Ex CIA employee Joshua Adam Schulte sentenced to 40 years in prison
Security Affairs
FEBRUARY 2, 2024
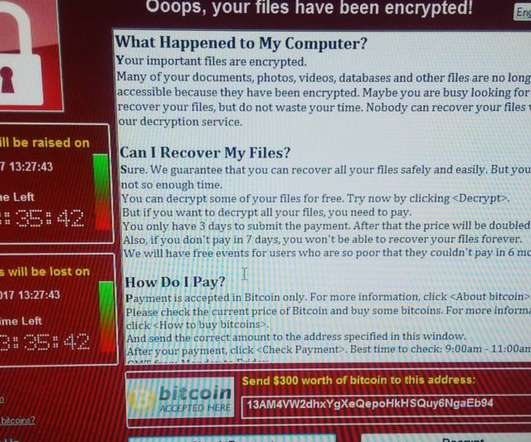
Furman for crimes of espionage, computer hacking, contempt of Court, making false statements to the FBI, and child pornography.” ” In July 2022, Schulte was found guilty in a New York federal court of stealing the agency’s hacking tools and leaking them to WikiLeaks in 2017. . District Judge Jesse M.
































Let's personalize your content