Nexx bugs allow to open garage doors, and take control of alarms and plugs
Security Affairs
APRIL 5, 2023
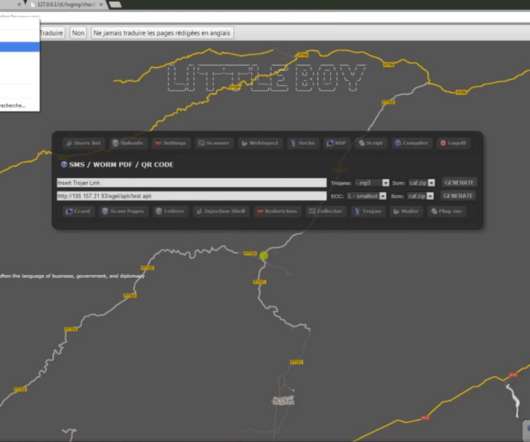
A series of vulnerabilities in multiple smart devices manufactured by Nexx can be exploited to remotely open garage doors, and take control of alarms and plugs. Below is a video demo published by the researcher that shows how to exploit the flaw CVE-2023–1748 to obtain users’ info.






























Let's personalize your content