Jamf Event: Education recap
Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.
Thales Cloud Protection & Licensing
SEPTEMBER 27, 2023
Around the World with Thales: Our Upcoming Events madhav Thu, 09/28/2023 - 05:01 The summer is long gone, and we are all back to work. However, there will be plenty of opportunity for us all to catch up as the Fall season is bustling with cybersecurity events worldwide. Our event booth number is H25-C70.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Global October Cybersecurity Events: Where You Can Find Thales. The summer is now over, and October is a month full of cybersecurity events for Thales around the world. Below are just some of the events Thales will be at over the next few weeks. Les Assises turns 22 this year, and the event motto is "In 2022, We Speed Up!"

KnowBe4
MAY 2, 2022
I recently attended a customer’s annual security awareness training employee event. It included everything I think a security awareness training employee event should have. I have attended a bunch of these over the years and I have loved them all. But this particular customer threw a great one!
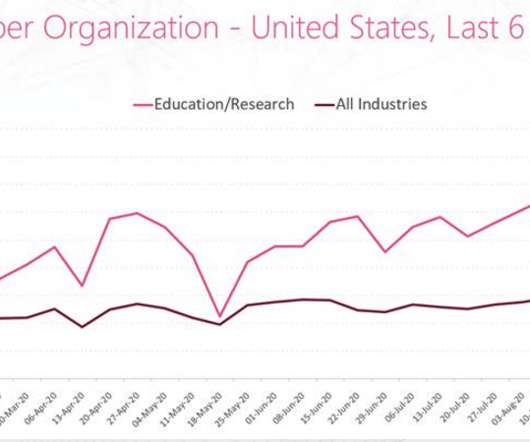
Security Affairs
SEPTEMBER 15, 2020
Experts warn of a surge in the DDoS attacks against education institutions and the academic industry across the world. The DDoS attacks are causing severe issues to the targeted education institutions such as temporarily takedown of the network and online classes. Most of the attacks targeted educational institutions in the U.S.,

The Last Watchdog
SEPTEMBER 27, 2021
To minimize their impact, implementing preventive security measures into these advanced systems is crucial. Businesses across all industries can function adequately without worrying about would-be hackers with malicious intent when they secure their networks. Related: How Russia uses mobile apps to radicalize U.S.

IT Governance
SEPTEMBER 10, 2020
This incident is the latest in a long line of cyber attacks on the education sector. It followed August’s ransomware attack on the education administrator Blackbaud , in which students’ phone numbers, donation history and events attendance were all compromised. Cyber Security as a Service.

ForAllSecure
JUNE 7, 2023
We have 4 upcoming events planned for June 2023: Mayhem Unleashed Webinar: Discover our Next Generation Security Testing Solution DevSecOps Roundtable CyberSecurity Summit Hartford ForAllSecure APFT (Adversary, Penetration, and FuzzTesting) Training Read on to learn more about June’s events. We hope to see you there!

IT Governance
OCTOBER 6, 2022
This October is Cyber Security Awareness Month, an event designed to educate people about information security and the steps they can take to stay safe online. This year’s event focuses on phishing and ransomware – two of the biggest threats that organisations currently face. Getting involved.

The Last Watchdog
FEBRUARY 15, 2021
In response to continuing waves of data breaches and network disruptions, companies have made a concerted effort and poured substantial resources into promoting data security awareness among employees, suppliers and clients. Cybersecurity education for kids is therefore a smart investment. Host virtual events?

The Last Watchdog
SEPTEMBER 6, 2023
Strong security measures become increasingly important as more people use this digital currency. Related: Currency exchange security issues For managing and keeping your Bitcoin assets, you must need a bitcoin wallet, which is a digital version of a conventional wallet. Secure your network, device. Select a reliable wallet.

OpenText Information Management
APRIL 19, 2024
This AI-generated moose has been on the hunt for threats and keeping security top of mind. You: How has AI evolved the landscape of security? General awareness and education on the potential threats to your employee base is a must. Meeting risk and security standards are table stakes for companies of all sizes.

