Audio Blog: How does social media impact getting a job?
Architect Security
MARCH 21, 2018
Today on the blog, we discuss: How does social media impact getting a job? Find out more at my sister-site, IncreaseYourSecurity.org.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 media media-blog
media media-blog 
Architect Security
MARCH 21, 2018
Today on the blog, we discuss: How does social media impact getting a job? Find out more at my sister-site, IncreaseYourSecurity.org.
Krebs on Security
APRIL 10, 2024
The domain mentioned at the beginning of this story — fedetwitter.com — redirects users to the blog of a Japanese technology enthusiast. The domain setwitter.com, which Twitter/X until very recently rendered as “sex.com,” redirects to this blog post warning about the recent changes and their potential use for phishing.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Krebs on Security
NOVEMBER 2, 2021
” In the first week of September, Groove posted on its darknet blog nearly 500,000 login credentials for customers of Fortinet VPN products, usernames and passwords that could be used to remotely connect to vulnerable systems. Sometime in the last week, Groove’s darknet blog disappeared. Maybe sell it? government interests.

OpenText Information Management
FEBRUARY 21, 2024
However, it remains challenging to manage the increasing volume and complexity of rich media that organizations and individuals create and consume. Whether it is new formats, like 3D models, new channels, like social short-form video, or new … The post What’s new in OpenText Media Management appeared first on OpenText Blogs.

Hunton Privacy
FEBRUARY 21, 2024
On February 12, 2024, a federal court in the Southern District of Ohio issued an order granting a Motion for a Preliminary Injunction, prohibiting the Ohio Attorney General from implementing and enforcing the Parental Notification by Social Media Operators Act, Ohio Rev. Code § 1349.09(B)(1) B)(1) (the “Act”).

Security Affairs
MAY 21, 2022
The media company Nikkei has disclosed a ransomware attack and revealed that the incident might have impacted customer data. The Japanese-based media company Nikkey is focused on the business and financial industry, it is the world’s largest financial newspaper. To nominate, please visit:? Pierluigi Paganini.
Krebs on Security
FEBRUARY 4, 2021
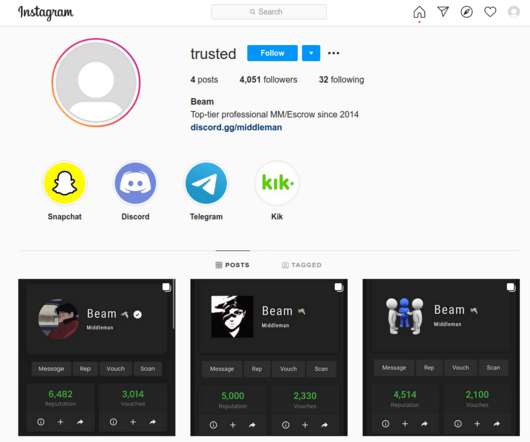
At the center of the account ban wave are some of the most active members of OGUsers , a forum that caters to thousands of people selling access to hijacked social media and other online accounts. “ Amp ,” a major middleman and account seller on OGUusers.
Security Affairs
APRIL 17, 2023
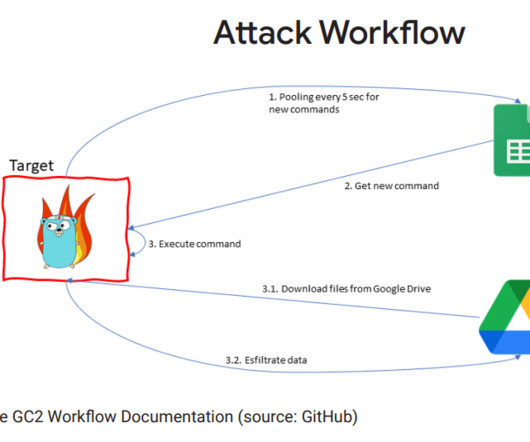
China-linked APT41 group used the open-source red teaming tool GC2 in an attack against a Taiwanese media organization. Google Threat Analysis Group (TAG) team reported that the China-linked APT41 group used the open-source red teaming tool Google Command and Control ( GC2 ) in an attack against an unnamed Taiwanese media organization.

