Why Retailers Must Avoid Passwords
HID Global
APRIL 1, 2024
Discover how RFID reader technology revolutionizes retail with secure, passwordless authentication for enhanced efficiency and security. Learn more.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

HID Global
APRIL 1, 2024
Discover how RFID reader technology revolutionizes retail with secure, passwordless authentication for enhanced efficiency and security. Learn more.

Data Breach Today
JANUARY 27, 2023
FIDO Alliance's Hulka on Why Customers and Providers Like Payment Confirmation Payment regulations in Europe have forced retailers to implement strong authentication that's phishing-resistant and facilitates more customer understanding, says FIDO Alliance's Christina Hulka.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
NOVEMBER 22, 2022
Are Retailers Shopping for a Cybersecurity Breach? Retailers started the century as the prime targets for cyber attackers looking for credit card data. Today, unfortunately, retailers are again coming back to the spotlight. Similar to many organizations, 36% of retail respondents cited human error as the leading threat.
Thales Cloud Protection & Licensing
NOVEMBER 20, 2023
Black Friday and Cyber Weekend: Navigating the Tumultuous Waters of Retail Cybersecurity sparsh Tue, 11/21/2023 - 05:01 As global consumers gear up for the much-anticipated shopping bonanza that is Black Friday and Cyber Weekend, retailers brace themselves for the frenzied onslaught of shoppers and the deluge of cyber threats lurking in the shadows.

Security Affairs
APRIL 15, 2023
The Brazilian retail arm of car manufacturing giant Volvo leaked sensitive files, putting its clientele in the vast South American country in peril. Volvo’s retailer in Brazil, Dimas Volvo, leaked sensitive files through its website. website, belonging to an independent Volvo retailer in the Santa Catarina region of Brazil.

Thales Cloud Protection & Licensing
JANUARY 20, 2022
How to activate multifactor authentication everywhere. The impact of not having multifactor authentication (MFA) activated for all users is now well known by enterprises. The challenge of multifactor authentication everywhere. Variety of a user’s authentication journey…. Variety of a user’s authentication journey….

The Last Watchdog
JUNE 15, 2023
The World Wide Web Consortium today announced a standardization milestone for a new browser capability that helps to streamline user authentication and enhance payment security during Web checkout. Customer authentication For the past 15 years, e-commerce has increased as a percentage of all retail sales.

Thales Cloud Protection & Licensing
MAY 10, 2023
The Retail Data Threat Environment and Why CIAM is a Key Cornerstone to Better Cybersecurity. madhav Thu, 05/11/2023 - 06:06 The retail landscape has changed significantly. Customers should be aware of the existing threats, while retailers must understand the risks associated with poor management of customer identities.

Dark Reading
NOVEMBER 1, 2022
Retailers' new holiday jingle must hit cybersecurity high points to help survive the season. Forget Dasher and Dancer — add SAST and DAST to app testing; manage third-party risks; and use MFA along with training and proper authentication to secure credentials.

Security Affairs
NOVEMBER 25, 2020
Retail giant Home Depot has agreed to a $17.5 The US largest home improvement retailer giant Home Depot agrees to $17.5 According to the US retailer the payment card information of approximately 40 million Home Depot consumers nationwide. The post Retail giant Home Depot agrees to a $17.5 ” . . Pierluigi Paganini.

Thales Cloud Protection & Licensing
JANUARY 20, 2022
How to activate multifactor authentication everywhere. The impact of not having multifactor authentication (MFA) activated for all users is now well known by enterprises. The challenge of multifactor authentication everywhere. Variety of a user’s authentication journey…. Variety of a user’s authentication journey….

The Last Watchdog
APRIL 7, 2021
Passwordless authentication as a default parameter can’t arrive too soon. That’s the upshot of a new report, The State of Passwordless Security 2021 , put out by HYPR , a New York City-based supplier of advanced authentication systems. Related: Top execs call for facial recognition to be regulated. 1 use case is remote access.”.

Thales Cloud Protection & Licensing
JUNE 24, 2021
How FIDO 2 authentication can help achieve regulatory compliance. One common denominator in all regulations is the need for strong authentication. Strong authentication is the key to eliminate a large percentage of cyber-attacks, including those based on stolen credentials and subsequent credential stuffing.

Thales Cloud Protection & Licensing
OCTOBER 23, 2018
So before the shopping frenzy begins, we thought this would be an opportune time to outline some best practices that both retailers and consumers should follow in order to protect consumer data. As convenience technologies evolve, look for more risks to consumers and retailers. Protecting Consumer Data is Priority #1. Back to basics.

Troy Hunt
APRIL 14, 2024
However, per that story: Cybernews couldn’t confirm the authenticity of the data. I couldn't confirm the authenticity of the data either and I wrote a short thread about it during the week: I'm not convinced this data is from Accor. We reached out to Accor for clarification and are awaiting a response.

