY 31, 2018
Doctors can effectively treat patients without a high performance computer or an expensive technology environment. Artificial intelligence, machine learning and deep learning (AI | ML | DL) require massive amounts of computer processing power. They just need the same iPhone that you and I use every day. Figure 1: Derm Expert App.

ARMA International
SEPTEMBER 22, 2021
This means imagining the “art of the possible” for a new future using a cloud computing model to deliver transformative change. Implied herein is a cloud computing model that ARMA (2016) defines as “A model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g.,
The Last Watchdog
JULY 6, 2023
Nuvoton was spun-off as a Winbond Electronics affiliate in July 2008 and went public in September 2010 on the Taiwan Stock Exchange (TWSE). About Nuvoton Technology: Nuvoton Technology Corporation (Nuvoton) was founded to bring innovative semiconductor solutions to the market.

eDiscovery Daily
SEPTEMBER 30, 2018
The Internet of Things (IoT) is one of the fastest growing sources of potential data in e-discovery and an important data privacy consideration. LIE227575 – The Internet of Things from a Legal and Regulatory Perspective. This session has been submitted for CLE accreditation. Ball, P.C.

Reltio
JUNE 20, 2019
I got good grades in mathematics at school but it was an evening class in secondary school that I took in what was then called EDP (Electronic Data Processing) that got me started. We didn’t even have a computer at that school so the whole class was about things drawn on the blackboard.

Reltio
OCTOBER 20, 2019
I got good grades in mathematics at school but it was an evening class in secondary school that I took in what was then called EDP (Electronic Data Processing) that got me started. We didn’t even have a computer at that school so the whole class was about things drawn on the blackboard.

Privacy and Cybersecurity Law
MAY 19, 2017
.” In the report, the GAO provides an introduction to the Internet of Things (IoT), describes what is known about current and emerging IoT technologies, and examines the implications of their use. Technological Advancements Leading To IoT Surge. Cloud computing. Common Components Of IoT Devices.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content