Security Compliance & Data Privacy Regulations
eSecurity Planet
AUGUST 9, 2022
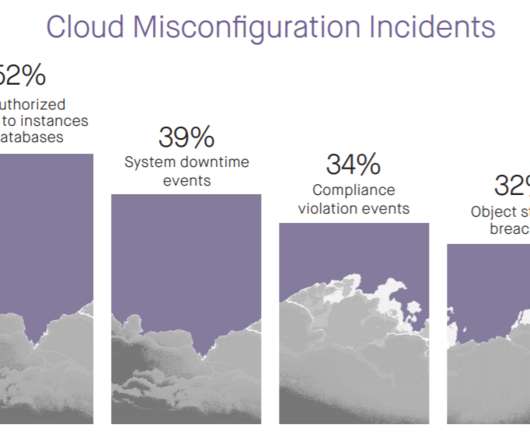
Regulatory compliance and data privacy issues have long been an IT security nightmare. GDPR (among other legal requirements in the EU and elsewhere) can expose multinational organizations to hefty financial penalties, additional rules for disclosing data breaches, and increased scrutiny of the adequacy of their data security.











































Let's personalize your content