Krebs on Security
JULY 26, 2021
Justice Department last week announced O’Connor’s arrest and indictment, his alleged role in the Twitter compromise was well covered in the media. Once inside, the attackers found nude photos of Thorne, which they then threatened to release unless she agreed to post on social media thanking the hackers using their online handles.

OpenText Information Management
SEPTEMBER 1, 2020
This blog is co-authored by Annie John and Todd Cernetic. Not that long-ago, social media was the “new kid on the block,” something we used to share photos with distant family members, comment … The post Is social media being mined for insider threats? appeared first on OpenText Blogs.
Data Matters
JUNE 17, 2022
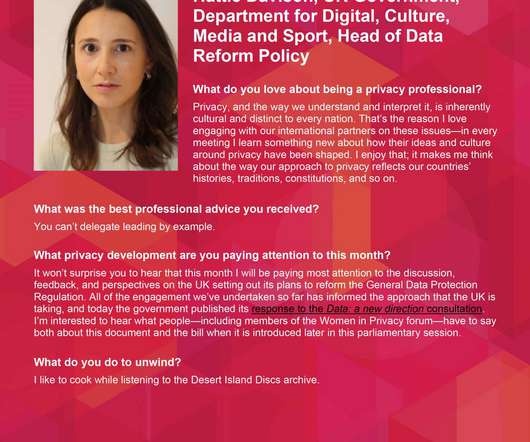
Hattie Davison, UK Government, Department for Digital, Culture, Media and Sport, Head of Data Reform Policy. The post Spotlight on Women in Privacy – Hattie Davison appeared first on Data Matters Privacy Blog.

Krebs on Security
JUNE 27, 2023
On July 16, 2020 — the day after some of Twitter’s most recognizable and popular users had their accounts hacked and used to tweet out a bitcoin scam — KrebsOnSecurity observed that several social media accounts tied to O’Connor appeared to have inside knowledge of the intrusion. I haven’t done anything.”

Data Matters
NOVEMBER 23, 2022
States and Congress have been enacting or debating different approaches to online “content moderation” by social media and other internet platforms. In short, AB 587 requires social media companies to disclose their processes to take down or manage content and users on their platforms.

OpenText Information Management
JANUARY 11, 2024
Billions of rich media assets are created every day for new and emerging channels. With all this creative, consistency is a challenge that goes right to the bottom line.

AIIM
MAY 25, 2021
Many self-proclaimed experts will develop and manage social media profiles, such as personal blogs, LinkedIn profiles, and profiles on other public and private social media services. We can also leverage analytics to analyze email traffic or social media traffic.
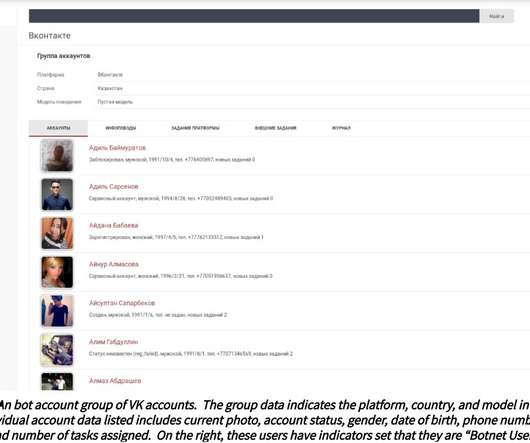
Security Affairs
MAY 23, 2022
The botnet provides a web-based dashboard known as SANA that allows operators to spread trending social media events, called ‘newsbreaks,’ en masse. SANA allows operators to create and manage fake social media persona accounts. .” reads the analysis published by the security firm NISOS. ” continues the report.

Security Affairs
MAY 6, 2022
No eyebrows were raised in Quriums security operation center when the independent Philippine media outlet Bulatlat once again got DDoSed , as they are a frequent target of such digital attacks. The post How the thriving fraud industry within Facebook attacks independent media appeared first on Security Affairs. Pierluigi Paganini.