The Last Watchdog
JULY 11, 2023
Boston, July 7, 2023 — CybSafe, the human risk management platform, has today announced CEO Oz Alashe MBE has been named as a SecurityInfoWatch.com , Security Business and Security Technology Executive magazines’ 2023 Security Industry Innovator Award winner. We are developing intelligent software to help them.”

IBM Big Data Hub
APRIL 15, 2024
Organizations have spent millions developing and implementing cutting-edge technologies to bolster their defenses against such threats, and many already have security awareness campaigns, so why are we failing to stop these attacks? People also have a slow, deliberate and analytical thought process, called System 2.

The Last Watchdog
FEBRUARY 5, 2024
Fortunately, effective tools and wise best practices can help mitigate this this exposure enabling companies to indefinitely leverage Exchange Server as a productive, resilient and secure communications tool. These practices are foundational for maintaining the security and operational integrity of Exchange Server environments.
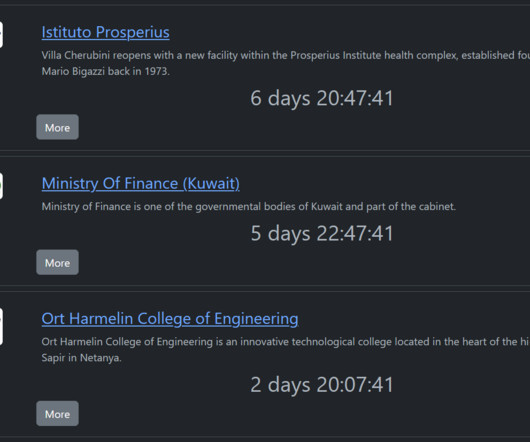
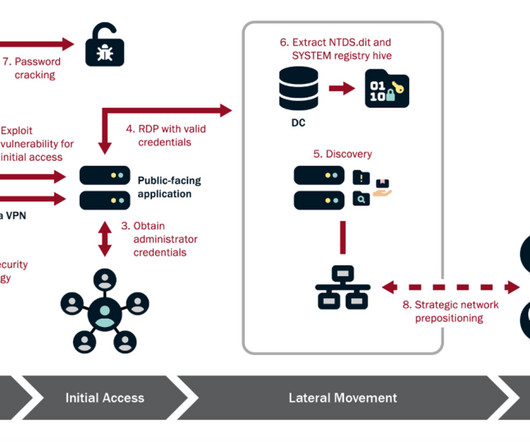
Security Affairs
NOVEMBER 15, 2023
The ransomware gang hit organizations in multiple industries, including the education, healthcare, manufacturing, information technology, and government sectors. PuTTY.exe Rhysida actors have been observed creating Secure Shell (SSH) PuTTy connections for lateral movement. The victims of the group are “targets of opportunity.”
eSecurity Planet
DECEMBER 19, 2023
Infrastructure as a service security is a concept that assures the safety of organizations’ data, applications, and networks in the cloud. Understanding the risks, advantages, and best practices connected with IaaS security is becoming increasingly important as enterprises shift their infrastructure to the cloud.

The Last Watchdog
JANUARY 23, 2024
Throughout the week, NCA will emphasize the critical significance of digital privacy for both consumers and businesses through a series of educational webinars featuring experts from various industries. “Knowing how to safeguard your personal information has never been more important than it is today.

Security Affairs
FEBRUARY 13, 2022
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs free for you in your email box. The post Security Affairs newsletter Round 353 appeared first on Security Affairs. US seizes $3.6 US seizes $3.6 Pierluigi Paganini.

OpenText Information Management
MARCH 18, 2024
Our complimentary event will be held in three locations: London (Queen Elizabeth II Centre, April 15), Munich (MOC—Event Center Messe München, April 16 & 17), and Paris (Maison de la Chimie, April 18). Here are just a few additional reasons to join us in-person for a jam-packed event in one of these beautiful cities. #5

eSecurity Planet
AUGUST 22, 2023
Remote access security is critical for protecting increasingly distributed work environments, ensuring that only authorized users can access your valuable information regardless of their location. The technologies for secure remote access can range from VPNs and multi-factor authentication to more advanced access and zero trust controls.

