Google Stored G Suite Passwords in Plaintext Since 2005
Threatpost
MAY 22, 2019
Google said it had stored G Suite enterprise users' passwords in plain text since 2005 marking a giant security faux pas.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
 2005 Related Topics
2005 Related Topics 
WIRED Threat Level
MAY 21, 2019
On the heels of embarrassing disclosures from Facebook and Twitter, Google reveals its own password bugs—one of which lasted 14 years.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
FEBRUARY 9, 2023
CEO Change Marks First Time Since 2005 Someone Other Than Udi Mokady Is In Charge CyberArk will promote Matt Cohen, 47, to CEO on April 3.
Data Breach Today
NOVEMBER 23, 2022
Attackers targeted Boa servers, which were discontinued in 2005, to compromise Tata and other critical infrastructure organizations around the world.

Archives Blogs
OCTOBER 18, 2017
We are pleased to announce that after a significant transfer of records from the Revenue Services Department, the Archives can now make available property tax records up to 2005. 1978-1990 and 1992-2005: Property tax statements: series COV-S289. Map of assessment wards in the Municipality of Point Grey, with proposed changes, ~1927.

ChiefTech
MAY 23, 2012
I wrote this in June 2005. The history of intranets is one of a slow burn of adoption (or innovation, if you like). But the pace of technology change is increasing , email is being challenged. is it time now to dust off the intranet imperative and think about about where we go next? What exactly is an intranet?

Dark Reading
JANUARY 25, 2023
Zacks Elite sign-ups for the period 1999–2005 were accessed, including name, address, email address, phone number, and the password associated with Zacks.com.

Data Breach Today
NOVEMBER 15, 2017
The Final FFIEC Guidance has been issued and its main intent is to reinforce the 2005 Guidance's risk management framework and update the Agencies' expectations regarding customer authentication, layered security, or other controls in the increasingly hostile online environment.
KnowBe4
NOVEMBER 21, 2022
Then, in 2005 the clever people at the National Retail Federation decided that an online frenzy of shopping was needed the Monday after Thanksgiving. People arrived at the shops the night before waiting in line for the doors to open. We know this Monday as Cyber Monday.

Krebs on Security
JUNE 22, 2022
Stanx said he was a longtime member of several major forums, including the Russian hacker forum Antichat (since 2005), and the Russian crime forum Exploit (since April 2013). In an early post to Antichat in January 2005, Stanx disclosed that he is from Omsk , a large city in the Siberian region of Russia.

Krebs on Security
MAY 4, 2023
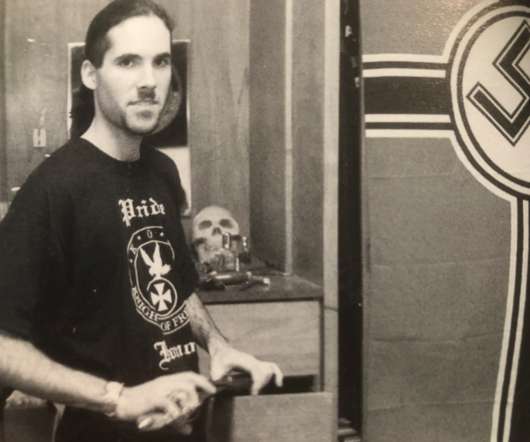
Launched in 2005, Try2Check soon was processing more than a million card-checking transactions per month — charging 20 cents per transaction. ” In February 2005, Nordex posted to Mazafaka that he was in the market for hacked bank accounts, and offered 50 percent of the take. Denis Kulkov, a.k.a. Image: USDOJ.
Krebs on Security
NOVEMBER 8, 2020
In 2005, AOL won a $12.8 Hawke had reportedly bragged about the money he earned from spam, but told friends he didn’t trust banks and decided to convert his earnings into gold and platinum bars. That sparked rumors that he had possibly buried his ill-gotten gains on his parents’ Massachusetts property.