IBM Big Data Hub
FEBRUARY 12, 2024
How we arrived at this CX environment Early days of retail Before mass media, it was harder to know what other products were available outside of the ones offered by the local store. This means organizations need to devote more resources to improving their SEO, mobile apps and social media presences.

Data Breach Today
DECEMBER 18, 2019
Tips From a Cybersecurity Veteran on Winning the Battle In this in-depth blog, a long-time cybersecurity specialist who recently joined the staff of Information Security Media Group sizes up evolving ransomware risks and offers a list of 11 critical mitigation steps.

OpenText Information Management
APRIL 25, 2022
Maybe you are considering moving from OpenTextTM MediaBin to OpenTextTM Media Management (OTMM) but you’re not sure where to start? My recommendation would be to firstly understand the potential benefits to your organization of migrating to OpenText Media Management.

Data Matters
FEBRUARY 15, 2024
Indeed, over the past year, legislative forums, editorial pages, and social media platforms were dominated by AI discourse. Plans to ‘Lead the Way’ on Global AI Policy appeared first on Data Matters Privacy Blog. The post The U.S.

Security Affairs
APRIL 5, 2023
“Nexx has not replied to any correspondence from myself, DHS (CISA and US-CERT) or VICE Media Group.” The expert attempted to report the flaws to Nexx, but the company has never replied to the reports. ” reads a post published by Sabetan. Authorization Bypass Through User-Controlled Key CWE-639 ( CVE-2023–1749 , CVSS3.0:
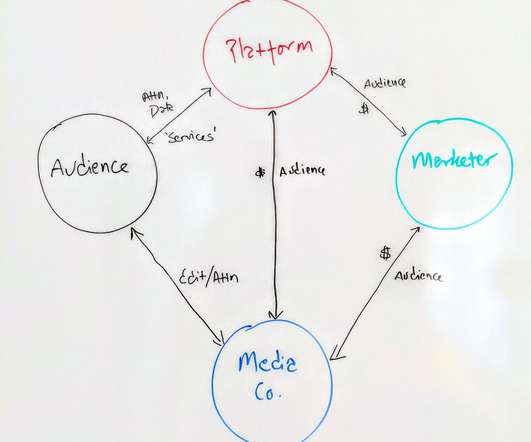
John Battelle's Searchblog
JUNE 17, 2020
It’s time to rethink the relationship between marketers, media companies (not “content creators,” ick), and the audience. I’m heading into a bit of media theory for the next couple thousand words – I hope this will start an interesting conversation. The Old Media Model. More on that later on.

John Battelle's Searchblog
APRIL 7, 2022
We believe we are innovating, but in fact, we’re making the same mistakes old school media companies made when faced with the rise of the internet 15 years ago. In short, we know we must deliver an experience that builds community – because no media brand thrives without community. .
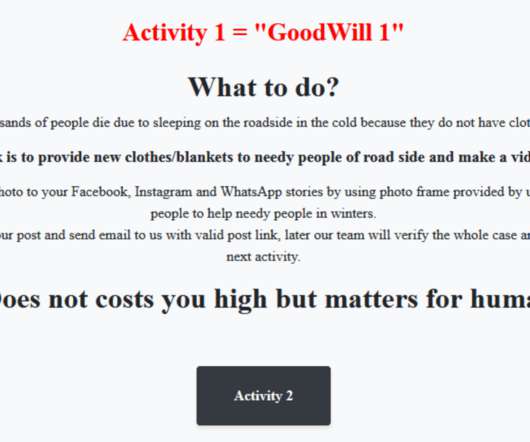
Security Affairs
MAY 30, 2022
Victims have to donate new clothes to the homeless, record their action, and post it on social media. In addition, the victims can accompany less fortunate children to Dominos, Pizza Hut or KFC for a treat, take pictures and videos, and post them on social media. said the researchers. said the researchers. To nominate, please visit:?.

