Change Healthcare Outage Hits Military Pharmacies Worldwide
Data Breach Today
FEBRUARY 23, 2024
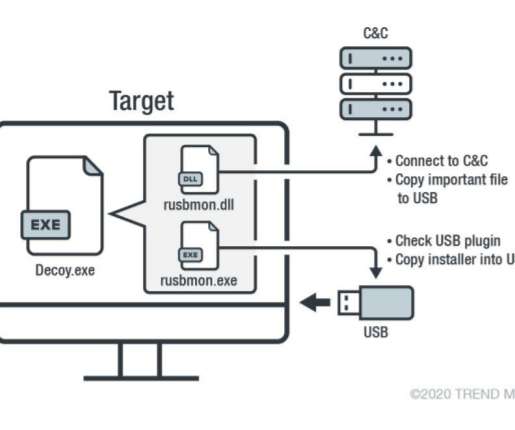
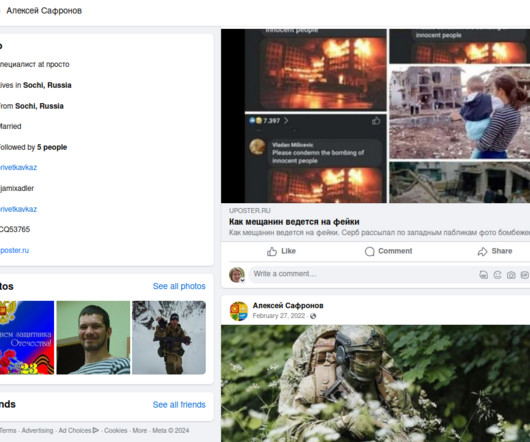
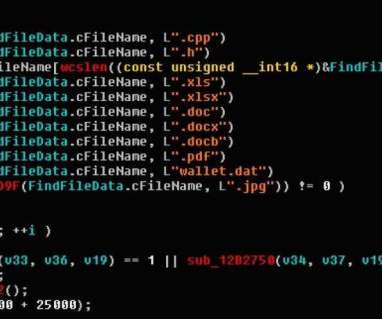
military hospitals and clinics worldwide are among the entities affected by the cyberattack on Optum's Change Healthcare this week, which has forced the IT services company to take many of its applications offline. Experts Speculate About Whether the Hack Involved the ScreenConnect Flaw Exploit Pharmacies at U.S.





































Let's personalize your content