US CISA Aims to Expand Automated Malware Analysis Support
Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.

Data Breach Today
JANUARY 29, 2019
Around the world, many CIOs at various levels of governments expect an increase in cybersecurity spending in 2019, according to new research from Gartner. Alia Mendonsa, co-author of the report, analyzes the results of a global survey.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
FEBRUARY 16, 2024
CISA revealed that threat actors breached an unnamed state government organization via an administrator account belonging to a former employee. The government experts conducted an incident response assessment of the state government organization after its documents were posted on the dark web.

OpenText Information Management
MARCH 28, 2024
State carry out comprehensive assessments of their cybersecurity services and practices. Enter OpenText™, a trailblazing force in the realm of cybersecurity , with its cutting-edge Network Detection and Response (NDR). Attackers linked to Iran and China are actively targeting critical infrastructure. Both the U.S.

Adam Levin
JANUARY 9, 2019
Government has impacted federal cybersecurity according to several reports. The roughly 800,000 federal workers currently on furlough include: 45% of staff from the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency , which is tasked with defending critical infrastructure from cyber and physical threats.

Data Matters
MARCH 11, 2022
Securities and Exchange Commission (SEC) proposed new cybersecurity rules to enhance and standardize disclosures regarding cybersecurity risk management, strategy, governance, and incident reporting by public companies. Reporting material cybersecurity incidents within four days.

Data Protection Report
NOVEMBER 8, 2023
On November 1, 2023, the New York Department of Financial Services (“NYDFS”) released the finalized amendments of Part 500 of its cybersecurity regulations. This notice requirement explicitly applies to cybersecurity incidents occurring to the covered entity itself, its affiliates, or a third-party service provider.

The Last Watchdog
JUNE 13, 2022
At the start of this year, analysts identified a number of trends driving the growth of cybersecurity. Among them: an expanding digital footprint, growing attack surfaces, and increasing government regulation. billion in venture capital poured into cybersecurity companies globally. Related: Taking API proliferation seriously.

Hunton Privacy
JULY 5, 2023
On June 28, 2023, the New York Department of Financial Services (“NYDFS”) published an updated proposed Second Amendment (“Amendment”) to its Cybersecurity Regulation, 23 NYCRR Part 500. As described below, senior governing bodies would have new oversight responsibilities under the amendments.

Data Breach Today
SEPTEMBER 24, 2021
The latest edition of the ISMG Security Report features an analysis of how the U.S. government has been tracking an increase in the pace of attacks tied to Conti ransomware. Also featured are what "protection" means today and building a new cybersecurity operating model.
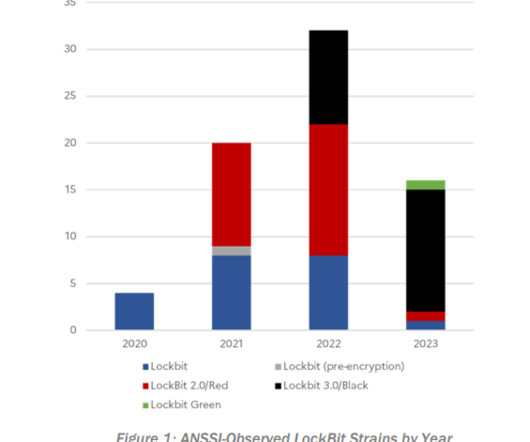
Security Affairs
JUNE 15, 2023
According to a joint advisory published by cybersecurity agencies, the LockBit ransomware group has successfully extorted roughly $91 million in about 1,700 attacks against U.S. 16% of the State, Local, Tribal, and Tribunal (SLTT) government ransomware incidents reported to the MS-ISAC is 2022 were LockBit attacks. law enforcement).
IBM Big Data Hub
SEPTEMBER 20, 2023
When implemented in a responsible way—where the technology is fully governed, privacy is protected and decision making is transparent and explainable—AI has the power to usher in a new era of government services. AI’s value is not limited to advances in industry and consumer products alone.
Security Affairs
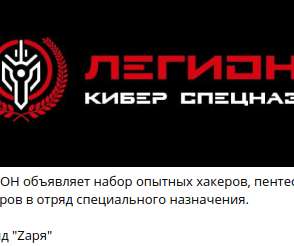
JUNE 6, 2022
Following the attacks of the Killnet Collective, the group responsible for the attacks against major government resources and law enforcement, a new group has been identified called “Cyber Spetsnaz”.

