5 Steps to Better Security in Hybrid Clouds
Dark Reading
JANUARY 23, 2018
Following these tips can improve your security visibility and standardize management across hybrid environments.

 cloud-security 5-steps-to-better-security-in-hybrid-clouds
cloud-security 5-steps-to-better-security-in-hybrid-clouds 
Dark Reading
JANUARY 23, 2018
Following these tips can improve your security visibility and standardize management across hybrid environments.

IBM Big Data Hub
JANUARY 26, 2024
Hybrid Cloud Mesh, which is generally available now, is revolutionizing application connectivity across hybrid multicloud environments. Let’s draw a comparison between Hybrid Cloud Mesh and a typical service mesh to better understand the nuances of these essential components in the realm of modern enterprise connectivity.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
MAY 15, 2023
Outsourcing DDoS Protection May Not Adequately Control Risk IT managers may be inclined to outsource their DDoS protection to their ISP or cloud service provider. While more advanced L3-L7 DDoS mitigation services may be available from some ISPs or cloud vendors, response times to an attack tend to be slow.

OpenText Information Management
MARCH 21, 2024
4 out of the top 5 airline companies use mainframe systems Mainframes handle 68% of the world’s production IT workloads, yet they account for only 6 percent of IT costs. Moreover, mainframes have top reliability, with uptime of 99.999% (down 5 minutes 13 seconds per year) to 99.9999% (down 31 seconds per year).” And what is its future?

IBM Big Data Hub
NOVEMBER 10, 2023
Once your business has decided to switch to an enterprise resource planning (ERP) software system, the next step is to implement ERP. Steps to implement ERP Below is a breakdown of a step-by-step ERP implementation plan. An ERP software can be acquired in this first step if the requirements have been well-defined.
eSecurity Planet
APRIL 14, 2023
The main purpose of bot protection is to ensure the security and integrity of online systems as well as to prevent unfair or harmful activities such as spamming, click fraud, scraping, and credential stuffing.
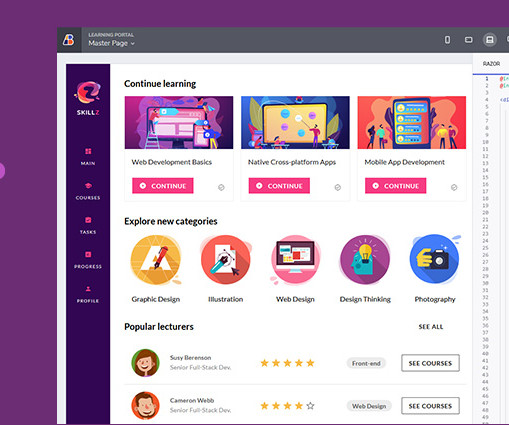
Enterprise Software Blog
MAY 9, 2023
Seen through the lens of an end-user, the things that define a great application for digital consumers today are speed, accessibility, functionality, security, and even the freedom a user is given to add customizations and tweaks. Do desktop applications fit this frame? To some extent, yes. Again, yes. And here’s why. What Is a Web App?
Let's personalize your content