New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
As most of us know, IoT devices are on the rise in enterprise networks. According to McKinsey & Company , the proportion of organizations that use IoT products has grown from 13 percent in 2014 to 25 percent today. The issue is that these tens of billions of new devices will likely amplify the inherent security risks of IoT.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
JULY 15, 2021
Key Developments in IoT Security. Remember the early days of the emergence of Internet of Things (IoT) devices? The rush to market for consumers to enjoy the modern conveniences offered by these devices shocked the security community. Security experts were concerned that these devices were built with no security in mind.

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. Now for the big challenge - security. I also looked at custom firmware and soldering and why, to my mind, that was a path I didn't need to go down at this time. Let's dive into it.

The Last Watchdog
NOVEMBER 15, 2018
Even as enterprises across the globe hustle to get their Internet of Things business models up and running, there is a sense of foreboding about a rising wave of IoT-related security exposures. And, in fact, IoT-related security incidents have already begun taking a toll at ill-prepared companies. Tiered performances.

The Last Watchdog
MARCH 28, 2019
Related: IoT botnets now available for economical DDoS blasts. His blog, Krebs on Security , was knocked down alright. Here we are in 2019 and the same attack strategy continues to persist. It’s easy to do when there are six million open DNS resolvers on the internet using poor security practices.”. Beyond DDoS.

Thales Cloud Protection & Licensing
OCTOBER 19, 2022
Manufacturing needs to adopt a Zero Trust approach to mitigate increased cyber threats. Long gone is the time when manufacturing systems and operations were siloed from the Internet and, therefore, were not a cybersecurity target. Thu, 10/20/2022 - 06:20. Survey’s key findings.

The Last Watchdog
FEBRUARY 21, 2024
Related: How decentralized IoT boosts decarbonization Yet, more so than ever, infusing trustworthiness into modern-day digital services has become mission critical for most businesses. If you factor in where we are in the world today with things like IoT, quantum computing and generative AI, we could be heading for a huge trust crisis.”

IBM Big Data Hub
JUNE 20, 2023
Here’s what you need to know in order to build a successful strategy. We’ll go deeper into EAMs, the technologies underpinning them and their implications for asset lifecycle management strategy in another section. What is an asset? First, let’s talk about what an asset is and why they are so important.

eSecurity Planet
FEBRUARY 2, 2024
Within the last couple of months, smart device vulnerabilities have been piling up, prompting businesses to protect their Internet of Things (IoT) environments. While Teslas aren’t the typical business IoT device, their connection to the internet makes them a cyber threat as much as your business’s other IoT technology.

eSecurity Planet
FEBRUARY 23, 2022
How can an industrial recycler safely secure its $400,000 hard drive recertification rack with control software that only runs on Windows XP? The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. Also read: Top IoT Security Solutions for 2022.

IBM Big Data Hub
MAY 31, 2023
There are many overlapping business usage scenarios involving both the disciplines of the Internet of Things (IoT) and edge computing. This is especially true in manufacturing and industrial engineering. From strategy to design, development and deployment, there is a lot of thought that goes into connecting physical products.

eSecurity Planet
MARCH 1, 2023
Wireless security is the protection of wireless networks, devices and data from unwanted access and breaches. It involves a variety of strategies and practices designed to preserve the confidentiality, integrity and availability of wireless networks and their resources. What is Wireless Security?

IBM Big Data Hub
JANUARY 15, 2024
And while no one digital transformation strategy will be like any other, here are some recurring trends that help organizations engage in successful digital transformation initiatives. cloud service providers use cloud technologies to maintain uptime and security, so organizations can focus on their core businesses.

Thales Cloud Protection & Licensing
MAY 30, 2018
The recent DHS Cybersecurity Strategy was released at a crucial time when today’s cyberspace has become a new frontier for warfare for both nation states and criminal hackers. The key to successfully applying the first two pillars of the strategy includes evaluating cyberthreats quickly and mitigating risks or remediating threats swiftly.

Thales Cloud Protection & Licensing
AUGUST 16, 2018
On May 16, the Department of Homeland Security (DHS) released a new cybersecurity strategy to keep pace with the evolving cyber risk landscape. As we inch closer to the mid-term elections in November, I wanted to share what I hope (expect) to see as part of this strategy going forward. Beyond the basic best practices – The U.S.

eSecurity Planet
NOVEMBER 19, 2021
IoT security is where endpoint detection and response ( EDR ) and enterprise mobility management ( EMM ) meet the challenges of a rapidly expanding edge computing infrastructure. As the enterprise attack surface grows, IoT is yet another attack vector organizations aren’t fully prepared to defend.

