What Is Data Loss Prevention (DLP)? Definition & Best Practices
eSecurity Planet
MARCH 29, 2024
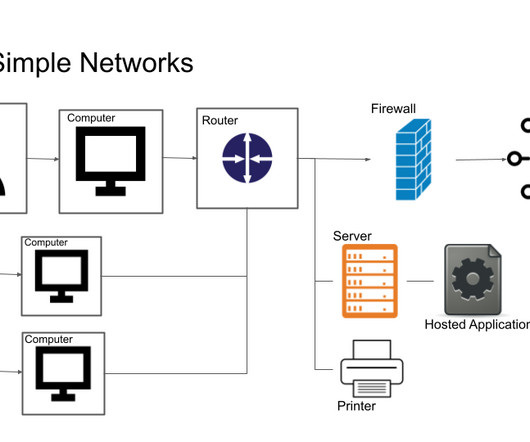
Data loss prevention (DLP) refers to a set of security solutions that identify and monitor information content across storage, operations, and networks. DLP solutions help detect and prevent potential data exposure or leaks. DLP integrates procedures, technology, and people to effectively detect and prevent sensitive data leaks.













































Let's personalize your content