Thales Cloud Protection & Licensing
OCTOBER 4, 2022
Historically, October has always been an important month for the cybersecurity community and a month of major cybersecurity events. How much do they trust industries to keep their sensitive data secure? So in 2004, the President of the United States designated October as Cybersecurity Awareness Month. Use strong passwords.
Security Affairs
JANUARY 22, 2024
Attackers often exploit current events or emergency situations to elicit emotional responses and induce victims to act hastily without carefully evaluating the legitimacy of the communications. He is also the author of the book “La Gestione della Cyber Security nella Pubblica Amministrazione”.
Security Affairs
MAY 14, 2023
Every week the best security articles from Security Affairs are free for you in your email box. Nominate Pierluigi Paganini and Security Affairs here here: [link] Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. We are in the final !

The Last Watchdog
FEBRUARY 11, 2024
Related: The case for augmented reality training Because of this, cybersecurity investments and regulatory oversight are increasing at an astounding rate , especially for those in the financial services industry, bringing an overwhelming feeling to chief compliance officers without dedicated security teams. The list goes on.

IT Governance
FEBRUARY 14, 2024
The benefits of partnering with us, and our partner-exclusive event IT Governance launched its partner programme in 2017, which now includes more than 400 organisations. What else can partners expect from the event? The main objective is to educate their sales teams about new products and/or services.
Security Affairs
FEBRUARY 28, 2023
Gmail client-side encryption (CSE) is now available for Workspace Enterprise Plus, Education Plus, and Education Standard customers. Google announced that Gmail client-side encryption (CSE) is now available for all Google Workspace Enterprise Plus, Education Plus, and Education Standard customers.

Dark Reading
OCTOBER 1, 2018
Cybersecurity Month at Dark Reading is packed with educational webinars, from data breach response to small business security.

HL Chronicle of Data Protection
MARCH 29, 2019
Please join us for our April events. Nicola Fulford and James Denvil will speak at the workshop,” Trust in data, no longer a luxury – Privacy, security, and consumer trust for 21st century,” at the Luxury Law London Summit. International Privacy + Security Forum. Trust in data, no longer a luxury?

eSecurity Planet
OCTOBER 16, 2023
Public cloud security refers to protections put in place to secure data and resources in cloud environments shared by multiple users or organizations. Major cloud service providers have generally had good security , so cloud users can be pretty confident in the security of their data and applications if they get their part right.
Security Affairs
FEBRUARY 8, 2024
In the most recent campaign, the group targeted organizations in the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors. The APT group is using almost exclusively living-off-the-land techniques and hands-on-keyboard activity to evade detection.

IT Governance
DECEMBER 9, 2021
Cloud security is an essential part of today’s cyber security landscape. To mitigate these risks, the NCSC (National Cyber Security Centre) created the Cloud Security Principles , which outline 14 guidelines for protecting information stored online.

The Last Watchdog
APRIL 13, 2022
Cybersecurity and Infrastructure Security Agency (CISA) has started a campaign to increase awareness of these risks to U.S. Educate your employees on threats and risks such as phishing and malware. Therefore, educating your employees about the importance of security to your network is critical. The efficacy of hygiene.

The Last Watchdog
SEPTEMBER 25, 2023
If you’re a small business looking for the secret sauce to cybersecurity, the secret is out: start with a cybersecurity policy and make the commitment to security a business-wide priority. Taurins It’s also essential your business evaluates its technology and keeps it regularly updated to the latest security standards. Stay educated.
Security Affairs
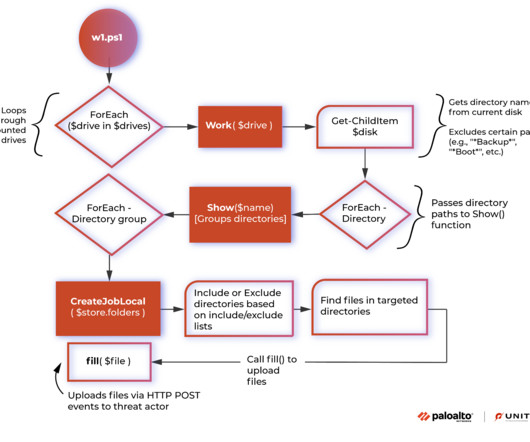
APRIL 17, 2023
Threat actors are using the PowerShell tool to evade software and/or human-based security detection mechanisms. Unit42 researchers were able to recover the script from the Windows Event Log (WEL). “each HTTP POST event will include the file’s full path.

