Cyber-Criminal espionage Operation insists on Italian Manufacturing
Security Affairs
MAY 22, 2020
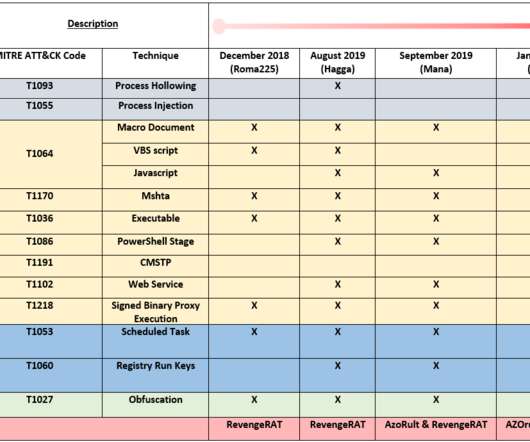
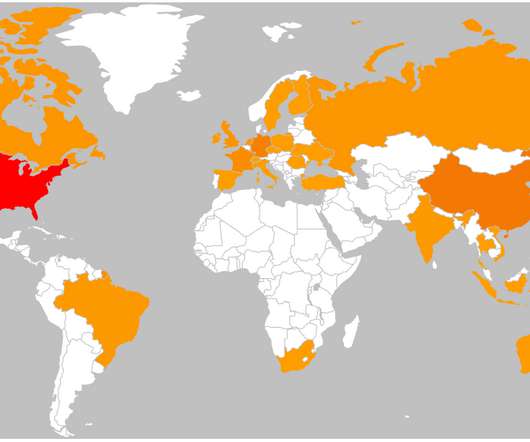
ZLab researchers spotted a new malicious espionage activity targeting Italian companies operating worldwide in the manufacturing sector. This actor was first spotted by PaloAlto’s UNIT42 in 2018 during wide scale operations against technology, retail, manufacturing, and local government industries in the US, Europe and Asia.























Let's personalize your content