The Last Watchdog
SEPTEMBER 6, 2022
Managed Security Services Providers have been steadily evolving for two decades; they now seem poised to help large enterprises and, especially, small to mid-sized businesses manage their cybersecurity. and one of its specialties is helping government contractors continuously monitor and manage their networks, systems and data.
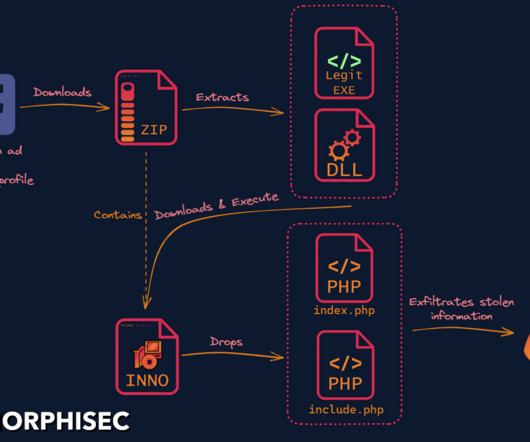
Security Affairs
MARCH 7, 2023
Researchers discovered a new info stealer dubbed SYS01 stealer targeting critical government infrastructure and manufacturing firms. ” reads the analysis published by Morphisec. to lure victims into downloading a malicious file. .” ” concludes Morphisec that also provides indicators of compromise (IoCs).

eSecurity Planet
JUNE 21, 2022
” Also read: Cybersecurity Employment in 2022: Solving the Skills Gap. “Certifications range from penetration testers , government/industry regulatory compliance , ethical hacking , to industry knowledge,” he said. Also read: How to Get Started in a Cybersecurity Career. The Top Cybersecurity Certifications.

The Last Watchdog
APRIL 13, 2022
These Russian cyber actors are government organizations and include other parties who take their orders from the Russian military or intelligence organizations – while not technically under government control. Cybersecurity and Infrastructure Security Agency (CISA) has started a campaign to increase awareness of these risks to U.S.
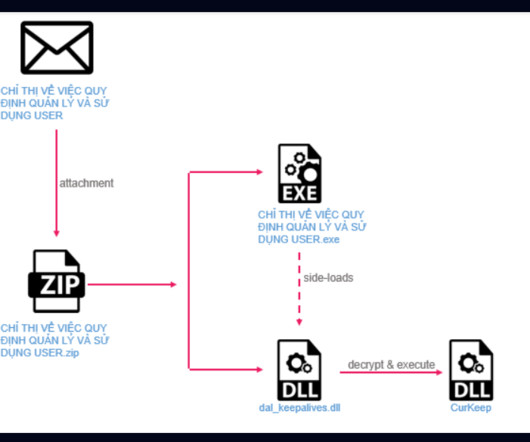
Security Affairs
OCTOBER 13, 2023
A cyberespionage campaign, tracked as Stayin’ Alive, targeted high-profile government and telecom entities in Asia. ” reads the analysis published by Checkpoint. The analysis of the C2 allowed the researchers to discover other loader variants used by the threat actor, such as CurLu, CurCore, and CurLog.

Security Affairs
AUGUST 26, 2021
Cybersecurity and Infrastructure Security Agency (CISA) released five malware analysis reports (MARs) related to samples found on compromised Pulse Secure devices. CISA published five malware analysis reports (MARs) related to samples found on compromised Pulse Secure devices. ” reads CISA’s advisory.
Security Affairs
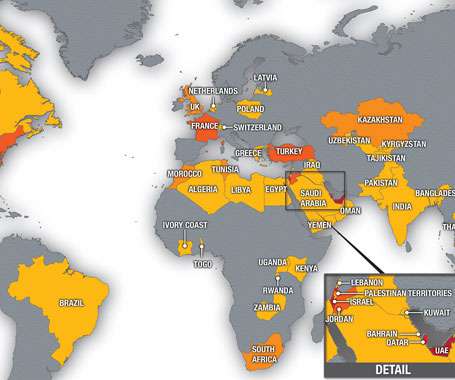
SEPTEMBER 20, 2021
Security researchers uncovered a large phishing campaign targeting multiple government departments in APAC and EMEA countries. . Researchers from cybersecurity firm Cyjax uncovered a large phishing campaign targeting multiple government departments in APAC and EMEA countries. . ” concludes the analysis.

