Breach at Hy-Vee Supermarket Chain Tied to Sale of 5M+ Stolen Credit, Debit Cards
Krebs on Security
AUGUST 22, 2019
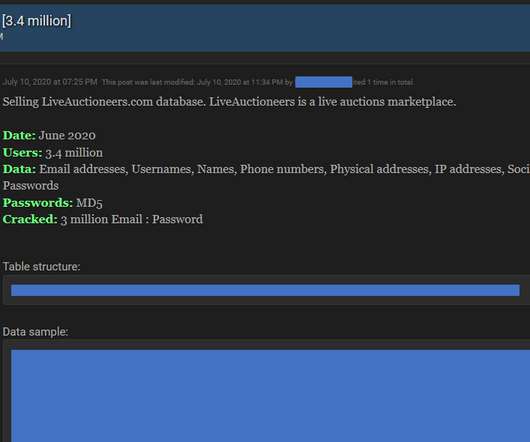
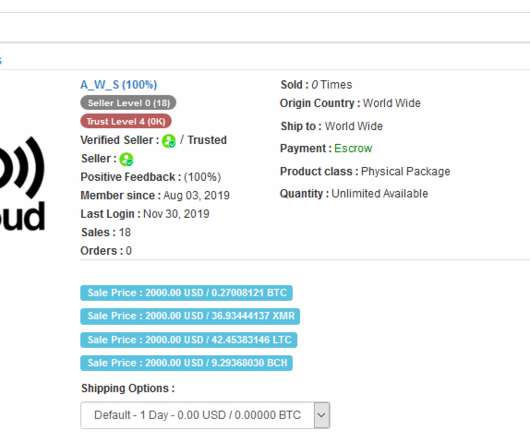
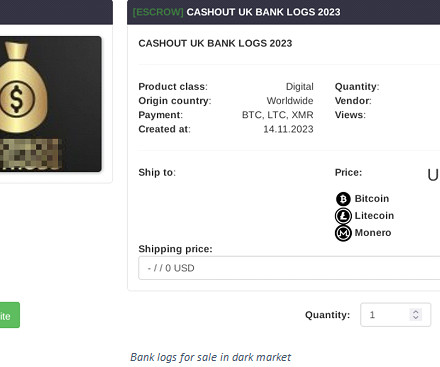
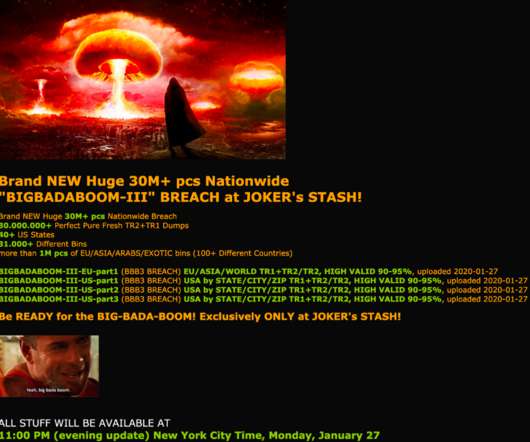
On Tuesday of this week, one of the more popular underground stores peddling credit and debit card data stolen from hacked merchants announced a blockbuster new sale: More than 5.3 “This encryption technology protects card data by making it unreadable. . million new accounts belonging to cardholders from 35 U.S.




































Let's personalize your content