UK Nuclear Cleanup Site Faces Criminal Cybersecurity Charges
Data Breach Today
MARCH 29, 2024
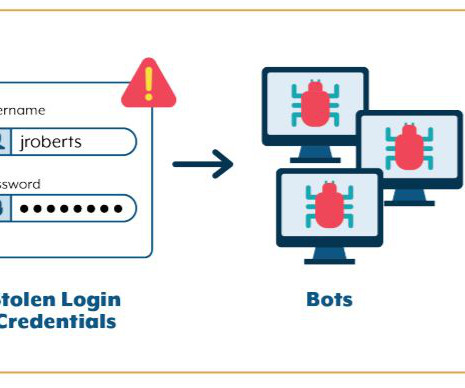
Probe Finds 'Largest and Most Hazardous Nuclear Site' Violated Security Laws Britain's nuclear power watchdog said it plans to prosecute the country's "largest and most hazardous nuclear site," Sellafield, for violating nuclear industry cybersecurity regulations from 2019 to 2023. Both Russian and Chinese nation-state hackers reportedly infiltrated the site's networks.









































Let's personalize your content