Security Affairs
APRIL 21, 2022
A critical RCE flaw in Android devices running on Qualcomm and MediaTek chipsets could allow access to users’ media files. “In addition, an unprivileged Android app could use these vulnerabilities to escalate its privileges and gain access to media data and user conversations.” To nominate, please visit:?
Security Affairs
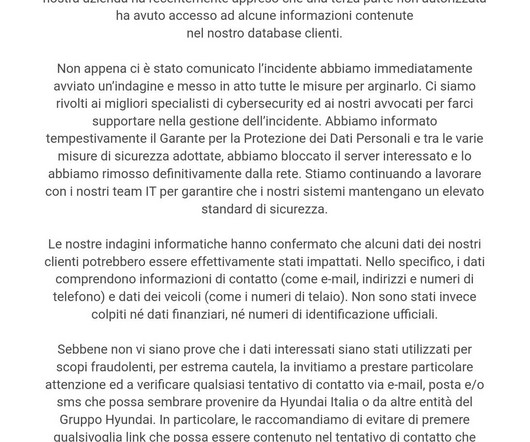
APRIL 12, 2023
In December 2019, German media reported that hackers suspected to be members of the Vietnam-linked APT Ocean Lotus ( APT32 ) group breached the networks of the car manufacturers BMW and Hyundai. The intrusion aimed at stealing automotive trade secrets.

Security Affairs
APRIL 20, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, vRealize ) The post VMware fixed a critical flaw in vRealize that allows executing arbitrary code as root appeared first on Security Affairs.
Security Affairs
APRIL 6, 2023
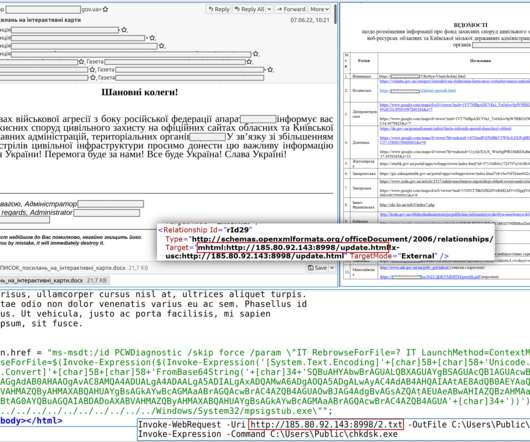
The messages pose as sent by a representative of a media outlet or think tank and ask North Korea experts to participate in a media interview or request for information (RFI). The attack chain associated with ARCHIPELAGO starts with phishing emails that embed malicious links.

IBM Big Data Hub
DECEMBER 13, 2023
Read the blog: How generative AI is transforming customer service Customer service types that organizations should prioritize By offering different types of customer service and several customer support channels, organizations demonstrate they are investing in customer care.

Security Affairs
APRIL 25, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, VMware ) The post VMware addressed two zero-day flaws demonstrated at Pwn2Own Vancouver 2023 appeared first on Security Affairs.
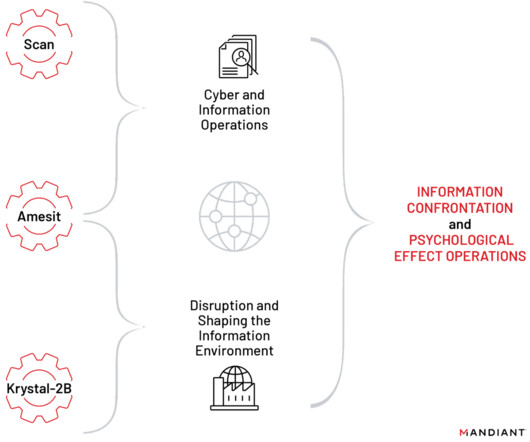
Security Affairs
APRIL 2, 2023
A joint research conducted by Mandiant with a collective of media outlets (including Papertrail Media, Der Spiegel, Le Monde, and Washington Post) focused on documents, dated between 2016 and 2020, belonging to NTC Vulkan (Russian: НТЦ Вулкан).
Security Affairs
JUNE 13, 2022
Nation-state actors are targeting media organizations in Ukraine, including radio stations, and newspapers. Targeting media orgs. sections “The Underdogs – Best Personal (non-commercial) Security Blog” and “The Tech Whizz – Best Technical Blog”). CERT-UA also shared indicators of compromise for these attacks.

