Microsoft warns of BadAlloc flaws in OT, IoT devices
Security Affairs
APRIL 30, 2021
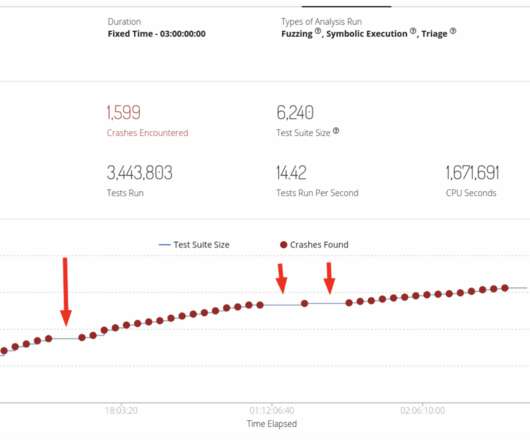
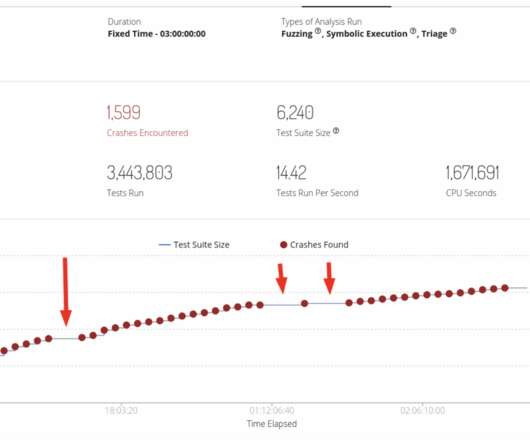
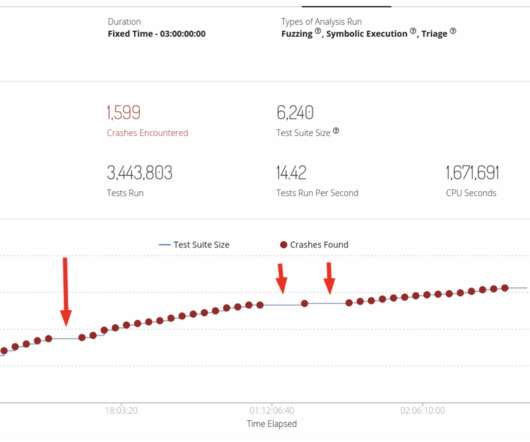
Microsoft researchers are warning of major security vulnerabilities affecting OT and IoT devices and high-risks for businesses using them. Researchers from Microsoft’s Section 52 team recently uncovered several critical memory allocation flaws, collectively tracked as BadAlloc , affecting IoT and OT devices.









































Let's personalize your content