Code to Cloud Roadshow - Minneapolis In-Person Event hosted by Palo Alto Networks
Data Breach Today
APRIL 18, 2024
Code to Cloud Roadshow, Minneapolis In-Person Event. data security breach
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
APRIL 18, 2024
Code to Cloud Roadshow, Minneapolis In-Person Event. data security breach

Data Breach Today
MARCH 21, 2022
SASE, Cloud and Data Security, Privacy, CISO Strategies in Complex Environments The past month has been filled with action-packed virtual cybersecurity events as the enterprise community continues to deal with a myriad of cybersecurity challenges.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
JANUARY 18, 2024
Cloud storage is a cloud computing model that allows data storage on remote servers operated by a service provider, accessible via internet connections. It excels in remote access, scalability, and security, with distributed storage options and privacy adherence capabilities.
Thales Cloud Protection & Licensing
SEPTEMBER 27, 2023
Around the World with Thales: Our Upcoming Events madhav Thu, 09/28/2023 - 05:01 The summer is long gone, and we are all back to work. However, there will be plenty of opportunity for us all to catch up as the Fall season is bustling with cybersecurity events worldwide. Our event booth number is H25-C70.

eSecurity Planet
OCTOBER 16, 2023
Public cloud security refers to protections put in place to secure data and resources in cloud environments shared by multiple users or organizations. These safeguards, when combined with adherence to security best practices and standards, establish a strong security architecture for public cloud environments.

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Global October Cybersecurity Events: Where You Can Find Thales. The summer is now over, and October is a month full of cybersecurity events for Thales around the world. Below are just some of the events Thales will be at over the next few weeks. Les Assises turns 22 this year, and the event motto is "In 2022, We Speed Up!"

IBM Big Data Hub
NOVEMBER 10, 2023
This blog will focus on the integration of IBM Cloud Code Engine and IBM Cloud Event Notifications along with IBM Cloud Secrets Manager to build a robust use case that will automate your certificate renewal process for applications in your code engine project. What is IBM Cloud Code Engine?

IT Governance
DECEMBER 9, 2021
Cloud security is an essential part of today’s cyber security landscape. With hybrid working now the norm, many organisations are relying on Cloud services to access data from home or the office. This might include spotting misconfigured firewalls or physical security threats.

Thales Cloud Protection & Licensing
JUNE 5, 2024
Generative AI, Confidential Computing, and Post-Quantum Cryptography, Among Interesting Topics at Google Cloud NEXT madhav Thu, 06/06/2024 - 05:18 Thales and Google Cloud have worked together for years to develop cybersecurity solutions for Google Cloud and Google Workspace using sovereign controls to protect sensitive data.

Data Breach Today
APRIL 8, 2024
Linda Gray Martin and Britta Glade on What to Expect and What's New This Year "The Art of Possible" is the theme of RSA Conference 2024, and event organizers Linda Gray Martin and Britta Glade say they may have put together the best agenda yet - featuring sessions and speakers on red-hot topics such as identity security, cloud, gen AI and operational (..)
eSecurity Planet
NOVEMBER 22, 2023
Cloud configuration management runs and regulates cloud configuration settings, parameters, and policies to streamline cloud services and assure security. This guide covers the importance of cloud configuration management, its main components, security benefits, challenges, and best practices.
Dark Reading
OCTOBER 9, 2023
Security sensors are common in the home for both prevention and response in the event something goes wrong. But in the cloud, have you taken the same approach?

IBM Big Data Hub
APRIL 2, 2024
Among others, IBM® MQ has been recognized as the top messaging broker because of its simplicity of use, flexibility, scalability, security and many other reasons. A messaging queue technology is essential for businesses to stay afloat, but building out event-driven architecture fueled by messaging might just be your x-factor.

Thales Cloud Protection & Licensing
OCTOBER 10, 2019
theme will help to encourage personal accountability and proactive behavior in digital privacy, security best practices, common cyber threats and cybersecurity careers. As part of their digital transformation process, more and more businesses are moving to the cloud. Let us examine the typical cloud provider model. Protect IT.’
eSecurity Planet
FEBRUARY 6, 2023
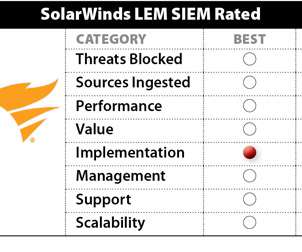
SolarWinds lacks the full security suite presence of some competitors, but is well-integrated across a variety of bonus IT operation capabilities such as threat intelligence platform capabilities, privileged access management, USB security, and botnet detection. SolarWinds Security Event Manager (SEM) 2022.4

eSecurity Planet
SEPTEMBER 1, 2023
Cloud workload protection (CWP) is the process of monitoring and securing cloud workloads from threats, vulnerabilities, and unwanted access, and is typically accomplished via Cloud Workload Protection Platforms (CWPP). What Are the Challenges of Cloud Workload Protection?