The Last Watchdog
FEBRUARY 27, 2024
is now offering their cutting-edge cybersecurity services free of charge to all organizations for 30 days, irrespective of their current cybersecurity measures. ThreatHunter.ai, with its elite team of threat hunters, engineers, and cybersecurity experts, employs the ARGOS platform to provide real-time threat detection and mitigation.

eSecurity Planet
SEPTEMBER 23, 2022
Securities and Exchange Commission (SEC) strongly advised public companies to improve their cybersecurity. However, after minimal corporate adoption of stronger cybersecurity, the SEC has drafted rules to require more formal cybersecurity reporting and disclosure. See the top Governance, Risk & Compliance (GRC) tools.
Hunton Privacy
MARCH 11, 2022
On March 9, 2022, the Securities and Exchange Commission (“SEC”) held an open meeting and proposed new cybersecurity disclosure rules for public companies by a 3-1 vote. In proposing the rules, the SEC hopes to improve the consistency and comparability of cybersecurity disclosures among public companies. Key Definitions.
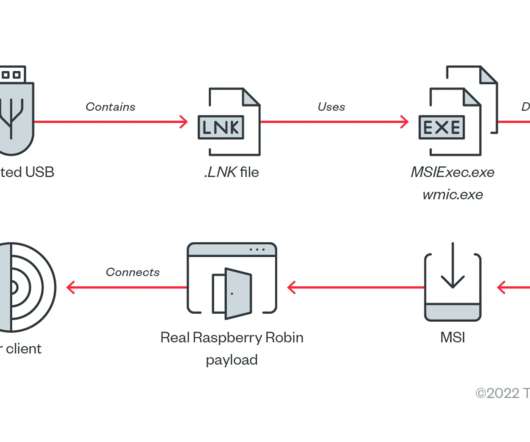
Security Affairs
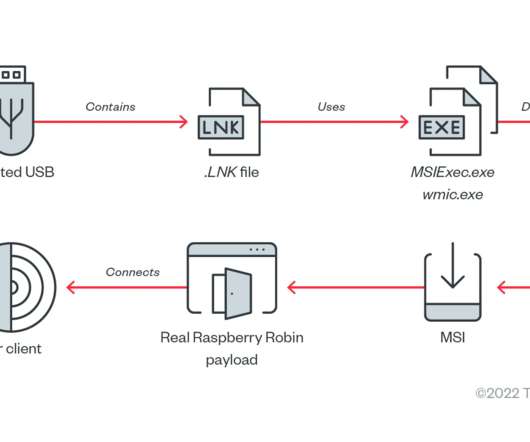
DECEMBER 24, 2022
The Raspberry Robin worm attacks aimed at telecommunications and government office systems across Latin America, Australia, and Europe. Researchers from Trend Micro have uncovered a Raspberry Robin worm campaign targeting telecommunications and government office systems across Latin America, Australia, and Europe. Pierluigi Paganini.

OpenText Information Management
FEBRUARY 25, 2021
The effects of the SolarWinds attack will be felt for a long time, and will ripple far beyond the government alone. Even though investigations and analysis of the discovered hack remain ongoing, it has become clear that the scope is extensive, and the full impacts will likely prove to be devastating.

eSecurity Planet
APRIL 23, 2021
To fill this gap and aid in the analysis, detection, and testing of malware, sandboxing is widely used to give organizations the setting, isolation, and security tools needed to preserve the integrity of the host network. In 2021, sandboxes are now a fundamental part of an organization’s cybersecurity architecture. Sandbox Features.
Security Affairs
JULY 19, 2021
Pegasus is a surveillance malware developed by the Israeli surveillance NSO Group that could infect both iPhones and Android devices, it is sold exclusively to the governments and law enforcement agencies. The evidence demonstrates that governments used Pegasus to intimidate journalists and critical media. Pierluigi Paganini.

Security Affairs
DECEMBER 27, 2021
Albania’s prime minister Edi Rama apologized for the massive leak of personal records from a government database of state. Albania’s prime minister this week apologized for the massive leak of personal records from a government database of state. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.
Security Affairs
APRIL 21, 2022
Threat intelligence firm Resecurity details how crooks are delivering IRS tax scams and phishing attacks posing as government vendors. Further analysis uncovered embedded scenarios detecting the victim’s IP (using GEO2IP module, deployed on a third-party WEB-site), likely done to selectively choose targets or to filter by region.

Security Affairs
DECEMBER 26, 2023
Cybersecurity company Resecurity has published the 2024 Cyber Threat Landscape Forecast. Resecurity, a Los Angeles-based cybersecurity company protecting Fortune 100 and government agencies worldwide, has compiled a comprehensive forecast outlining the imminent threats and novel security challenges anticipated in the upcoming year.

The Last Watchdog
OCTOBER 4, 2021
The Wharton School of the University of Pennsylvania observed that “nowhere is the workforce-skills gap more pronounced than in cybersecurity.”. This shortage is significantly impacting corporate America, and it is particularly dire across federal, state and local governments. Cybersecurity Ventures predicts that there will be 3.5

Security Affairs
APRIL 8, 2024
Greylock McKinnon Associates (GMA) provides expert economic analysis and litigation support to a diverse group of domestic and international clients in the legal profession, the business community, and government agencies, including the Department of Justice (DoJ). ” reads the data breach notification.