Unwritten Record
MARCH 15, 2024
Beginning with the 2005 session, the Court implemented a digital audio recording system, and began transferring digital audio files to NARA for preservation and public access. From 1955 to 2004, the court recorded its proceedings onto 1/4” open reel analog tape.
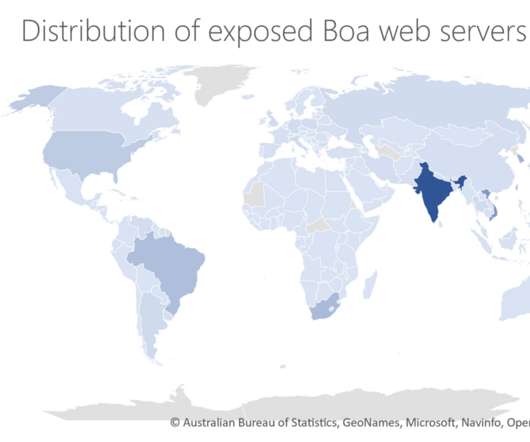
Security Affairs
NOVEMBER 24, 2022
The experts pointed out that Boa has been discontinued since 2005. ” Microsoft experts explained that despite Boa being discontinued in 2005, many vendors across a variety of IoT devices and popular software development kits (SDKs) continue to use it. ” reads the report published by Microsoft.

DXC Technology
APRIL 12, 2020
2005????????10???NIST???????????????????????????????????????????????????ICAS??????????????????????????????????????????????????????ICAS?????????????????????????????????????????FeliCa?????????????????????? FeliCa?????????????????????????????????????????????????????????????/???????????????????????????????????????????ICAS??????????? DXC Japan??ICAS?????????????2005??ICAS??????????????FeliCa????????????????????????.

Security Affairs
NOVEMBER 27, 2020
The hackers accessed company file servers that contained information about current and former employees from 2005 to 2020 and their beneficiaries and dependents. The investigation conducted by Canon found evidence of unauthorized accesses on its network between July 20 and August 6. ” reads the statement.

Hunton Privacy
JUNE 13, 2019
The adaption of French law to the new EU data protection framework was conducted in various stages: The French Data Protection Act of January 6, 1978, was first amended by a law dated June 20, 2018, while its implementing Decree of October 20, 2005, was amended by a Decree of August 1, 2018.
Hunton Privacy
JUNE 30, 2023
APEC CBPR and PRP operationalize the nine Privacy Principles set forth in the 2005 APEC Privacy Framework. The CBPR and PRP were developed originally as regional transfer mechanisms for APEC member economies.

Security Affairs
MARCH 27, 2022
The oldest flaws in the set of 66 recently added issues are dated back to 2005. The new vulnerabilities added to the catalog have to be addressed by federal agencies by April 15, 2022. Microsoft addressed this bug with the release of the February 2022 Patch Tuesday updates.
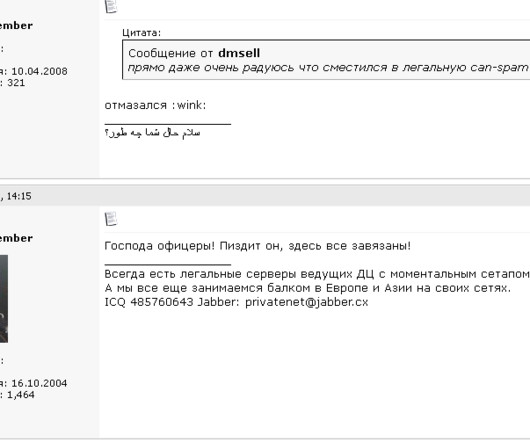
Krebs on Security
JANUARY 8, 2024
From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a From one of his ads in 2005: Domains For Projects Advertised By Spam I can register bulletproof domains for sites and projects advertised by spam(of course they must be legal). w s, icamis[.]ru ru , and icamis[.]biz.
Krebs on Security
JUNE 28, 2022
ru’s original WHOIS records, which shows it was assigned in 2005 to a “private person” who used the email address lycefer@gmail.com. ru)was registered in 2005 to two men, one of whom was named Dmitry Sergeevich Starovikov. And maybe that was the point. and starovikov[.]com.
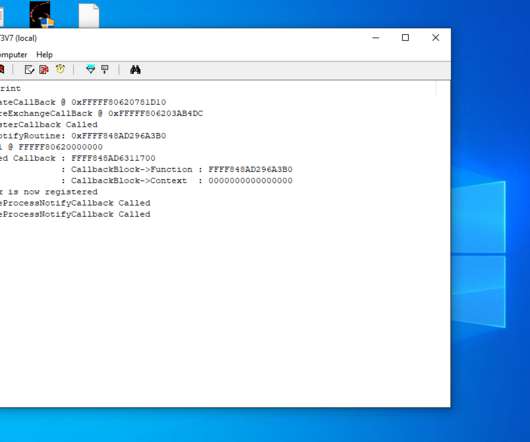
Security Affairs
MAY 31, 2021
The feature was first introduced in 2005 with the x64 editions of Windows XP and Windows Server 2003 Service Pack 1. Kento published technical details of its attack in a blog post and also released proof-of-concept (PoC) code for his attack.
Krebs on Security
SEPTEMBER 1, 2021
An ad circa 2005 for A311 Death, a powerful banking trojan authored by “Corpse,” the administrator of the early Russian hacking clique Prodexteam. Image: Google Translate via Archive.org.