Security Affairs
NOVEMBER 29, 2022
In today’s technological world, educating people about cybersecurity awareness is an absolute necessity. Due to the increasing use of digital tools for business operations and reliance on employee conduct to ensure security, new solutions are required. In service of that end, gamification is a highly effective tactic.

The Last Watchdog
APRIL 17, 2023
Even the most well-protected companies can be susceptible to attacks if they are not careful about a proactive approach towards cyber security. Here are a few of the top security weaknesses that threaten organizations today: Poor risk management. Vulnerability management is another key consideration when it comes to security.
eSecurity Planet
MARCH 15, 2024
From analyzing attack methods and suggesting defense tactics to doing vulnerability assessments, it provides users with the knowledge to improve their security posture. Aside from ethical hacking, HackerGPT seeks to assist professionals and improve security assessments. It has an intuitive UI similar to ChatGPT.

Adam Levin
AUGUST 26, 2020
Schools and companies should consider the following: Set up accounts with competing services: While Zoom holds a dominant position, it is by no means the only video conferencing platform for meetings or for education. If your school or educator hasn’t provided these, check online for one of several free resources for education. .

eSecurity Planet
AUGUST 22, 2023
Cybersecurity can be difficult to implement, and to make matters worse, the security professionals needed to do it right are in short supply. Managed IT security service providers (MSSPs) make life easier for organizations by providing outsourced expertise and tools at a fraction of the cost, time, and trouble of doing it yourself.

Security Affairs
APRIL 19, 2024
In the most recent campaign, the group targeted organizations in the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors. The APT group is using almost exclusively living-off-the-land techniques and hands-on-keyboard activity to evade detection.

The Last Watchdog
OCTOBER 5, 2023
The grants are part of the state’s SOC/Range Initiative, a program managed by MassTech’s MassCyberCenter that aims to help build a diverse generation of cybersecurity professionals through education, training, and workforce development. Preparation, communication, and active monitoring are key to defending against online attacks.” “The
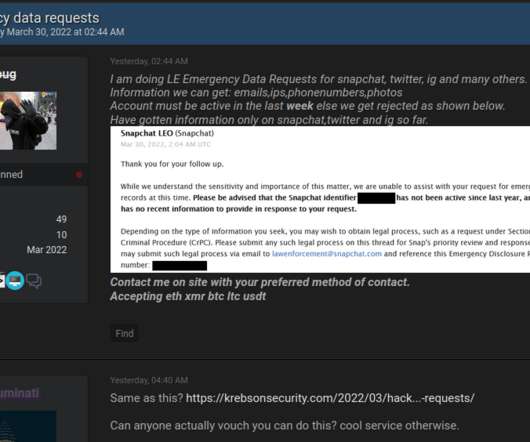
Krebs on Security
MARCH 31, 2022
“Recent news reports have revealed an enormous threat to Americans’ safety and national security,” Wyden said in a statement provided to KrebsOnSecurity. This post will be updated in the event they respond. Ron Wyden (D-Ore.), who said he was moved to action after reading this week’s coverage.

Security Affairs
MAY 2, 2023
US Cybersecurity and Infrastructure Security Agency (CISA) added TP-Link, Apache, and Oracle vulnerabilities to its Known Exploited Vulnerabilities catalog. The vulnerability was first reported to ZDI during the Pwn2Own Toronto 2022 event. in TP-Link Archer AX21 Wi-Fi routers.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content