Thales Cloud Protection & Licensing
JANUARY 10, 2022
In the latest episode of Thales Security Sessions podcast , I was asked by Neira Jones to join Simon Keates, Head of Strategy and Payment Security at Thales and share my thoughts about the major security and organizational challenges retailers and other financial services organizations are facing. Pandemic has changed us all.
Thales Cloud Protection & Licensing
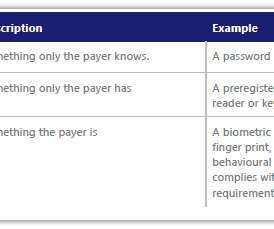
JANUARY 26, 2021
The Verizon DBIR 2020 report indicates that financially motivated attacks against retailers have moved away from Point of Sale (POS) devices and controllers, towards web applications. Figure 1: Web application breaches in the Retail industry. Strong Customer Authentication (SCA). Table 1: Strong Customer Authentication Factors.

Krebs on Security
OCTOBER 1, 2021
30 , the FCC said it plans to move quickly on requiring the mobile companies to adopt more secure methods of authenticating customers before redirecting their phone number to a new device or carrier. In a long-overdue notice issued Sept. ” The FCC said the proposal was in response to a flood of complaints to the agency and the U.S.

Thales Cloud Protection & Licensing
NOVEMBER 20, 2022
As the holiday season approaches, many retail, hospitality, logistics, and food manufacturing organizations hire seasonal workers to meet increasing demand. The Bureau of Labor Statistics reports a 7% job rise in the retail industry. How to Secure Access for your Seasonal Workers. Mon, 11/21/2022 - 05:36.
Thales Cloud Protection & Licensing
NOVEMBER 25, 2021
Many retailers and shipping services are planning to hire temporary workers for the upcoming holiday season. That’s 50,000 more seasonal employees than the retailer brought in at the end of 2020, noted CNBC. Many organizations already have robust authentication solutions in place for their permanent workers.

CGI
MAY 6, 2021
Product authenticity plays a huge role in assuring consumer confidence for B2B and B2C businesses. Correspondingly, for manufacturers and retailers, safeguarding the consumer experience and ensuring safety and trust are key to protecting the brand. Using blockchain to combat counterfeiting in manufacturing. ravi.kumarv@cgi.com.
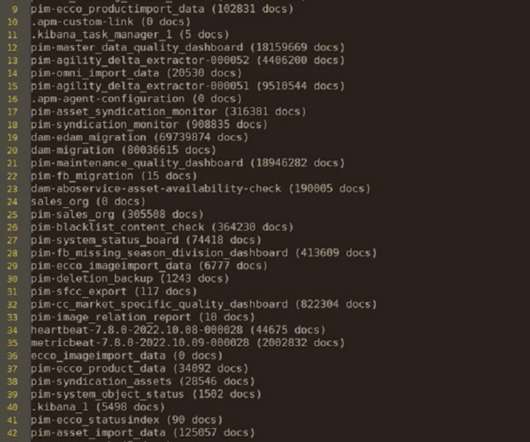
Security Affairs
DECEMBER 21, 2022
CyberNews researchers reported that Ecco, a global shoe manufacturer and retailer, exposed millions of documents. Ecco, a global shoe manufacturer and retailer, exposed millions of documents. Original post @ [link]. It’s no use carrying an umbrella if your shoes are leaking, an old Irish proverb says.

Krebs on Security
JULY 23, 2018
The basic model featured here retails for $20. Security Keys are inexpensive USB-based devices that offer an alternative approach to two-factor authentication (2FA), which requires the user to log in to a Web site using something they know (the password) and something they have (e.g., A YubiKey Security Key made by Yubico.

The Last Watchdog
MAY 3, 2021
ABE opens the door to an advanced form of the Public Key Infrastructure, or PKI , the system we use to encrypt data, as well as to authenticate individual users and the web servers they log onto. PKI revolves around the distribution of digital certificates to validate the authenticity of websites.
Security Affairs
MAY 2, 2023
FortiGuard Labs researchers observed a worrisome level of attacks attempting to exploit an authentication bypass vulnerability in TBK DVR devices. Threat actors are attempting to exploit a five-year-old authentication bypass issue, tracked as CVE-2018-9995 (CVSS score of 9.8), in TBK DVR devices.

Dark Reading
SEPTEMBER 14, 2021
Seventy-nine percent of people used two-factor authentication at least once in 2021, with 72% regularly using the technology, as remote work, social media, and online retail spur demand.

Security Affairs
FEBRUARY 10, 2022
Use strong multi-factor authentication methods such as biometrics, physical security tokens, or standalone authentication applications to access online accounts. Authenticate calls from third party authorized retailers requesting. Authenticate calls from third party authorized retailers requesting.

The Last Watchdog
SEPTEMBER 22, 2023
Benefits of PrivX •Eliminates static credentials with passwordless authentication and just-in-time access, enabling easy implementation of Zero Trust access management solution. We have 5,000+ customers worldwide, including 40 percent of Fortune 500 companies and major organizations in the Finance, Government, Retail, and Industrial segments.

Krebs on Security
SEPTEMBER 12, 2018
wireless carriers today detailed a new initiative that may soon let Web sites eschew passwords and instead authenticate visitors by leveraging data elements unique to each customer’s phone and mobile subscriber account, such as location, customer reputation, and physical attributes of the device. The four major U.S.

