GUEST ESSAY – Notable events in hacking history that helped transform cybersecurity assessment
The Last Watchdog
SEPTEMBER 27, 2021
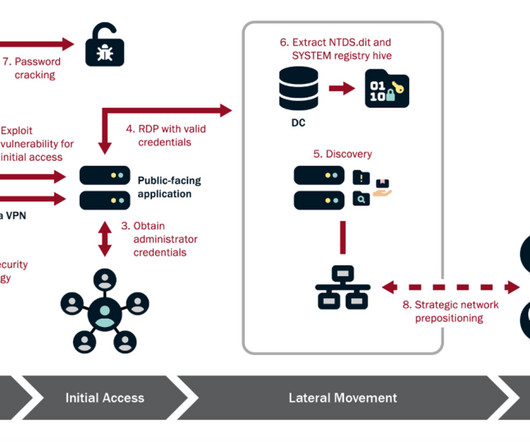
To minimize their impact, implementing preventive security measures into these advanced systems is crucial. Businesses across all industries can function adequately without worrying about would-be hackers with malicious intent when they secure their networks. Related: How Russia uses mobile apps to radicalize U.S. As a result, the U.S.



































Let's personalize your content