Don’t Let Zombie Zoom Links Drag You Down
Krebs on Security
OCTOBER 2, 2023
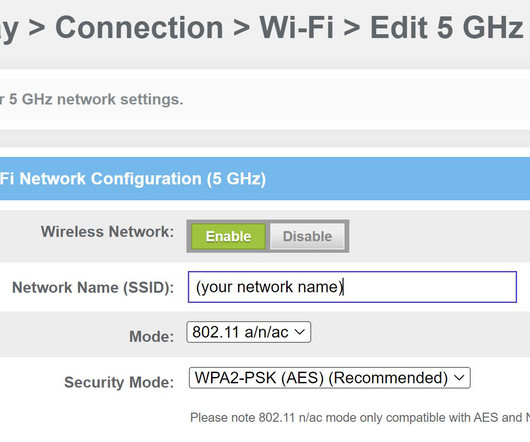
Many organizations — including quite a few Fortune 500 firms — have exposed web links that allow anyone to initiate a Zoom video conference meeting as a valid employee. The PMI portion forms part of each new meeting URL created by that account, such as: zoom.us/j/5551112222










































Let's personalize your content