Thales Cloud Protection & Licensing
DECEMBER 13, 2018
Invariably, Internet of Things (IoT) strategies form the backbone of those efforts. Enormous quantities of data can be generated by and collected from a wide variety of IoT devices. The diversity of IoT devices and lack of standardisation also poses challenges. The goal is then to analyse it and take impactful action.

The Last Watchdog
FEBRUARY 21, 2020
Related: Why PKI is well-suited to secure the Internet of Things PKI is the authentication and encryption framework on which the Internet is built. I had a chance to interview Brian Trzupek , DigiCert’s senior vice president of emerging markets products, at the company’s Security Summit 2020 in San Diego recently.

Thales Cloud Protection & Licensing
AUGUST 24, 2021
Finding #1: CIOs Have Begun to Focus on Security Through Loyalty. Organizations’ shift to remote work proved that security doesn’t need to happen in the office. Finding #2: CIOs Must Embrace a Holistic Security Approach. But they didn’t always take the proper precautions to secure those devices. That’s a crucial point.

The Last Watchdog
MARCH 31, 2021
The start of 2021 brings forth a cyber security crossroads. From the known compromise vectors to the most recent threats, hackers are constantly on the lookout for new strategies to bypass IT notice, out maneuver defense setups, and take advantage of new weaknesses. Many employees don’t have a wide range of security protections.

OpenText Information Management
APRIL 1, 2024
Mark will be joined by OpenText customer Carsten Trapp, CIO of manufacturer Carl Zeiss, who will discuss his company’s partnership with OpenText to support their SAP S/4HANA transformation and compliance initiatives. While you’re wandering the show floor, take time out to see AI in action at the Aviator IoT LEGO® Experience.

Data Matters
MARCH 7, 2022
If adopted in its current form, the new rules will impose far-reaching obligations on tech companies (such as manufacturers of connected products and cloud service providers) and give national authorities new enforcement powers to sanction infringements with fines of up to EUR 20 million or 4% of annual global revenue, whichever is higher.

eSecurity Planet
OCTOBER 26, 2021
Threat intelligence can help scan IT environments for the latest malware, but that’s just one security layer against zero-day threats. There is no such thing as an ironclad risk-averse software management strategy; therefore, organizations must strive to be risk-aware. Also read: How to Defend Common IT Security Vulnerabilities.
eSecurity Planet
NOVEMBER 10, 2021
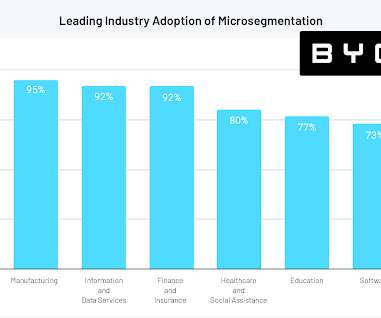
For a security technology that’s only a few years old, microsegmentation is catching on quickly. According to a new report from edge security vendor Byos, 88 percent of cybersecurity leaders believe microsegmentation is essential to achieving zero trust security, and 83 percent are currently leveraging microsegmentation in some form.
eSecurity Planet
NOVEMBER 11, 2021
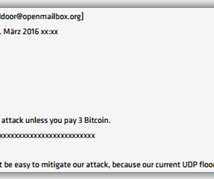
Hackers targeted a wide range of organizations, such as banks, mail services, Bitcoin sites, VoIP providers, vaccination registration portals, information security media, gaming platforms, government sites, and even security agencies. Ransom Now a DDoS Strategy. DDoS Attackers Target Middleboxes, UDP.

IBM Big Data Hub
AUGUST 8, 2023
This ambitious bill, largely managed by the US Department of Transportation, will distribute USD 1 trillion to fund construction, manufacturing initiatives and public works. Both strategies help enterprises better plan for maintenance and avoid costly shutdowns that can impact the entire business.

Information Matters
DECEMBER 7, 2017
Finding “reliable” data about the installed base of Internet of Things (IoT) devices, market size and forecasts is not easy and can be expensive if you have to buy a commercial market report. Creating IoT stats is notoriously difficult depending on accuracy of models, assumptions and definitions. billion in 2018, an increase of 14.6%

Thales Cloud Protection & Licensing
OCTOBER 10, 2022
Protect 5G to Secure Sustainable Growth. These concepts are no longer limited to our mobile devices but are becoming increasingly important to operations in the manufacturing, transportation, and energy sectors. In fact, according to Gartner, the deployment of IoT devices will accelerate from 25 billion in 2023 to 75 billion in 2025.

ARMA International
SEPTEMBER 13, 2021
The exponential growth in content is fueled by a plethora of connected devices, colloquially called “Internet of Things (IoT),” from cell phones, mobiles, and wearable technologies, to sensors in homes, appliances, cars, and so on. Consequently, CS are inextricably linked to a cloud-first strategy. Content Services Platforms (CSP).

