LockBit Group Prepared New Crypto-Locker Before Takedown
Data Breach Today
FEBRUARY 22, 2024
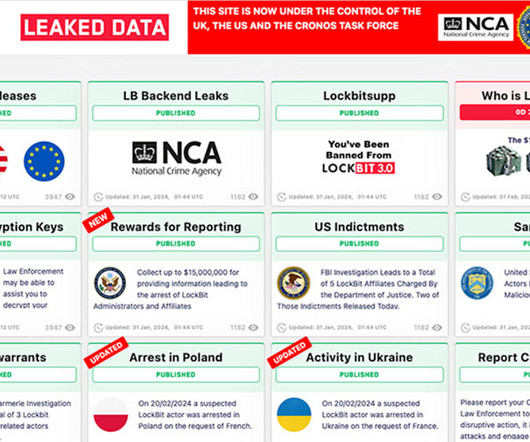
Numerous Impediments Remain If Administrators Attempt to Reboot the Operation The notorious ransomware-as-a-service group LockBit, disrupted by law enforcement this week, was developing a new version of its crypto-locking malware prior to being shut down, security researchers reported. Even so, experts say it's unlikely the group would be able to successfully reboot.



































Let's personalize your content