Security Affairs
MARCH 31, 2021
Researchers from Google’s Threat Analysis Group (TAG) reported that North Korea-linked hackers are targeting security researchers via social media. The cyberspies used fake Twitter and LinkedIn social media accounts to get in contact with the victims. ” reads the post published by Google TAG.

IBM Big Data Hub
AUGUST 28, 2023
With nearly 5 billion users worldwide—more than 60% of the global population —social media platforms have become a vast source of data that businesses can leverage for improved customer satisfaction, better marketing strategies and faster overall business growth. words and/or phrases) known as tokens.
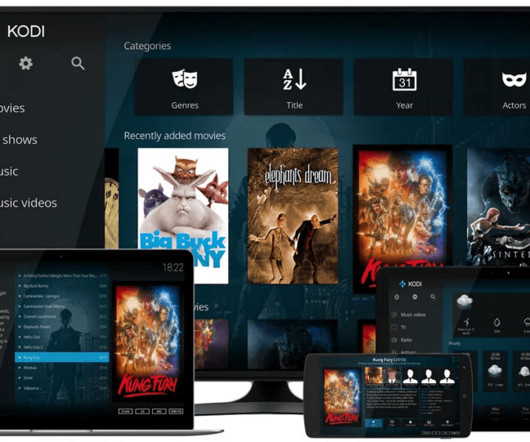
Security Affairs
APRIL 14, 2023
Open-source media player software provider Kodi discloses a data breach after threat actors stole its MyBB forum database. Kodi has disclosed a data breach, threat actors have stolen the company’s MyBB forum database that contained data for over 400K users and private messages.

OpenText Information Management
DECEMBER 9, 2020
Dealing with the scale and complexity of evidence in rich-media formats (images, video and audio) is one of the key challenges in evidence management for law enforcement and security organizations today. With the ubiquity of mobile devices, people are creating more content than ever.

IT Governance
JUNE 24, 2019
A version of this blog was originally published on 19 June 2017. But all that activity has made social media a breeding ground for a new form of cyber attack known as angler phishing. Angler phishing is a specific type of phishing attack that exists on social media. Many social media users know very little about angler phishing.

Security Affairs
APRIL 13, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, Hikvision ) The post Hikvision fixed a critical flaw in Hybrid SAN and cluster storage products appeared first on Security Affairs.

Security Affairs
APRIL 12, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, April security updates) The post SAP April 2023 security updates fix critical vulnerabilities appeared first on Security Affairs.

Security Affairs
APRIL 10, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, Sophos) The post Sophos patches three issues in the Sophos Web Security appliance, one of them rated as critical appeared first on Security Affairs.
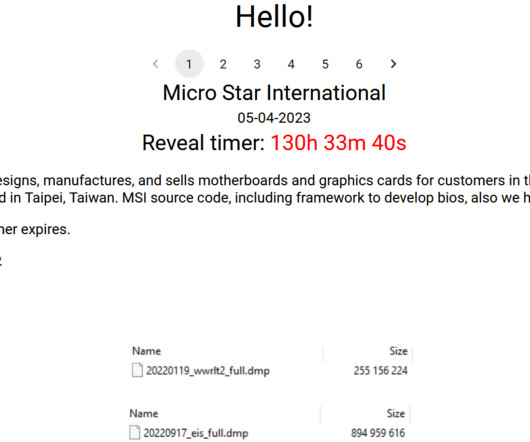
Security Affairs
APRIL 6, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, MSI) The post Money Message ransomware group claims to have hacked IT giant MSI appeared first on Security Affairs.

IBM Big Data Hub
APRIL 25, 2024
This era was defined by massive online marketplaces like Amazon, ecommerce platforms such as eBay, and consumer-to-consumer transactions conducted on social media platforms like Facebook marketplace.

National Archives Records Express
MAY 15, 2023
Welcome to the first in a series of blog posts on the new rule for digitizing federal records. This includes most types of paper-based documents, like text documents, maps, posters, and photographs, but it doesn’t cover other types of media like film or audio tapes.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content