Thales Cloud Protection & Licensing
DECEMBER 5, 2017
I also tapped some of my expert colleagues John Grimm, Sol Cates, Jose Diaz and Jon Geater to share their thoughts on a few areas including IoT, established and emerging technologies, and payments. safety of employees) and IT security. I’m in agreement with my colleagues when it comes to IoT security.

eSecurity Planet
SEPTEMBER 1, 2021
Service providers and 5G-enabled device manufacturers both have critical roles to play in the success and sustainability of this wireless network rollout. Exposing the Internet of Things (IoT) Universe. IoT products are notoriously vulnerable appliances because the build prioritizes ease of use and connectivity.

eSecurity Planet
MARCH 22, 2023
Network security protects and monitors the links and the communications within the network using a combination of hardware, software, and enforced policies. Networks and network security comes in a wide range of complexity to fit the wide range of needs. For a more general overview consider reading: What is Network Security?

IBM Big Data Hub
MAY 15, 2024
End users cannot trust their AI output without a proficient data integration strategy to integrate and govern the organization’s data. It prevents the fully managed design time from touching that data, improving security and performance while retaining the application efficiency benefits of a fully managed model.
Hunton Privacy
MARCH 2, 2023
On March 2, 2023, the Biden-Harris Administration announced the release of the National Cybersecurity Strategy.

Thales Cloud Protection & Licensing
JANUARY 24, 2024
Protecting Against the Risks and Managing the Complexities of a Quantum World with Thales and IBM Consulting madhav Thu, 01/25/2024 - 11:03 Contributors: Ollie Omotosho - Director, Strategir Partnerships, Thales Antti Ropponen, Head of Data & Application Security Services, IBM Consulting In the world of business, data security is paramount.

The Last Watchdog
DECEMBER 9, 2021
The acceleration of cloud, mobility, and security initiatives proved to be critical for organizations looking to weather the new threats and disruptions. Related: How ‘SASE’ blends connectivity, security. Cybercriminals have taken advantage of security challenges that arise from the new model of remote work and collaboration.

Collibra
APRIL 3, 2019
Continued adoption of IoT technologies will pose both opportunities and challenges. A tsunami of new data streams offers enormous opportunities in guiding digital transformation strategies across many industries. Any organisation engaged in IoT will be amassing datasets that have the potential to become extremely valuable.

ForAllSecure
MARCH 8, 2023
And I was really fortunate to land the security beat right away. I wrote two books, one on IoT Security and another with Kevin Mitnick, then jumped around a couple of different jobs. What if you are a woman in information security? WANG : it was the security security practice. By accident. So I learned.

IBM Big Data Hub
JUNE 15, 2023
When it comes to managing assets throughout their lifecycle, business leaders know they need a comprehensive strategy in place to succeed. But they aren’t always clear on the strategic opportunities around parts inventory management and the role it plays in maintenance strategy.

IBM Big Data Hub
AUGUST 7, 2023
For instance, in response to sustainability trends, product manufacturers may need to prove the carbon footprint of their products to regulators and clients. It provides a comprehensive solution for secure, transparent and trustworthy data management. Figure 2 illustrates the blockchain functionalities that Orion offers.
eSecurity Planet
APRIL 7, 2023
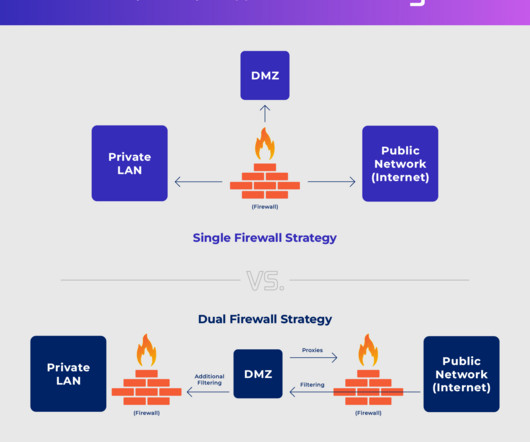
Also referred to as a perimeter network or screened subnet, a DMZ network acts as an additional layer of network security, isolating itself and its contents from the parts of the enterprise network where more sensitive and private resources are more securely kept.

eSecurity Planet
FEBRUARY 16, 2021
Rogue security software. Architect a premium network security model like SASE that encompasses SD-WAN , CASB , secure web gateways , ZTNA , FWaaS , and microsegmentation. Most device or software manufacturers place backdoors in their products intentionally and for a good reason. Jump ahead: Adware. Bots and botnets.

IBM Big Data Hub
MARCH 28, 2024
As cloud computing continues to transform the enterprise workplace, private cloud infrastructure is evolving in lockstep, helping organizations in industries like healthcare, government and finance customize control over their data to meet compliance, privacy, security and other business needs. billion by 2033, up from USD 92.64
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content