US Government And Allies Disrupt Massive Russian Botnet
Data Breach Today
JUNE 18, 2022
Botnet Targets IoT And Android Devices; Industrial Control Systems And Computers The U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
JUNE 18, 2022
Botnet Targets IoT And Android Devices; Industrial Control Systems And Computers The U.S.

Thales Cloud Protection & Licensing
MAY 31, 2021
Use cases of secure IoT deployment. In our previous blog post , we discussed the challenges for securing IoT deployments, and how businesses and consumers benefit from authenticating and validating IoT software and firmware updates. Tue, 06/01/2021 - 06:55. Use case 1: Fortune 500 Healthcare Company. Use case 2: Automobiles.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
MAY 4, 2021
CryptoAgility to take advantage of Quantum Computing. The same goes with the advent of Quantum Computing , which is supposed to bring exponential computing power that shall not only bring endless benefits but also raises question marks on the current state of cryptography that is the bedrock of all information security as we know today.
eSecurity Planet
NOVEMBER 1, 2021
The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices. In addition, the amendment also will ensure greater privacy of personal data, prevent financial fraud, and improve resilience in European communications networks, according to EU officials.

Thales Cloud Protection & Licensing
MARCH 10, 2021
What’s driving the security of IoT? Connectivity enables powerful, revenue-generating capabilities…from data telemetry and runtime analytics, to effectively predicting and maintenance requirements. First off, connected vehicles and IoT devices are highly attractive targets to hackers. Guest Blog: TalkingTrust.

Thales Cloud Protection & Licensing
SEPTEMBER 12, 2018
The Internet of Things (IoT) is rapidly growing and expected to affect all industry verticals as well as our private lives. In this blog, we reached out to our technology partner Nexus to better understand the challenges that the industry faces to ensure safe deployment and management of IoT technologies. Weak authentication.

Security Affairs
JULY 23, 2021
Estonian hacker Pavel Tsurkan has pleaded guilty in a United States court to the counts of computer fraud and of creating and operating a proxy botnet. The Estonian national Pavel Tsurkan has pleaded guilty in a United States court to two counts of computer fraud and abuse. ” reads the press release published by DoJ. . .
Security Affairs
FEBRUARY 2, 2024
Furman for crimes of espionage, computer hacking, contempt of Court, making false statements to the FBI, and child pornography.” The huge trove of data, called “ Vault 7 ,” exposed the hacking capabilities of the US Intelligence Agency and its internal infrastructure. District Judge Jesse M.

eDiscovery Daily
DECEMBER 1, 2021
As a vital part of the Electronic Discovery Reference Model (EDRM) , any data collected is done so with the intent to capture it exactly as intended or as it was actively being used. This ensures the searchability and traceability of your data so it can be properly collected, indexed, and documented for use in litigation.

The Last Watchdog
NOVEMBER 16, 2020
Related: How Multi Party Computation is disrupting encrypti on An accomplished violinist, Einstein, no doubt, appreciated the symmetry of his metaphor. And the risk factors will only rise exponentially as reliance on cloud infrastructure and Internet of Things (IoT) systems accelerates.

ARMA International
JUNE 11, 2019
Edge computing is increasingly associated with at least two “trending” terms in the IT and information arenas: Internet of Things (IoT) and artificial intelligence (AI). Broadly speaking, the term refers to computing that’s done at or near the source of the data. back to the enterprise.”.

The Security Ledger
NOVEMBER 6, 2018
In this episode of the podcast, #119: Electronic Frontier Foundation General Counsel Kurt Opsahl joins us to talk about the Coders’ Rights Project. Also: we speak with Senthil Ramakrishnan, a lead member of AT&T’s IoT Security group about that company’s plans to work with Ericsson to certify the security of IoT devices.

The Last Watchdog
MAY 23, 2022
Related: Leveraging PKI to advance electronic signatures. It used to be that trusting the connection between a workstation and a mainframe computer was the main concern. And automation already is being leveraged to assure that an object hasn’t been tampered with, as well as ensure the encryption of data in transit – at scale.

The Last Watchdog
NOVEMBER 30, 2018
Intelligent computing systems have been insinuating themselves into our homes and public gathering places for a while now. Grimm CEO Brain Demuth told me he hopes the work Grimm has commenced in Sparta will also contribute to generally elevating the security of all types of IoT systems. Get ready for smart ground transportation.

DLA Piper Privacy Matters
OCTOBER 7, 2021
The Middle East’s data protection regulatory landscape is complex, and continues to develop with Saudi Arabia’s ( KSA ) newly published Personal Data Protection Law ( PDPL ). While the PDPL contains the main features of a modern data protection law, it cannot be considered a direct analogue of the GDPR. Deceased’s data.

Thales Cloud Protection & Licensing
JULY 20, 2023
3 Ways to Protect Smart Devices from Criminal Exploits madhav Thu, 07/20/2023 - 07:28 When people think of home or business security, they are usually worried about protecting against a physical breaking in via a window or door and a burglar stealing valuables such as jewelry, cash, electronics, and equipment.