Security Affairs
JANUARY 25, 2023
According to the notice, threat actors had access to an older database of customers who had signed up for the Zacks Elite product between November 1999 through February 2005. The company discovered the intrusion at the end of 2022, it believes the unauthorized access took place sometime between November 2021 and August 2022.

Adapture
SEPTEMBER 19, 2023
About Smartsheet Since its founding in 2005, Smartsheet enables individuals and teams to become high achievers by creating innovative work management solutions, mobilizing a passionate and diverse global team, and redefining the possibilities of work management, empowering people to do amazing things.

Adam Levin
MAY 24, 2019
Google announced a glitch that stored unencrypted passwords belonging to several business customers, a situation that had been exploitable since 2005. This issue has been fixed and, again, we have seen no evidence of improper access to or misuse of the affected passwords.

Schneier on Security
DECEMBER 14, 2018
I wrote about this exact attack in 2005 and 2009. In the event targets' accounts were protected by 2fa, the attackers redirected targets to a new page that requested a one-time password. This isn't new.

Security Affairs
JUNE 13, 2023
According to the notice, threat actors had access to an older database of customers who had signed up for the Zacks Elite product between November 1999 through February 2005. The company discovered the intrusion at the end of 2022, it believes the unauthorized access took place sometime between November 2021 and August 2022.
Security Affairs
APRIL 3, 2021
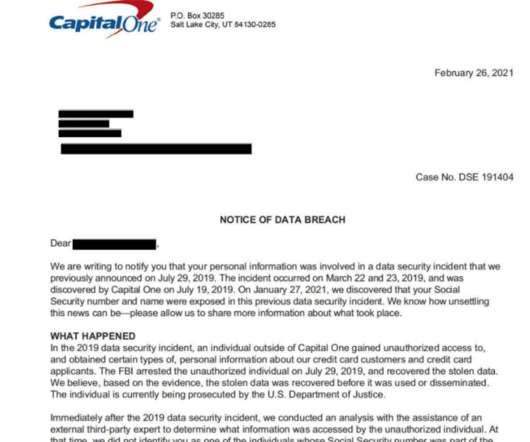
The security breach data breach took place on March 22nd and 23rd, the hacker accessed information of customers who had applied for a credit card between 2005 and 2019. District Court in Seattle. Based on our analysis to date, this event affected approximately 100 million individuals in the United States and approximately 6 million in Canada.

AIIM
NOVEMBER 30, 2017
But after 2005, these effects vanish from the measured statistics. Total productivity growth has fallen by two-thirds since 2005, while real GDP growth has averaged about 2 percent per year—all during a period in which the digital economy has continued to grow.”.

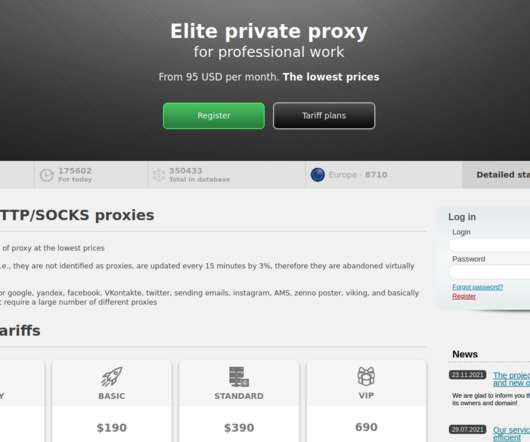
Security Affairs
MAY 3, 2023
The platform has been active since 2005, according to the DoJ, it generated tens of millions of dollars in revenue. Authorities dismantled the Try2Check platform, a Card-Checking platform that generated tens of millions of dollars in revenue. DoJ charged the Russian citizen Denis Gennadievich Kulkov with running the Card-Checking services.