The Last Watchdog
MARCH 18, 2020
Corporate America’s love affair with cloud computing has hit a feverish pitch. Related: Why some CEOs have quit tweeting That’s the upshot of FireMon’s second annual State of Hybrid Cloud Security Report of 522 IT and security professionals, some 14 percent of whom occupy C-suite positions.

IBM Big Data Hub
APRIL 22, 2024
Resilience : Deployable architecture is designed to be resilient, with built-in redundancy and failover mechanisms that ensure the system remains available even in the event of a failure or outage. Creating a secure, compliant and tailored application infrastructure is often more challenging and requires expertise.

OpenText Information Management
APRIL 19, 2024
This AI-generated llama has been living in the clouds, creating her own cloud trails to follow. Skye has spent the last six months working with IT departments to better understand current and future needs for cloud operations. SKYE: AI has brought back the need to think about cloud operations and data strategies end-to-end.

IBM Big Data Hub
JANUARY 8, 2024
In modern enterprises, where operations leave a massive digital footprint, business events allow companies to become more adaptable and able to recognize and respond to opportunities or threats as they occur. Teams want more visibility and access to events so they can reuse and innovate on the work of others.
eSecurity Planet
DECEMBER 19, 2023
Infrastructure as a service security is a concept that assures the safety of organizations’ data, applications, and networks in the cloud. Understanding the risks, advantages, and best practices connected with IaaS security is becoming increasingly important as enterprises shift their infrastructure to the cloud.

eSecurity Planet
APRIL 19, 2023
Portnox Cloud offers network access control (NAC) as a cloud-hosted SaaS solution that enables rapid deployment of basic NAC capabilities. Although the capabilities are more limited than some NAC competitors, the quick deployment and reduced IT labor costs make Portnox Cloud an attractive solution for many.
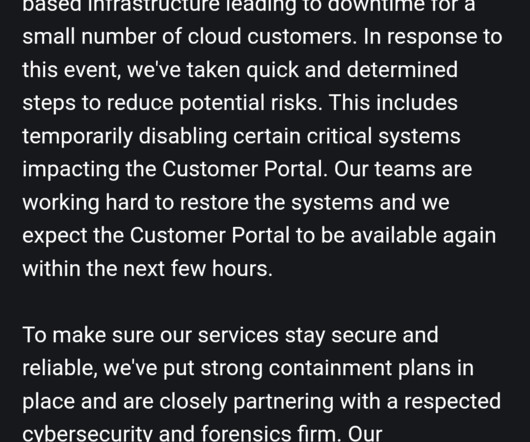
Security Affairs
AUGUST 26, 2023
The cloud and hosting provider Leaseweb suffered a security breach that impacted some “critical” systems of the company. Global hosting and cloud services provider Leaseweb has disabled some “critical” systems following a recent security breach.

eSecurity Planet
JUNE 7, 2023
IT security buyers are consolidating vendors at an overwhelming rate, according to a speaker at this week’s Gartner Security & Risk Management Summit. ” Security Products Merge Into Platforms As part of that trend, security products are consolidating too, MacDonald said.

The Last Watchdog
MARCH 29, 2022
Log4j is the latest, greatest vulnerability to demonstrate just how tenuous the security of modern networks has become. This is all part of corporations plunging into the near future: migration to cloud-based IT infrastructure is in high gear, complexity is mushrooming and fear of falling behind is keeping the competitive heat on.

IBM Big Data Hub
DECEMBER 14, 2023
Kids completing homework with ChatGPT, the rest of us generating images, PowerPoint slides, poems, code skeletons and security hacks. This year, IBM Cloud introduced projects and deployable architectures. Application templates with guardrails ensure the day-to-day operations, fixes and security patches are delivered continuously.

IBM Big Data Hub
JUNE 28, 2023
Trusted profiles can serve as a foundation for secure cloud environments and as a building block for secure cloud solutions. In our new IBM Cloud solution tutorial, you are going to learn about trusted profiles, their use cases and how to utilize them for enhanced security.

The Last Watchdog
FEBRUARY 5, 2024
Even in the cloud era, Microsoft Exchange Server remains a staple business communications tool across the globe. Fortunately, effective tools and wise best practices can help mitigate this this exposure enabling companies to indefinitely leverage Exchange Server as a productive, resilient and secure communications tool.

OpenText Information Management
JULY 20, 2021
Headline-making events like SolarWinds, Colonial Pipeline, and JBS have exposed a major vulnerability for security teams – a lack of resources to effectively detect and respond to security threats before they become serious breaches. appeared first on OpenText Blogs. appeared first on OpenText Blogs.

IBM Big Data Hub
MARCH 20, 2024
With more dependency on technology and third and fourth parties, expectations are increasing for organizations to continue delivering critical business services through a major disruption in a safe and secure manner. This means actively minimizing downtime and closing gaps in the supply chain to remain competitive. Similarly, in the U.S.