The Security Ledger
JANUARY 8, 2019
In this episode of The Security Ledger podcast (#128): you're going to hear a lot from the annual Consumer Electronics Show (CES) out in Las Vegas this week, but are any of the new gadgets being released secure? And do security and privacy have a seat at the table at the world's largest electronics event? Read the whole entry. »

AIIM
SEPTEMBER 12, 2018
Data Privacy and Open Data: Secondary Uses under GDPR. Mitigate Data Privacy and Security Risks with Machine Learning. GDPR and Cross Border Data Flows between the EU and the US: Current State of the Law. GDPR Compliance Starts with Data Discovery. GDPR and the Data Governance Imperative.
ARMA International
FEBRUARY 21, 2020
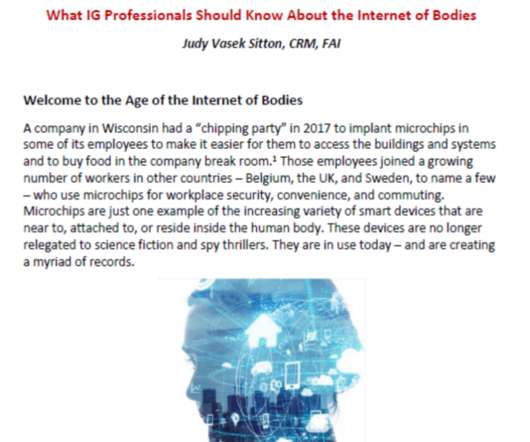
According to futurist Bernard Marr, [2] “The Internet of Bodies (IoB) is an extension of the IoT (Internet of Things) and basically connects the human body to a network through devices that are ingested, implanted, or connected to the body in some way. Types of Devices and What They are Gathering. Body-inserted devices (“embeddables”).

eDiscovery Daily
MARCH 20, 2019
; o ) While I’m speaking at the University of Florida E-Discovery Conference today, let’s take a look at a couple of articles related to Internet of Things (IoT) devices that you need to know from an eDiscovery standpoint. noted IoT devices may have multiple data repositories, which creates more data for attorneys to review.

IBM Big Data Hub
MAY 23, 2023
The rise of interconnected technologies like the Internet of Things (IoT), electric vehicles, geolocation and mobile technology have made it possible to orchestrate how people and goods flow from one place to another, especially in densely-packed urban areas. The solution is smart transportation.
eSecurity Planet
NOVEMBER 4, 2021
The unranked list contains 12 entries that categorize data found in hardware programming, design, and architecture. Hackers can exploit these weaknesses to compromise computer systems, exfiltrate data, and even perform DDoS attacks. See our picks for the Top Vulnerability Management Tools. The full MITRE-CWE list.

Krebs on Security
OCTOBER 12, 2018
BK: But certainly there are some areas of computer hardware and network design where you absolutely must have far greater integrity assurance? Of course, some nations have more capability than others to sift through huge amounts of data they’re collecting. TS: Like a lot of things in security, the economics always win.

Thales Cloud Protection & Licensing
AUGUST 31, 2022
Organizations in the finance sector manage trillions of dollars and maintain very valuable and vital electronic data, including bank account, credit card, and transaction information as well as sensitive data related to estates, wills, titles, and other matters. Data security challenges. Thu, 09/01/2022 - 05:15.

Security Affairs
SEPTEMBER 23, 2018
Google Android team found high severity flaw in Honeywell Android-based handheld computers. Amazon is investigating allegations that its staff is selling customer data. Evolution of threat landscape for IoT devices – H1 2018. Magecart cybercrime group stole customers credit cards from Newegg electronics retailer.

eSecurity Planet
FEBRUARY 13, 2023
Application security is the practice of securing software and data from hackers, whether that application comes from a third party or was developed in house, regardless of where it resides or how it’s accessed. Implement secure server configurations to maintain security and privacy of websites and protect private and sensitive data.

Reltio
JUNE 20, 2019
Henrik Liliendahl is an MDM and PIM expert; speaker and blogger ( www.liliendahl.com and [link] ) and the Co-Founder, Chairman and CTO of Product Data Lake a product information exchange service. We didn’t even have a computer at that school so the whole class was about things drawn on the blackboard. Kate Tickner, Reltio.

Reltio
OCTOBER 20, 2019
Henrik Liliendahl is an MDM and PIM expert; speaker and blogger -- Liliendahl on Data Quality and The Disruptive MDM/PIM/DQM List -- and the Co-Founder, Chairman and CTO of Product Data Lake a product information exchange service. Then one day we had a trip to a larger college that actually had computers and I was hooked!

IBM Big Data Hub
MAY 26, 2023
Cloud computing offers the potential to redefine and personalize customer relationships, transform and optimize operations, improve governance and transparency, and expand business agility and capability. In 2017, 94% of hospitals used electronic clinical data from their EHR.

ARMA International
SEPTEMBER 13, 2021
Some technology trends such as real-time data analytics are on-going, while others are more recent, such as blockchain. This means imaging the “art of the possible” for a new future using a cloud computing model to deliver transformative change. So, at the outset, a good question to ask is What is DT ?

