Federal Government is Excelling at Digital Transformation While Security Challenges Gain Ground
Thales Cloud Protection & Licensing
APRIL 21, 2020
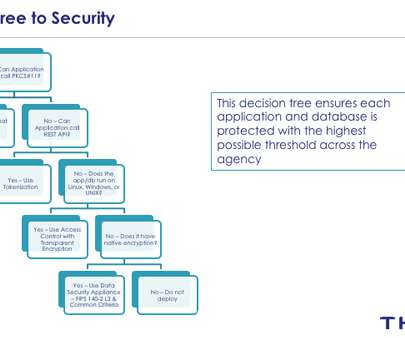
federal government contends with a tidal wave of demands in the COVID-19 battle, agencies are pushed to unprecedented limits. government is excelling with digital transformation (DX) which is critical in this time of crisis as the cloud becomes a crucial dynamic with the world working remotely. As the U.S.










































Let's personalize your content