OpenText Information Management
AUGUST 22, 2023
Google Cloud Next 2023 is back in-person on August 29-31, in San Francisco. This is Google’s largest annual event with more than 15,000 IT, line of business, and developers expected to attend.

OneHub
SEPTEMBER 30, 2020
Transferring operations to the cloud has ensured it’s been ‘business as usual’ for many companies during the recent crisis. Being cloud-enabled has allowed firms to continue to collaborate across different geographical parameters and time zones. What is cloud computing? How does the cloud improve business continuity?
eSecurity Planet
MAY 19, 2023
Application security tools and software solutions are designed to identify and mitigate vulnerabilities and threats in software applications. These tools play a vital role in ensuring the security, integrity, and confidentiality of sensitive information, such as personal data and financial records.

IBM Big Data Hub
SEPTEMBER 29, 2023
Regular cleanup is part of all account administration and security best practices, not just for cloud environments. In our blog post on identifying inactive identities , we looked at the APIs offered by IBM Cloud Identity and Access Management (IAM) and how to utilize them to obtain details on IAM identities and API keys.

OpenText Information Management
JUNE 10, 2024
Yet, organizations cannot overlook the foundational need for security while working to capture this market opportunity. AI-Powered Security Challenges and Opportunities MSPs and MSSPs play an essential role in safeguarding their customers’ sensitive data and assets.

Krebs on Security
JUNE 8, 2021
Microsoft today released another round of security updates for Windows operating systems and supported software, including fixes for six zero-day bugs that malicious hackers already are exploiting in active attacks. June’s Patch Tuesday addresses just 49 security holes — about half the normal number of vulnerabilities lately.

Thales Cloud Protection & Licensing
APRIL 24, 2024
Stronger Together: Join Thales & Imperva at RSA Conference 2024 Where the World Talks Security madhav Thu, 04/25/2024 - 05:17 In today’s increasingly connected and digital world, the cybersecurity industry stands as a bastion against a relentless tide of threats. Nation states pivot with chilling precision towards any goal in their sights.
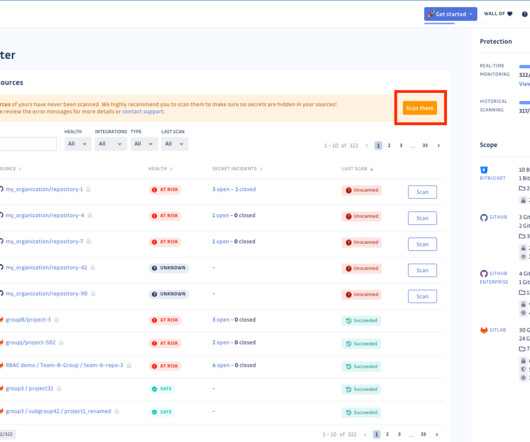
Security Affairs
NOVEMBER 8, 2023
Security firm Sumo Logic disclosed a security breach after discovering the compromise of its AWS account compromised last week. Sumo Logic is a cybersecurity company that specializes in cloud-based log management and analytics. The company discovered the security breach on Friday, November 3, 2023.

The Last Watchdog
JULY 11, 2023
Boston, July 7, 2023 — CybSafe, the human risk management platform, has today announced CEO Oz Alashe MBE has been named as a SecurityInfoWatch.com , Security Business and Security Technology Executive magazines’ 2023 Security Industry Innovator Award winner. We are developing intelligent software to help them.”

IBM Big Data Hub
SEPTEMBER 13, 2023
They all work toward the common goal of creating secure, compliant, real-time, ubiquitous and low-cost payment rails. IBM Cloud for Payments offers end-to-end, as-a-Service solutions for check payments, cross-border payments and real-time payments.

OpenText Information Management
APRIL 15, 2024
Cloud data warehouses and data lakes offer a powerful way to perform analytics that includes scalability, cost-efficiency, performance, and accessibility. Cloud data warehouses simplify data management by providing maintenance, security, and compliance features, reducing the burden on IT teams.

IBM Big Data Hub
OCTOBER 10, 2023
There is also a great deal of tension within financial markets between the requirements on innovation and agility for banking solutions versus the security, compliance and regulatory requirements that CISOs (Chief Information Security Officers) and CROs (Chief Risk Officers) need to guarantee for their financial institutions.

OpenText Information Management
APRIL 2, 2024
Recognizing that great AI starts with great information management, OpenText™ is actively collaborating with industry leaders like Google Cloud to make the integration of AI more seamless and accessible. Great AI starts with great information management The Cognitive Era is upon us, with 92% of U.S. Learn more about OpenText Aviator here.

eSecurity Planet
DECEMBER 28, 2020
The movement to the cloud means access to data anywhere, enhanced data recovery, flexibility for collaboration, and less of a burden on IT staff. But, while cloud providers boast that their storage services — or “buckets” — offer added application security , they have also consistently proven vulnerable.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content