Security Affairs
AUGUST 4, 2022
Taiwan government websites were temporarily forced offline by cyber attacks during the visit to Taipei of US House Speaker Nancy Pelosi. Major Taiwan government websites were temporarily forced offline by distributed denial of service (DDoS) attacks attacks during the visit to Taipei of US House Speaker Nancy Pelosi.

erwin
OCTOBER 31, 2019
The Regulatory Rationale for Integrating Data Management & Data Governance. Now, as Cybersecurity Awareness Month comes to a close – and ghosts and goblins roam the streets – we thought it a good time to resurrect some guidance on how data governance can make data security less scary.
Security Affairs
JANUARY 30, 2024
This figure also includes historical records and new artifacts identified in January 2024, following an analysis of Command and Control (C2) servers and underground marketplaces. Resecurity has notified victims whose credentials were compromised by infostealers like Azorult , Redline , Vidar, Lumma, and Taurus and exposed on the Dark Web.

Security Affairs
APRIL 19, 2024
The security team at the organization promptly launched an investigation, logged out the threat actor, and engaged third-party forensics Incident Response teams to conduct independent analysis in collaboration with internal experts. The organization said that the core enterprise network or partners’ systems were not affected by this incident.

Security Affairs
MARCH 4, 2024
Threat actors stole sensitive information from the company, including military and government documents, revealed Taiwan’s Defense Ministry. TeraBytes of data” that included government contracts. Cybersecurity experts attribute the vast majority of these attacks to China-linked threat actors. ” reported AFP agency.

Security Affairs
JULY 7, 2022
The attacks against Healthcare and Public Health (HPH) Sector organizations started in May 2021 and government experts observed multiple cases that involved the use of the Maui ransomware. The joint report refers to an industry analysis of a sample of Maui provided in Stairwell Threat Report: Maui Ransomware.

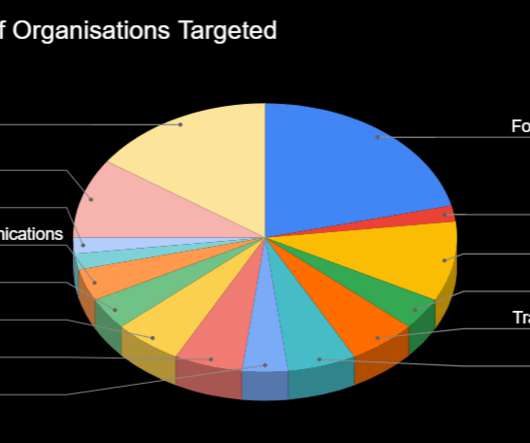
Security Affairs
DECEMBER 5, 2023
The insights presented herein result from a thorough mapping and analysis of DoS incidents spanning from January 2022 to August 2023. DoS attacks affect all sectors, government services are consistently the most targeted. An analysis of a total of 310 verified DoS incidents – from January 2022 to August 2023.

The Last Watchdog
NOVEMBER 14, 2023
Related: How ‘Internet Access Brokers’ fuel ransomware I happened to be in the audience at Stanford University when President Obama took to the stage to issue an executive order challenging the corporate sector and federal government to start collaborating as true allies. This strengthens the overall Windows ecosystem, Budd noted.

The Last Watchdog
JUNE 4, 2019
With the largest concentration of cybersecurity expertise –– the “oil” — in the world, Maryland is fast changing from the Old Line State into “Cybersecurity Valley.” There’s oil in the state of Maryland – “cyber oil.” The state counts approximately 109,000 cyber engineers.
eSecurity Planet
SEPTEMBER 8, 2023
Technology reviews can be a temptingly easy way to gain insight into the often impenetrable world of enterprise cybersecurity products, but you need to know how to use them. Organization type: corporate, education, utility, non-profit, government International regions: Asia, South America, North America, etc.
Security Affairs
DECEMBER 24, 2022
The Raspberry Robin worm attacks aimed at telecommunications and government office systems across Latin America, Australia, and Europe. Researchers from Trend Micro have uncovered a Raspberry Robin worm campaign targeting telecommunications and government office systems across Latin America, Australia, and Europe. Pierluigi Paganini.

Data Protection Report
MAY 25, 2022
Boards and organisations should assess their cybersecurity risk management activities in light of the decision and ask whether current approaches are adequately resourced and operating effectively? Despite these requirements, RI Advice’s ARs suffered nine cybersecurity incidents in the period from 2014 to 2021. Introduction.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content