Security Affairs
AUGUST 9, 2021
Most of the attacks have been reported in July, the organizations hit by the ransomware gang operate in professional services, construction, manufacturing, retail, and food industries. Ransomware operators also stole data from the victims and leaked it online when they refused to pay the ransom. in Australia since 2020.

The Last Watchdog
SEPTEMBER 24, 2018
Already having our primary access points for code and infrastructure behind strong authentication requiring two factor authentication (2FA), we learned that SMS-based authentication is not nearly as secure as we would hope, and the main attack was via SMS intercept. This is because they are useful in targeting big companies.

Threatpost
OCTOBER 2, 2020
Account takeover fraud (ATO) attacks are on the rise, up nearly 300 percent since last year.

Security Affairs
NOVEMBER 18, 2019
Cyber security firm Venafi announced it has uncovered lookalike domains with valid TLS certificates that appear to target major retailers. The number is doubled compared to last year, the study revealed that less than 19,890 certificates have been issued for legitimate retail domains. retailers with over 49,500 typosquatted domains.
Krebs on Security
FEBRUARY 1, 2024
In a SIM-swapping attack, the crooks transfer the target’s phone number to a device they control, allowing them to intercept any text messages or phone calls sent to the victim, including one-time passcodes for authentication or password reset links sent via SMS.
Thales Cloud Protection & Licensing
NOVEMBER 15, 2023
Data sprawl Airports handle the identity records of a highly diverse population of employees, including hospitality, retail, security, and maintenance staff. For example, implementing multifactor authentication (MFA) through mobile authenticator apps is impossible in airport areas where smartphones are prohibited.
Security Affairs
OCTOBER 10, 2020
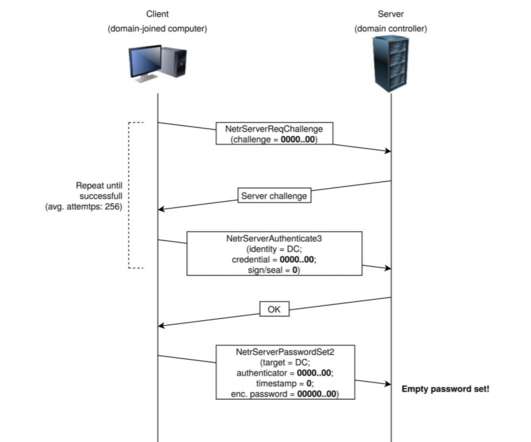
TA505 hacking group has been active since 2014 focusing on Retail and banking sectors. The Netlogon service is an Authentication Mechanism used in the Windows Client Authentication Architecture which verifies logon requests, and it registers, authenticates, and locates Domain Controllers.

Adam Levin
NOVEMBER 17, 2020
Mobile payment platforms, like Apple Pay and Google Pay, use advanced technology, like fingerprint authentication and tokenization (in which credit card account numbers are replaced by randomly generated numbers) to provide brick-and-mortar shoppers with an added layer of security. Shop at reputable and recognizable retailers.

Security Affairs
JANUARY 17, 2022
The IT giant pointed out that many of these vulnerabilities can be exploited by remote attackers without authentication. Oracle also urges its customers to apply Critical Patch Update patches as soon as possible due to the risk of exploitation of the addressed vulnerabilities. The highest CVSS v3.1 Base Score (10.0) Base Score of 9.9.

Thales Cloud Protection & Licensing
NOVEMBER 22, 2017
This year is expected to see similarly high numbers which is paralleled by increasing retailer anxiety about the state of their cybersecurity. In fact, according to our recent survey of retailers , 88% feel vulnerable to data threats. Almost 1 million visited physical stores.

IT Governance
NOVEMBER 23, 2023
In fact, in 2020–2022, the financial sector was the second-most attacked sector, topped only by the retail and manufacturing sector. That said, remember to consider risks to the confidentiality, integrity, availability and authenticity of each ICT asset: Confidentiality : The asset is accessible to authorised people only.

Adam Levin
APRIL 10, 2019
The analysis was conducted by the Aite Group, which looked at mobile apps in eight categories: retail banking, credit cards, mobile payment, healthcare savings, retail finance, health insurance, auto insurance and cryptocurrency.

Security Affairs
JANUARY 24, 2024
Impacted customers include Sweden’s largest cinema chain Filmstaden (the attack disrupted its online ticket system) and the discount retail chain Rusta. Tietoevry notified law enforcement and impacted customers.

Krebs on Security
AUGUST 12, 2018
. “The cyber criminals typically create fraudulent copies of legitimate cards by sending stolen card data to co-conspirators who imprint the data on reusable magnetic strip cards, such as gift cards purchased at retail stores,” the FBI warned.

Security Affairs
FEBRUARY 10, 2022
Use strong multi-factor authentication methods such as biometrics, physical security tokens, or standalone authentication applications to access online accounts. Authenticate calls from third party authorized retailers requesting. Use a variation of unique passwords to access online accounts. Pierluigi Paganini.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content