Passwords stolen via phishing campaign available through Google search
Security Affairs
JANUARY 21, 2021
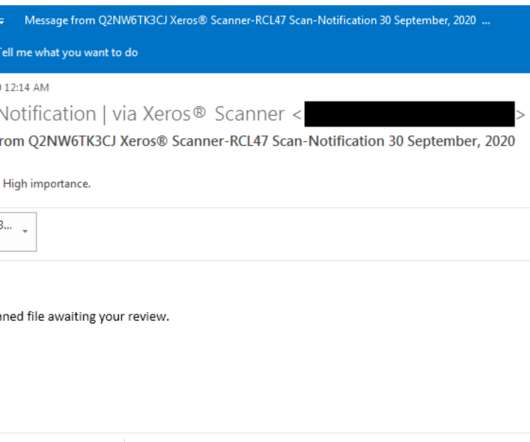
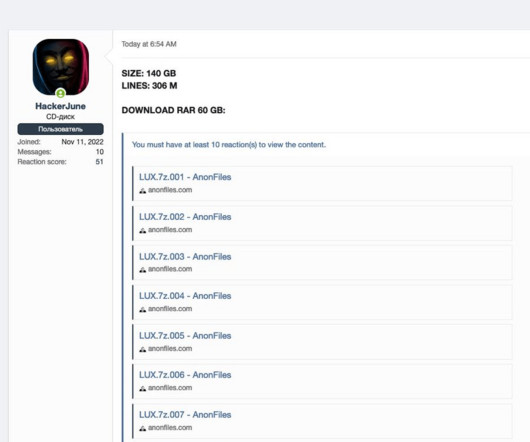
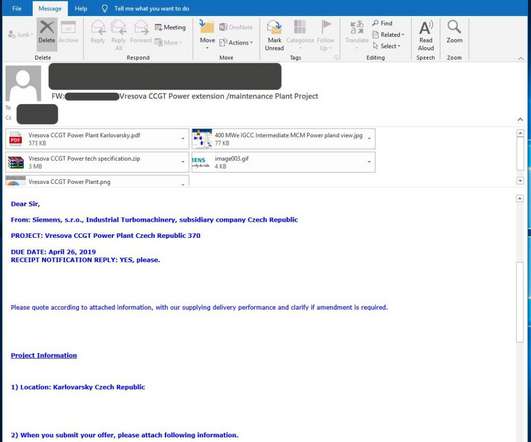
With a simple Google search, anyone could have found the password to one of the compromised, stolen email addresses: a gift to every opportunistic attacker.” The analysis of a subset of ~500 stolen credentials revealed that victims belong to a wide range of target industries, including IT, healthcare, real estate, and manufacturing.

































Let's personalize your content