Thales Cloud Protection & Licensing
AUGUST 28, 2018
We attended the show with our colleague Paul Cleary and sat in on many talks (and demos) ranging from attacking IoT devices over insecure Bluetooth connections, to exploiting publically available expired certificates. Our favorite presentation was a talk called “Reaping and Breaking Keys at Scale: When Crypto Meets Big Data.”

eDiscovery Daily
JANUARY 18, 2018
Tom also wrote a terrific four part informational overview on Europe’s General Data Protection Regulation (GDPR) titled eDiscovery and the GDPR: Ready or Not, Here it Comes. Anyway, this week’s eDiscovery Tech Tip of the Week is about Early Data Assessment. Issues Managing ESI Data in Criminal Cases. How Data is Acquired.

ARMA International
NOVEMBER 12, 2019
AI refers to computer systems that are able to perform tasks that are considered to require human intelligence – that is, cognitive tasks. With the explosion of data (big data), statistical approaches to AI found greater success. ML algorithms require sufficient data inputs and some form of training. Definitions of AI.

ARMA International
SEPTEMBER 22, 2021
Some technology trends such as real-time data analytics are on-going, while others are more recent, such as blockchain. This means imagining the “art of the possible” for a new future using a cloud computing model to deliver transformative change. The “Art of the Possible” for the End-state.

eSecurity Planet
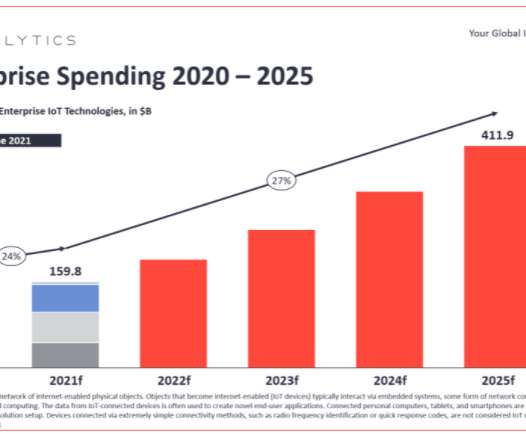
SEPTEMBER 1, 2021
Exposing the Internet of Things (IoT) Universe. Consumer electronics, business, network appliances, and industrial IoT (IIoT) devices are all driving the exponential growth of IoT systems. IoT products are notoriously vulnerable appliances because the build prioritizes ease of use and connectivity.

eDiscovery Daily
MARCH 25, 2018
A frequent court appointed special master in electronic evidence, Craig is a prolific contributor to continuing legal and professional education programs throughout the United States, having delivered over 2,000 presentations and papers. I don’t understand why they lump blockchain in with IoT? Today’s thought leader is Craig Ball.

The Security Ledger
JULY 10, 2018
» Related Stories Episode 100: Estonia’s Former CIO talks about engineering a secure electronic vote Fitness apps: Good for your health, not so much for military security Episode 101: The Dystopian IoT looks a lot like the Printer Ink Aisle and City of Atlanta Employees phished on Rogue Wi-Fi. Read the whole entry. »

eDiscovery Daily
SEPTEMBER 30, 2018
As a development partner in the Relativity ecosystem , CloudNine will once again be the conference and will be there to provide demonstrations of our Outpost for Relativity capability that automatically ingests and loads data into Relativity based on your specified criteria. This session has been submitted for CLE accreditation. Ball, P.C.

Bill Schmarzo - Dell EMC
JANUARY 31, 2018
Doctors can effectively treat patients without a high performance computer or an expensive technology environment. Whether we know it or not, we have all become “Citizens of Data Science,” and the world will never be the same. They just need the same iPhone that you and I use every day. Figure 1: Derm Expert App.

Privacy and Cybersecurity Law
MAY 19, 2017
.” In the report, the GAO provides an introduction to the Internet of Things (IoT), describes what is known about current and emerging IoT technologies, and examines the implications of their use. Technological Advancements Leading To IoT Surge. Cloud computing. Data analytics. Ubiquitous connectivity.

eSecurity Planet
AUGUST 13, 2021
For everything from minor network infractions to devastating cyberattacks and data privacy troubles , digital forensics software can help clean up the mess and get to the root of what happened. The Sleuth Kit enables administrators to analyze file system data via a library of command-line tools for investing disk images.

ForAllSecure
NOVEMBER 9, 2022
A sophisticated set of encryption and electronics is at work inside the vehicle. As more and more automotive manufacturers start incorporating computer technology into their expensive BMWs, Mercedes Ferraris and Porsches. Lacking any formal computer training. And for the most part, this is true. He told the Prague post.

eDiscovery Daily
MARCH 13, 2018
They understand that there’s some computer technology in play. Clearly, one of the things the new GDPR regulation is doing is making just a minimal touch enough for the European states to claim jurisdiction on the data, so I think you really need to take a long look at that. I’m not posting data over there.

IBM Big Data Hub
JANUARY 29, 2024
A recent analysis from the IBM Institute for Business Value asked company executives “[…] how they use data to create performance baselines and to understand how applying technologies—for example, cloud, AI, generative AI—might materially improve performance in the parts of the business that generate income.”
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content