Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.

 tag crypto
tag crypto 
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.

Security Affairs
MARCH 13, 2022
March 8 – Google TAG: Russia, Belarus-linked APTs targeted Ukraine. Google TAG observed Russian, Belarusian, and Chinese threat actors targeting Ukraine and European government and military orgs. March 7 – Coinbase blocked 25,000 crypto addresses linked to Russian individuals and entities.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
AUGUST 6, 2023
Rapid7 found a bypass for the recently patched actively exploited Ivanti EPMM bug Russian APT29 conducts phishing attacks through Microsoft Teams Hackers already installed web shells on 581 Citrix servers in CVE-2023-3519 attacks Zero-day in Salesforce email services exploited in targeted Facebook phishing campaign Burger King forgets to put a password (..)

Security Affairs
MARCH 13, 2022
Government Multiple Russian government websites hacked in a supply chain attack Anonymous hacked Russian cams, websites, announced a clamorous leak HP addressed 16 UEFI firmware flaws impacting laptops, desktops, PoS systems Samsung data breach: Lapsus$ gang stole Galaxy devices’ source code Microsoft March 2022 Patch Tuesday updates fix 89 vulnerabilities (..)

IT Governance
DECEMBER 8, 2022
Over the weekend, a verified account posing as FTX founder SBF posted dozens of copies of this deepfake video offering FTX users “compensation for the loss” in a phishing scam designed to drain their crypto wallets pic.twitter.com/3KoAPRJsya — Jason Koebler (@jason_koebler) November 21, 2022.
Security Affairs
MAY 7, 2020
The first information tag “ prog.params ” is immediately retrieved in the instruction “ HandlerParams.Start() ” seen in Figure 4. The malware tries to find the id of the mutex, declared inside the relative tag seen in code snippet 2, inside the “%TEMP%” folder. Figure 7: Check of a previous infection. Conclusion.
Krebs on Security
JULY 25, 2023
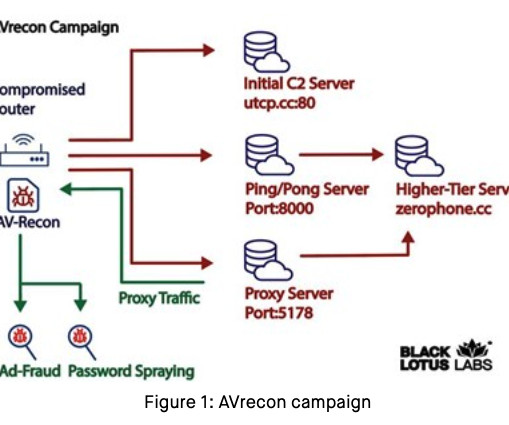
Spur.us , a startup that tracks proxy services, told KrebsOnSecurity that the Internet addresses Lumen tagged as the AVrecon botnet’s “Command and Control” (C2) servers all tie back to a long-running proxy service called SocksEscort. SocksEscort[.]com com , is what’s known as a “SOCKS Proxy” service. .”
Let's personalize your content