Google Gmail client-side encryption is available globally
Security Affairs
FEBRUARY 28, 2023
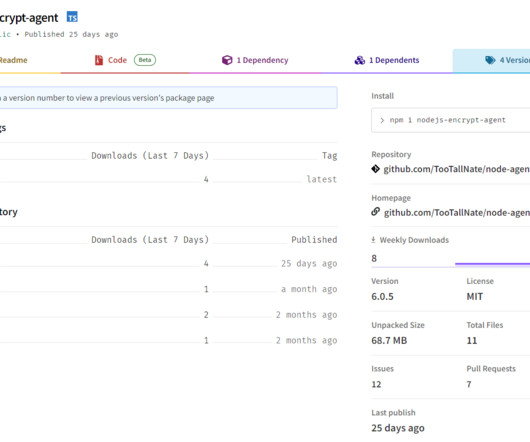
Gmail client-side encryption (CSE) is now available for Workspace Enterprise Plus, Education Plus, and Education Standard customers. Google announced that Gmail client-side encryption (CSE) is now available for all Google Workspace Enterprise Plus, Education Plus, and Education Standard customers.






























Let's personalize your content