The Schedule
DECEMBER 10, 2019
In 2005, two people working in Records and Archives at the World Health Organisation — Ineke Deserno and Donna Kynaston — had this to say about the intersection of records management and archival work: “A records management program is indispensable for an archives program. It ensures.
Security Affairs
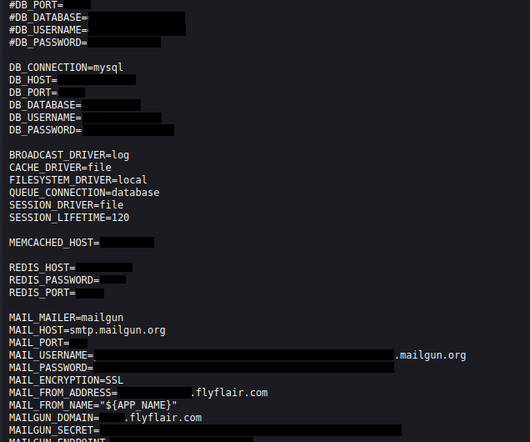
SEPTEMBER 26, 2023
Flyflair.com belongs to the Canadian ultra-low-cost carrier Flair Airlines, founded in 2005. The leak consisted of publicly accessible environment files hosted on the flyflair.com website. According to SimilarWeb, the website attracts 3.2 million monthly visitors.
Security Affairs
JULY 24, 2020
It was formed in 2005 in response to European Union requirements to separate the natural monopoly of infrastructure management from the competitive operations of running train services. The company has over 13,000 employees for a revenue of around $8 Billion.

Security Affairs
MAY 2, 2019
The good news is that most recent versions of SAP software are configured by default to drop unauthorized connections, Since 2005, SAP is providing instructions on how to configure an ACL for the Message Server. Experts pointed out that the problem could impact many SAP products, including S/4HANA and NetWeaver Application Server (AS).
Security Affairs
MARCH 28, 2023
million records dating back to at least 2005 were also compromised in the data breach. .” The company announced that it will reimburse those customers who choose to replace their stolen ID documents. The statement also reported that approximately 6.1 94% of these records (5.7 million) were provided before 2013.
Security Affairs
APRIL 19, 2020
” Webkinz were originally released by the Canadian toy company Ganz on April 29, 2005. Webkinz are stuffed animals that have a playable online counterpart, www.webkinz.com, in “Webkinz World.”

The Security Ledger
NOVEMBER 3, 2021
Programs like iDefense Labs Vulnerability Contributor Program (VCP) (launched in 2002) and TippingPoint’s Zero Day Initiative (2005) were accused -at the time- of incentivizing the work of criminals and bad actors. . When the first bugs for cash programs emerged almost two decades ago, they were controversial.
John Battelle's Searchblog
JANUARY 5, 2023
I’d argue we’ve already been in dialog with a semi-intelligent machine for decades – ever since the dawn of search, and certainly since the rise of Google, where every interaction is considered a “query” and every response a “result.”

Archives Blogs
JULY 24, 2020
Author Devery Anderson offered this passage about Till’s aspirations in his 2005 book Emmett Till: The Murder That Shocked the World and Propelled the Civil Rights Movement : “Like most kids, Emmett thought about his future, and he talked about becoming a motorcycle cop or a professional baseball player. Devery Anderson.

Rippleshot
AUGUST 2, 2019
The sheer scope of this incident shows how the fallout from this breach could be unknown for years: “Consumers and small businesses who applied for Capital One credit cards from 2005 through early 2019 are most at risk,” the company revealed. The mainstream media highlighted the core of what everyone should know about the breach itself:

The Last Watchdog
MARCH 9, 2020
Security information and event management systems — SIEMs — have been around since 2005, but their time may have come at last. Related: Digital Transformation gives SIEMs a second wind After an initial failure to live up to their overhyped potential, SIEMs are perfectly placed to play a much bigger role today.

Security Affairs
SEPTEMBER 4, 2021
. “For example, the SEC brought a number of enforcement actions against individuals and companies who made false and misleading statements about alleged business opportunities in light of damage caused by Hurricane Katrina in 2005. ” reads the alert published by SEC.

Imperial Violet
AUGUST 25, 2021
The 2005 edition changed that to be ISO/IEC 8859-1 (i.e. One thing to note is that the QR spec (ISO/IEC 18004:2005) has a whole section on “structured append” mode, where multiple QR codes can be combined into one. But you probably need to work with a variety of decoders.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content